Connecting to the internet exposes your personal IP address to every website you visit. A proxy prevents this by processing requests on your behalf.
If you are wondering what is a proxy server, it is simply an intermediary system for your web traffic. It hides your identity, unlocks restricted content, and controls network access.
This article explains the technical mechanics of proxy technology. Read on to explore the various proxy types and find the exact solution for your specific use cases.
Key takeaways:
- A proxy server acts as an intermediary gateway that masks your IP address to provide online anonymity and bypass geographical restrictions.
- There are various types of proxies available, such as residential and datacenter proxies, each tailored for specific needs like web scraping or streaming.
- While effective for accessing blocked content, most proxies do not encrypt traffic like VPNs, leaving sensitive data potentially exposed to interception.
- Using free or unreliable proxies involves significant risks, including malicious data logging, identity theft, and slower connection speeds.
- The choice between a proxy and a VPN depends on whether you prioritize high-speed application-specific tasks or comprehensive system-wide security.
1. What is a proxy server?
Proxy servers act as gateways between users and the Internet. It acts as an intermediary system separating end users from the websites they browse.
While we often think of proxies as software, they exist in two physical forms:
- Hardware proxy: A physical device placed between your network and the internet. These are robust and handle heavy traffic loads for large enterprises, but are expensive to maintain.
- Software proxy: An application hosted by a provider or on the cloud. These are the standards for most modern users and businesses because they are flexible, scalable, and easier to manage remotely.
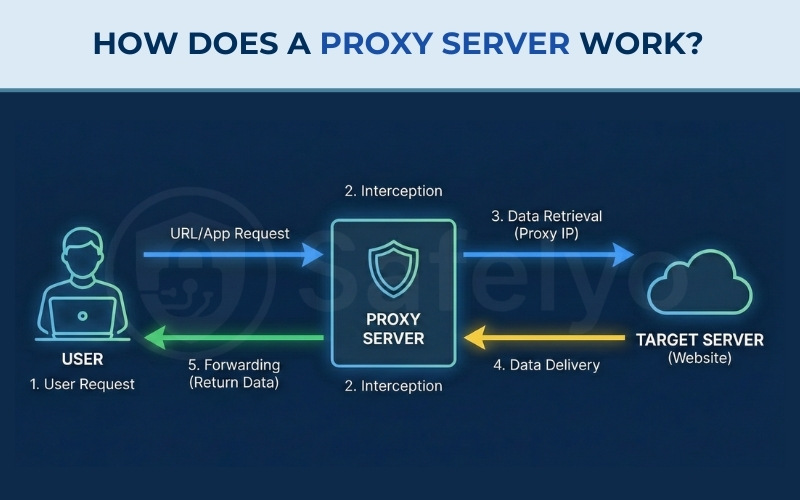
2. How does a proxy server work?
Functionally, a proxy server has its own IP address that your computer connects to. This setup ensures that the destination server communicates with the proxy rather than directly with your device.
This system creates an intermediate layer to manage data and modify online requests. Here is the step-by-step flow of how a proxy handles your traffic:
- User request: You type a URL or make a request from an app.
- Proxy interception: The request goes to the proxy server instead of directly to the website.
- Data retrieval: The proxy forwards the request to the target server (e.g., a website) using its own IP address.
- Data delivery: The target server responds to the proxy.
- Forwarding: The proxy returns the data to your browser.
3. History and evolution of proxy technology
Proxy servers originated in the early days of the Internet as caching tools to speed up content delivery on corporate networks. In the 1990s, web proxies became popular for shared Internet access and security filtering.
Over time, the technology evolved to include:
- Transparent proxies for content filtering in schools and libraries
- Anonymous and elite proxies for privacy seekers
- Reverse proxies are used by major web platforms for performance and load balancing
- Rotating and residential proxies are adopted by marketers and developers for large-scale data scraping and account management
4. Types of proxy servers and how they differ
Once you’ve grasped what a proxy server is, it’s important to explore the many types that exist.
Proxy servers come in many forms, each designed for specific levels of privacy, performance, or use cases. Whether you’re hiding your location or balancing web traffic, the type of proxy you choose matters.
