Does Tor have a built-in VPN? The short answer is no. The Tor Browser does not come with an integrated virtual private network (VPN). It relies on multi-layered onion routing instead.
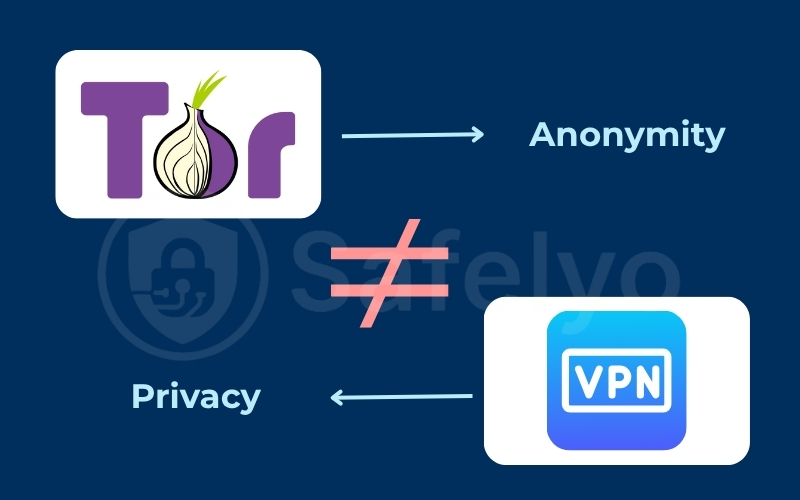
This causes common confusion. You might assume Tor functions like a VPN because it offers anonymity. In reality, they work differently. Tor bounces traffic through a volunteer network, while a VPN creates a private tunnel.
However, the landscape is changing. The Tor Project launched a standalone VPN beta for Android in September 2025. This article clarifies these updates. You will learn if the browser alone is enough for your security needs.
Key takeaways:
- The desktop Tor Browser does not include a built-in VPN.
- Tor provides anonymity through multi-node routing, while a VPN offers privacy through a single encrypted tunnel.
- The browser only protects web traffic within its own window and ignores other computer applications.
- Mobile users can route their entire device’s traffic through Tor using Orbot or the new Tor VPN beta.
- You can connect to a standalone VPN before opening Tor to hide your network usage from your internet provider.
1. Does Tor have a built-in VPN?
No, Tor Browser does not have a built-in VPN. You will not find a “connect to VPN” button or any integrated VPN service within the browser’s settings.
This is a very common point of confusion. Many users ask, “Is Tor a VPN?” because both tools are powerful and famous for protecting online privacy. It is easy to group them together.
The key is understanding their different goals:
- A VPN focuses primarily on privacy. It creates a secure, encrypted tunnel between your device and a single server run by a company. This hides your online activity from your Internet Service Provider (ISP). Your ISP only sees you connecting to the VPN, not the websites you visit.
- Tor Browser focuses primarily on anonymity. It hides who you are from the websites you visit. It does this by routing your connection through a decentralized, three-layer network run by volunteers. The website sees the IP address of the final volunteer node, not your real IP.
They are built to solve two different problems. Tor Browser acts as a modified version of Firefox with built-in encryption. It does not have a switch to encrypt your other apps like Spotify or Steam.
2. Why Tor Browser doesn’t include a VPN
The entire philosophy behind Tor is decentralization. Its power comes from a global network of thousands of volunteer-run servers, called nodes. No single person, company, or government controls this network.
If Tor included a “built-in VPN,” it would break this entire model. A VPN is a centralized service. You must trust the single company that runs the VPN servers. You trust them not to log your activity and to protect your data.
This creates a direct conflict. Tor is designed to be trustless. You do not need to trust the volunteers because of its 3-layer encryption. A VPN is a trusted system where you place your full trust in the VPN provider.
By not including a VPN, the Tor Project keeps the browser focused on anonymity. It gives you, the user, the choice to use a separate VPN provider if you wish.
3. Tor Browser vs. Tor Network: Understanding the difference
It is crucial to distinguish between the browser application and the underlying network. This explains why your entire computer is not automatically protected.
The Tor Browser only protects the traffic inside the browser window. When you open Tor Browser and visit a website, that specific activity is anonymous.
The Tor Network is the underlying infrastructure. It can be used system-wide if configured correctly, but this is not the default setting.
Consider a practical example. If you open Tor Browser, your web surfing is anonymous. If you then open Outlook, Steam, or a torrent client separately, your ISP sees everything. Tor Browser does NOT tunnel your whole system’s traffic. It only handles what happens inside the browser.
4. What privacy features does Tor Browser have?
So, if Tor doesn’t have a VPN, what does it have? It includes a powerful, multi-layered defense system focused entirely on anonymity