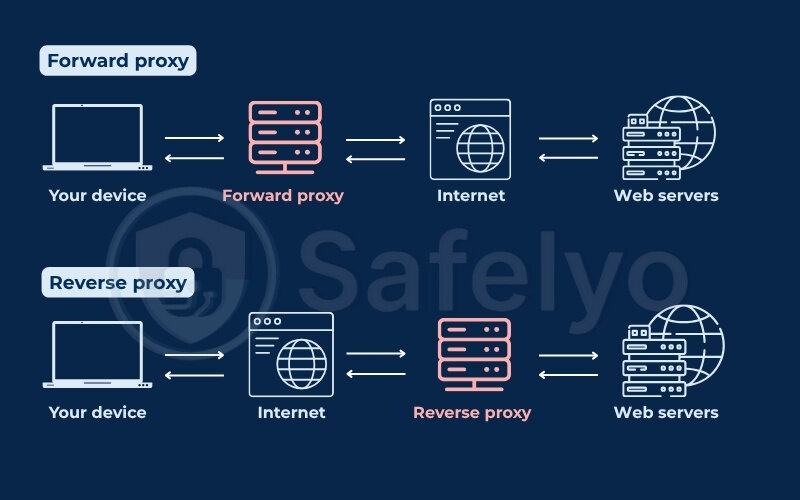
4.1. By role: Forward proxy and reverse proxy
Proxy servers can be classified by their network role, either acting on behalf of the client (forward proxy) or the server (reverse proxy).
4.1.1. Forward proxy
A forward proxy sits between the user and the Internet. It processes outbound requests, hides the user’s IP address, and can enforce access rules.
Key functions:
- Hides client identity
- Filters content and blocks websites
- Bypasses geo-restrictions
Use case:
Individuals use forward proxies to browse anonymously or access blocked content. Organizations use them to monitor or restrict employee access.
You may be interested in this article: How to browse the web anonymously: A 4-step guide
4.1.2. Reverse proxy
A reverse proxy sits in front of web servers and handles incoming requests. Clients connect to the proxy, which then forwards requests to the appropriate backend server.
Expanded functions:
- Load balancing: Distributes incoming traffic across multiple servers to prevent crashes.
- Web application firewall (WAF): Inspects incoming traffic to block malicious attacks like SQL injection and cross-site scripting (XSS) before they reach the server.
- Content delivery network (CDN): Caches content on servers geographically closer to the user to reduce latency and speed up page loading times.
Use case:
Businesses use reverse proxies to distribute traffic and protect internal infrastructure from direct exposure.
Here’s a quick overview about type of proxy by role:
| Type | Forward proxy | Reverse proxy |
|---|---|---|
| Sits between | Client and Internet | Internet and Server |
| Controls | Outbound traffic | Inbound traffic |
| Used by | Individuals, schools, offices | Enterprises, platforms, hosting |
| Purpose | Anonymity, filtering, access | Security, WAF, CDN, load distribution |
4.2. By anonymity level: Transparent, anonymous, high anonymity, and distorting
Proxy servers offer different levels of privacy based on how much information they reveal to the websites you visit. Some show your real IP address, while others fully hide your identity and even make the website record a different location.
4.2.1. Transparent proxy
A transparent proxy does not hide your identity. It passes your real IP address to the website and also tells the website that it’s a proxy.
- How it works: When you access a website, the request goes through the proxy. But the website can still see who you are and knows you’re using a proxy.
- Purpose: Used by schools, offices, and public Wi-Fi networks to monitor or filter content without needing user permission.
- Privacy level: No privacy. Your real IP is exposed.
4.2.2. Anonymous proxy
An anonymous proxy hides your real IP address, so websites can’t see where the request originally came from. However, it does identify itself as a proxy.
- How it works: The proxy replaces your IP with its own, but tells the website, “This is a proxy server.”
- Purpose: Used when users want basic online privacy, like avoiding tracking cookies or IP-based ads.
- Privacy level: Moderate. Your IP is hidden, but the site knows you’re using a proxy.
4.2.3. High anonymity (elite) proxy
A high anonymity proxy, also called an elite proxy, offers the highest level of privacy. It hides your IP and also does not reveal that it’s a proxy.
- How it works: The proxy fully masks your identity. The target website sees the proxy’s IP and assumes it’s a real user, not a proxy.
- Purpose: Used for maximum anonymity, avoiding IP bans, or accessing sensitive services without being tracked.
- Privacy level: Very high. Most secure and private option.
4.2.4. Distorting proxy
A distorting proxy hides your real IP but intentionally sends a fake IP address to the website. It also reveals itself as a proxy.
- How it works: The proxy replaces your IP with a false one, often from a different country, and tells the website it’s a proxy.
- Purpose: Used to bypass geo-blocks or trick regional filters.
- Privacy level: Variable. It hides your real IP but is not fully anonymous due to proxy detection.
Here’s a quick overview about type of proxy by anonymity level:
| Proxy type | Hides real IP | Reveals it’s a proxy | Sends fake IP | Privacy level | Best for |
|---|---|---|---|---|---|
| Transparent | No | Yes | No | Low | Web filtering in schools, cafes |
| Anonymous | Yes | Yes | No | Moderate | Basic privacy, avoiding IP tracking |
| High anonymity | Yes | No | No | Very high | Secure browsing, managing accounts |
| Distorting | Yes | Yes | Yes | Variable | Geo-spoofing, bypassing restrictions |
4.3. By origin: Residential proxy, datacenter proxy, and public vs. private proxy
Proxies can also be categorized by where the IP address comes from, whether it’s a real home device or a server in a data center. This affects how trustworthy and detectable the proxy is to websites.
4.3.1. Residential proxy
A residential proxy uses an IP address assigned to a real person’s home by an Internet service provider (ISP). This makes it look like the traffic is coming from a real human user.
- How it works: When you connect through a residential proxy, your traffic is routed through someone’s actual home Internet connection.
- Purpose: Best for avoiding detection, bypassing anti-bot systems, or accessing geo-restricted content.
Pros
- Harder to detect and block
- Looks like normal user traffic
- Good for sneaker bots, ad verification, and scraping
Cons
- Slower speed
- More expensive
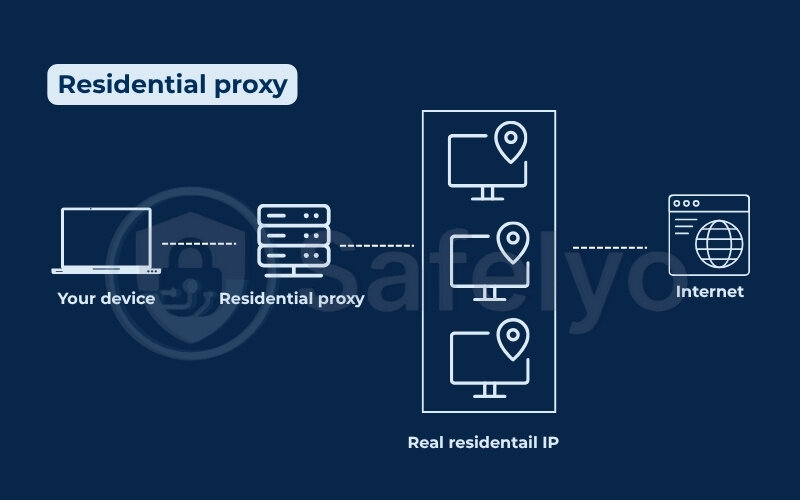
Streaming platforms like Netflix and Disney+ have advanced their detection systems, meaning standard datacenter proxies are now frequently blocked. Consequently, residential proxies have become a more reliable method to bypass these strict “VPN/Proxy Detected” errors, as they mimic legitimate home user connections.
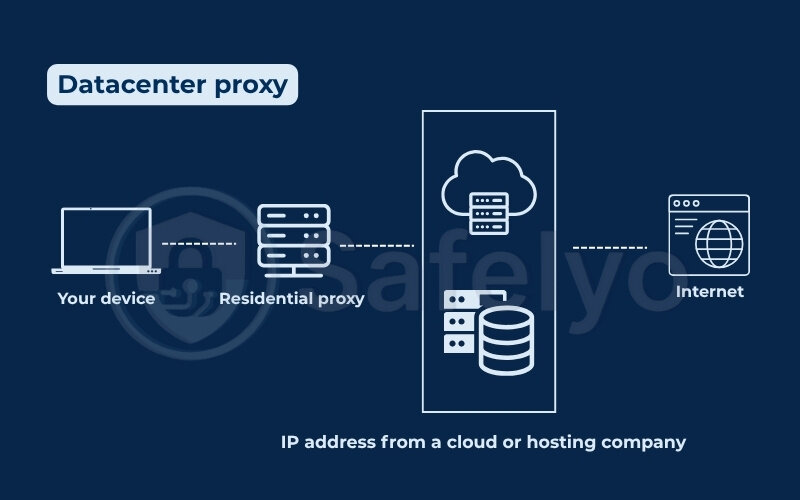
4.3.2. Datacenter proxy
A datacenter proxy uses an IP address from a cloud or hosting company, not from a real home. It’s fast and easy to create, but more likely to be detected by websites.
- How it works: Your Internet requests go through a virtual machine or server in a data center.
- Purpose: Good for speed, cost savings, and basic tasks like market research or unblocking websites.
Pros
- Fast speeds
- Cheap and scalable
- Easy to set up
Cons
- Easier for websites to detect as non-human traffic
- Can get banned or blocked on sensitive platforms
4.3.3. Public vs. private proxy
These terms describe who has access to the proxy – everyone, or just you.
Public proxy:
- Open to anyone. Anyone on the Internet can use it.
- Usually free, but often slow and risky.
- Low privacy and security.
Private proxy:
- Dedicated or semi-dedicated. Only one user or a small group has access.
- Paid and managed by a provider.
- Reliable, fast, and much safer than public options.
Here’s a quick overview about types of proxy by origin:
| Type | Real IP source | Speed | Detection risk | Best use case |
|---|---|---|---|---|
| Residential proxy | Real home user | Slower | Low | Bypassing geo-blocks, ad testing, scraping |
| Datacenter proxy | Cloud server | Fast | Higher | Web scraping, automation, non-sensitive use |
| Public proxy | Any device | Very slow | Very high | Not recommended (too risky) |
| Private proxy | Controlled IP | Fast | Low | Secure browsing, business tools |
4.4. By function: Web proxy, CGI proxy, rotating proxy, DNS proxy, SSL proxy, and SOCKS proxy
Proxies can also be classified based on what specific tasks they perform. Some are designed for browsing websites, others for managing traffic or bypassing firewalls. Here are the main types based on function:
4.4.1. Web proxy
A web proxy is used through a browser, usually by visiting a website that lets you enter a URL to access another site.
- How it works: You don’t need to install anything. Just go to a web proxy site, type in the address you want to visit, and the proxy fetches the content for you.
- Use case: Useful for quickly accessing blocked websites or browsing anonymously on public computers.
- Limitations: Often slow, limited to web browsing, and may break page formatting or scripts.
4.4.2. CGI proxy
A CGI (Common Gateway Interface) proxy is a type of web proxy that runs on a website using server-side scripts to fetch and show content.
- How it works: Similar to a basic web proxy, but uses CGI scripts (like PHP or Perl) to process your requests.
- Use case: Used when you want to hide browsing activity without changing browser or system settings.
- Limitations: Limited performance and compatibility with modern websites.
4.4.3. Rotating proxy
A rotating proxy automatically switches between different IP addresses at set intervals or with each request.
- How it works: Each connection you make is routed through a different proxy server or IP address, making it harder to track or block you.
- Use case: Ideal for web scraping or managing multiple accounts.
- Benefit: Reduces the chance of being detected or banned.
4.4.4. DNS proxy
A DNS proxy intercepts and forwards DNS requests (used to translate website names into IP addresses).
- How it works: Instead of connecting directly to a DNS server, your request goes through a proxy that can filter or reroute it.
- Use case: Used for content filtering, blocking specific websites, or parental controls.
- Limitation: It only affects domain name resolution, not full traffic routing.
4.4.5. SSL proxy
An SSL proxy decrypts and inspects secure HTTPS traffic between client and server.
- How it works: It acts as an intermediary, decrypting the encrypted traffic so it can be monitored or filtered before re-encrypting it and sending it to the destination.
- Use case: Common in corporate environments for monitoring or enforcing policies on encrypted traffic.
- Privacy warning: It can inspect sensitive information like passwords, so it must be used carefully and ethically.
4.4.6. SOCKS proxy
A SOCKS (Socket Secure) proxy works at a lower level, handling all kinds of traffic, not just web browsing.
- How it works: It passes data packets between the client and server regardless of protocol (HTTP, FTP, email, etc.).
- Use case: Great for torrents, gaming, or apps that aren’t just browsing websites.
- SOCKS5 version: Supports authentication and works better with firewalls and modern security protocols.
4.4.7. Suffix proxy
A suffix proxy adds the proxy server’s name to the end of a URL to bypass basic firewall filters. While simple to use, modern security systems are easy to detect and block.
4.4.8. Tor onion proxy
A Tor onion proxy routes your traffic through multiple encrypted layers (nodes) around the world. It provides extremely high anonymity but is significantly slower than standard proxies, making it suitable for privacy enthusiasts rather than streaming or gaming.
Here’s a quick overview about type of proxy by function:
| Proxy type | How it works | Use case | Limitations / Notes |
|---|---|---|---|
| Web proxy | Access sites via a browser-based proxy page. | Bypass blocks on public/shared computers. | Slow, web-only, may break page layout. |
| CGI proxy | Uses server-side scripts (e.g., PHP) to fetch content. | Private browsing without system changes. | Limited performance, poor compatibility. |
| Rotating proxy | Switches IPs automatically per request/time. | Web scraping, multi-account management. | Needs reliable service to avoid detection. |
| DNS proxy | Filters or redirects DNS requests. | Content filtering, parental control. | Affects domains only, not full traffic. |
| SSL proxy | Decrypts and inspects HTTPS traffic (MITM). | Corporate traffic monitoring. | Privacy risks; use ethically. |
| SOCKS proxy | Relays all traffic types at lower level (SOCKS5 supports auth). | Torrents, gaming, non-web apps. | No encryption unless paired with VPN. |
| Suffix proxy | Appends proxy name to URL. | Bypassing simple filters. | Easy to detect and block. |
| Tor onion proxy | Routes traffic through multiple encrypted layers. | High anonymity. | Very slow speed. |
5. Modern cloud security architectures (SASE & SSE)
In modern cloud security, the concept of a proxy has evolved beyond simple IP masking into comprehensive platforms that secure remote work. While often used interchangeably, there is a distinct difference between SSE and SASE.
- Security service edge (SSE): This represents the security pillar of SASE. It unifies secure web gateways (SWG), cloud access security brokers (CASB), and Zero Trust Network Access (ZTNA) into one cloud service. It inspects traffic to block threats and control data, but it does not manage the physical network connection.
- Secure access service edge (SASE): SASE is the complete package. It combines SSE (security) with SD-WAN (networking). It uses cloud proxies to secure traffic and optimize the network path. This ensures remote employees access corporate apps quickly without a traditional VPN.
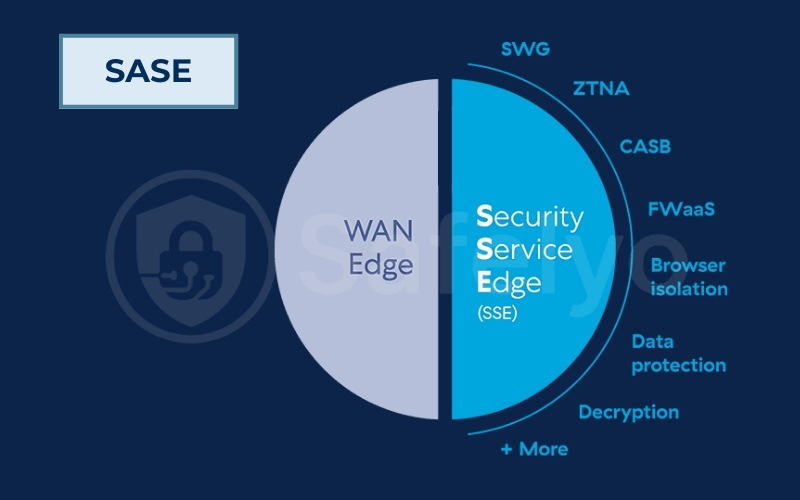
Real-world examples: When to use which?
- Use SSE when: You want to secure remote access to SaaS applications (like Microsoft 365 or Salesforce) but you are happy with your current network setup (SD-WAN).
- Example: A company wants to prevent remote employees from downloading sensitive data to personal devices but doesn’t want to rip and replace their existing network routers.
- Use SASE when: You need to transform both security and networking connectivity, typically to replace expensive MPLS lines.
- Example: A global retailer wants to connect 500 branch stores directly to the cloud. They need SASE to optimize the connection speed (SD-WAN) while ensuring every byte of traffic is inspected for malware (SSE) in a single platform.
6. Common protocols used by proxy servers
Proxy servers rely on specific network protocols to handle, transmit, and secure data between the client and the destination server. Understanding “what is a proxy server” and these protocols helps users choose the right proxy setup for privacy, speed, and compatibility.
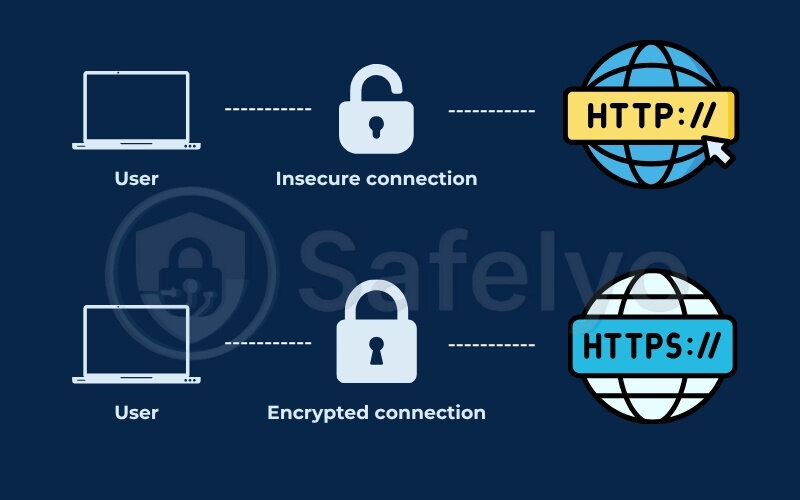
6.1. HTTP and HTTPS
HTTP (Hypertext Transfer Protocol) and HTTPS (HTTP Secure) are the most common protocols used by proxies for browsing websites.
- HTTP proxy: Routes traffic for unencrypted websites. It’s fast but not secure; any data sent can be seen by the proxy or others on the network.
- HTTPS proxy: Handles encrypted traffic by routing through an SSL connection. It allows secure browsing without revealing your data to the proxy server.
- Use case: Basic browsing, content filtering, and caching. HTTPS is a must for handling sensitive data like passwords or payment info.
6.2. SOCKS and SOCKS5
SOCKS proxies work at a lower level than HTTP, forwarding all kinds of traffic, not just web browsing. SOCKS5 is an upgraded version with better security.
- SOCKS: Good for handling data from any protocol (e.g., FTP, email, torrents, apps).
- SOCKS5: Adds support for authentication and UDP (used by gaming and streaming apps), and can bypass firewalls more effectively.
- Use case: Ideal for peer-to-peer sharing, streaming, multiplayer gaming, and accessing restricted networks.
6.3. SSL/TLS proxies
An SSL/TLS proxy decrypts secure web traffic (HTTPS) for inspection before re-encrypting it and forwarding it.
- How it works: The proxy acts as an intermediary between the client and server, temporarily decrypting data to allow content filtering or monitoring.
- Use case: Often used in corporate networks to monitor employee activity or enforce data protection rules.
- Caution: Because it involves decrypting secure traffic, it can raise ethical and privacy concerns.
6.4. Smart DNS and DNS-over-HTTPS
These protocols are used more for bypassing geo-restrictions and improving DNS privacy.
- Smart DNS: Re-routes only the DNS queries related to location-based restrictions, allowing access to geo-blocked services without changing your IP.
- DNS-over-HTTPS (DoH): Encrypts DNS requests, hiding them from ISPs or local networks. It adds a privacy layer by preventing DNS snooping or manipulation.
- Use case: Useful for streaming content from other regions or protecting DNS requests from surveillance.
7. Benefits of using a proxy server
Using a proxy server provides several practical advantages for both personal and professional use. These tools are highly effective for improving online privacy, accessing restricted content, and optimizing overall network performance.
7.1. Online anonymity and IP masking
One of the most valuable benefits of using a proxy server is hiding your IP address. A major reason people use proxies is IP address masking. Your IP address identifies your device and location. A proxy hides your IP and replaces it with its own, shielding your real location from websites, apps, or trackers.
This helps:
- Maintain online anonymity
- Avoid targeted tracking
- Mask your physical location from the sites you visit.
Some proxies even rotate IPs to make traffic appear more organic or anonymous. This is helpful for avoiding IP bans, conducting secure competitor research, and running multiple accounts.
You may also like these articles:
7.2. Bypassing geo-restrictions (Gaming & streaming)
Proxies enable users to access content blocked by geography or network rules. By routing traffic through servers in allowed regions, they help:
- Unblock streaming services: Access libraries on Netflix, BBC iPlayer, or Disney+ (using residential proxies).
- Modern Gaming: Gamers on PS5, Xbox, and mobile platforms like Free Fire use proxies to access lobbies in different regions. These tools also help reduce ping or bypass network blocks on game servers.
- Bypass firewalls: Access censored websites in restrictive countries or workplace networks.
You might also like this related article: Top 5 best VPN for streaming (Tested)
7.3. Bandwidth savings and content caching
Proxies, particularly forward proxies, can store copies of frequently accessed content (Caching).
Benefits include:
- Reduced bandwidth usage
- Faster load times for repeat requests
- Lower strain on origin servers
7.4. Monitoring, filtering, and parental control
Organizations and households use proxies to monitor and control Internet usage (Content filtering). Administrators can configure proxies to block access to specific domains or types of content (common in corporate or educational networks).
- Filter inappropriate or harmful content
- Restrict access during specific hours
- Monitor browsing activity for security or compliance
Proxy servers are part of broader network perimeter defenses, especially in schools and enterprises where content control is critical.
7.5. AI, data scraping, and bot detection avoidance
In 2026, web scraping has become a battleground between bots and anti-bot defenses (like Cloudflare).
- AI training: Companies use rotating proxies to scrape millions of web pages to train Large Language Models (LLMs) without getting IP-banned.
- Avoiding AI detection: Advanced “AI-enhanced proxies” now mimic human browsing behavior (mouse movements, realistic headers) to bypass AI-driven firewalls that block traditional bots.
8. Risks and limitations of proxy servers
While proxy servers offer significant advantages, they also introduce specific risks and limitations. These issues often arise when proxies are misconfigured or used without proper security measures. Understanding these potential drawbacks is crucial for protecting your data and making informed decisions about your network setup.
8.1. Data logging and trust issues
Not all proxy servers respect user privacy. Many log user data, including:
- IP addresses
- Browsing activity
- Login credentials (in worst-case scenarios)
Free or public proxies are particularly notorious for unethical logging practices. Some may even sell user data to advertisers or third parties.
8.2. Performance degradation
Because proxies introduce an extra layer between the client and the destination server, they can slow down your connection. Common causes include:
- Server congestion
- Poor hardware infrastructure
- Long-distance routing
8.3. Incompatibility with encryption
Some proxies, especially older or simpler ones like HTTP proxies, cannot handle encrypted traffic. This limits their ability to:
- Secure sensitive communications
- Access HTTPS-only websites
- Support secure apps and APIs
Additionally, SSL interception proxies (used for filtering HTTPS) may break end-to-end encryption if not configured correctly, raising serious privacy and compliance concerns.
8.4. Open proxy vulnerabilities
Open proxies, publicly accessible proxies, pose major security threats:
- They’re often exploited by cybercriminals
- Can be used to launch DDoS attacks
- Rarely offer encryption or user authentication
Open proxies are frequently blacklisted and should be avoided in any secure network architecture.
8.5. Shadow IT risks
In corporate environments, authorized proxies are standard, but unauthorized “Shadow IT” proxies pose a significant risk. Employees may set up unapproved proxies to bypass company firewalls or access restricted sites, inadvertently creating unmanaged and insecure entry points into the internal network that hackers can exploit.
8.6. Supply chain and third-party risks
Using external proxy providers introduces third-party risk. A proxy vendor in your supply chain might experience misconfigurations or data breaches. This could expose your data and customer information even if your internal systems are secure.
9. Proxy server vs. VPN: What’s the difference?
Proxy servers and VPNs both help mask your IP address and bypass restrictions, but they differ in how they handle traffic, security, and scope.
A proxy server routes traffic from a specific app (like your browser) through an external server. It usually doesn’t encrypt your data. A VPN encrypts all Internet traffic on your device and routes it through a secure tunnel, offering stronger privacy and protection.
Key differences
| Feature | Proxy server | VPN |
|---|---|---|
| IP masking | Yes | Yes |
| Encryption | No or limited | Full encryption (end-to-end) |
| Scope | Application-level: Only covers specific apps or browsers. | System-level: Covers all traffic, ports, and protocols on the device. |
| Security on public Wi-Fi | Low: Traffic is often unencrypted by default, leaving data exposed. | High: Encrypted tunnel protects data from snooping. |
| Speed impact | Typically faster, less secure | Slightly slower, more secure |
| Use case | Bypass filters, anonymity, caching | Privacy, security, encrypted browsing |
Proxies are better for lightweight tasks like bypassing restrictions or managing multiple accounts. VPNs are ideal for securing data, especially on public networks or when handling sensitive information.
See also our detailed explanation on this topic: Proxy vs VPN: What’s best for your online privacy?
10. Should you actually use a proxy? A decision framework
This is the critical missing piece in most guides. You know what a proxy is, but do you really need one? Before investing time or money, use this simple framework to make the right choice.
The 3 critical questions to ask yourself:
- Do you need to encrypt sensitive data (banking, passwords)?
- If YES → You need a VPN, not a proxy. Proxies do not offer end-to-end encryption.
- Do you need to change your location for a specific task (scraping, testing ads) without slowing down your whole device?
- If YES → A Proxy is ideal. It’s lightweight and task-specific.
- Do you need to bypass a simple IP block (school/work filter) quickly?
- If YES → A Web proxy or browser extension is sufficient.
Quick decision table:
| Your need/scenario | Recommended solution | Why? |
|---|---|---|
| Protecting privacy on public Wi-Fi | VPN | Requires full encryption to prevent hackers. |
| Web scraping / SEO research | Rotating residential proxy | Prevents IP bans by mimicking real users. |
| Bypassing school/work website blocks | Web proxy / HTTP proxy | Quick, lightweight, and doesn’t require installation. |
| Gaming (PS5/Xbox) to lower ping | Smart DNS / SOCKS5 proxy | Faster speeds without encryption lag. |
| Watching Netflix/Disney+ foreign libraries | Residential VPN / Proxy | Datacenter IPs are now blocked; you need a “real” IP. |
| Managing multiple social media accounts | Mobile / 4G proxy | Highest trust score to avoid account bans. |
11. Proxies on mobile and consoles (2026 trends)
Most guides focus on PCs, but modern proxy usage is heavy on mobile and gaming consoles. Here is what you need to know about using proxies on these devices.
11.1. Mobile devices (Android & iOS)
Using a proxy on a phone is different from a computer:
- Wi-Fi only: Standard proxy settings on Android and iOS usually only apply to Wi-Fi connections. If you switch to 4G/5G data, the proxy will disconnect.
- App-specific: Many mobile apps ignore system proxy settings. To force app traffic through a proxy, you often need third-party tools (like “ProxyDroid” on Android) or a VPN app that supports proxy configuration.
11.2. Gaming consoles (PS5, Xbox, Nintendo Switch)
Consoles do not have native browser support for proxy logins or apps. To use a proxy on a console, you have two main options:
- Router level: Configure the proxy directly on your Wi-Fi router. This covers every device in your house, including the console.
- PC/Mac bridge: Connect your console to your computer (via Ethernet or Wi-Fi hotspot) and share the computer’s proxy connection. This is the most common method for gamers wanting to access foreign lobbies or reduce lag.
12. Best practices for using proxy servers securely
Using a proxy server can significantly improve privacy and access, but only if it’s configured and managed properly. Here are the best practices I’ve learned (sometimes the hard way) to stay secure and effective with proxies.
12.1. How to choose a reliable proxy service
When selecting a proxy provider, consider:
- Reputation: Look for trusted vendors with transparent privacy policies
- Server variety: Geographic diversity for geo-testing or access
- Anonymity level: High-anonymity (elite) proxies offer better privacy
- Support and uptime guarantees
Tip: Services like Bright Data, Oxylabs, and Smartproxy are often favored by developers and researchers for large-scale tasks.
12.2. Avoiding public/open proxies
Free or open proxies are tempting but dangerous:
- Often lacks encryption
- May inject ads or malware
- Could steal credentials or data
Open proxies pose serious security risks and are frequently used for malicious activities.
Best practice: Avoid public proxy lists entirely. Instead, use authenticated, private proxies, even if they come with a cost. Security and stability are worth it.
12.3. Combining proxies with other tools
Proxies are more powerful when combined with other privacy and security layers:
- VPN: Use a VPN and proxy together for added anonymity
- Antivirus and firewall: Protect against local threats and leaks
- Browser isolation: Use dedicated browser profiles or containers per proxy
12.4. Legal and ethical considerations
Proxies can be misused. Ensure your use is legal and ethical by:
- Following the terms of service of the sites you access
- Avoiding data scraping where prohibited
- Respecting privacy laws (e.g., GDPR, CCPA)
Generally, proxy use isn’t illegal by default, but how you use it matters, especially if it involves bypassing protections or scraping restricted data.
You may be interested in reading this related article:
13. FAQs about proxy server
Here are clear, direct answers to common questions about proxy servers.
What is a proxy server used for?
A proxy server is mainly used for five key purposes: enhancing security by hiding your IP, ensuring anonymity online, bypassing blocked content (geo-restrictions), balancing network traffic loads, and caching data to speed up request times.
Should proxy server be on or off?
For most home users, your proxy settings should be OFF. You should only turn it on if you have a specific reason, such as connecting to a work network, bypassing a specific block, or using a privacy tool. If it is ON without your knowledge, it could be a sign of malware.
How do I know if I am using a proxy server?
You can check your system settings. On Windows, go to Settings > Network & Internet > Proxy. On Mac, go to System Settings > Network > Proxies. If any box is checked or an address is filled in under “Manual proxy setup,” you are using one.
Is a VPN the same as a proxy server?
No. A proxy works at the application level (like your browser) and does not encrypt your data. A VPN works at the operating system level, encrypting all traffic leaving your device. VPNs offer higher security, while proxies are often faster for specific tasks.
Are proxy servers legal?
Yes, using a proxy server is legal in most countries for legitimate purposes like privacy, security, and accessing content. However, using a proxy to commit crimes (hacking, fraud, copyright theft) is illegal.
Do proxy servers slow down internet speed?
It depends. Free or public proxies often slow down your internet significantly because too many people use them at once. However, high-quality private proxies can sometimes speed up your connection by caching frequently visited websites and reducing bandwidth usage.
What is a proxy server address?
A proxy server address is the digital “location” of the proxy you are connecting to. It typically consists of an IP address followed by a port number, looking like this: 192.168.1.50:8080. You need to enter this exact address in your settings to connect.
Can I use a free proxy server safely?
Generally, NO. Running a server costs money. If a proxy is free, they are likely making money by selling your browsing data, injecting ads into your browser, or even infecting your device with malware. It is much safer to use a reputable paid service.
Can I use a proxy server on my phone (Android/iOS)?
Yes, both Android and iOS support proxy configurations in their Wi-Fi settings. However, these settings usually only apply to Wi-Fi. If you switch to mobile data (4G/5G), the proxy will disconnect. For consistent protection on mobile, use a dedicated proxy app or VPN.
Does using a proxy lower ping in gaming (PS4/PS5/PC)?
It can, but not always. If the game server is far away, a high-quality SOCKS5 proxy located near the game server can provide a more direct route than your ISP, potentially lowering ping. However, using a low-quality or free proxy will almost certainly increase lag and latency.
Do proxies work with Netflix/Streaming services?
In 2026, standard datacenter proxies rarely work with Netflix, Disney+, or Hulu because these platforms have advanced detection systems. To bypass these blocks reliably, you need a Residential proxy, which uses an IP address from a real home ISP, making it much harder to detect.
How do I set up a proxy server easily?
The difficulty depends on the method.
- Easy: Use a browser extension (like FoxyProxy) or a “Smart DNS” service.
- Medium: Manually enter the IP and Port in your Windows/Mac network settings.
- Hard: Setting up a proxy on a router or gaming console requires more technical knowledge.
14. Conclusion
Understanding what is a proxy server helps you make informed decisions about how you manage your online identity. We have explored how proxies work, the various types available, and their specific use cases for unblocking content or basic privacy.
While proxies provide utility for specific tasks, they lack the comprehensive encryption and security layers of a VPN. If your goal is simply high speed for basic tasks, a proxy is a suitable option. However, if you want to combine accessing restricted content with fast speeds and robust data protection, top-tier VPNs are the superior choice.For more helpful articles and insights on VPNs, explore our VPN Guide section at Safelyo.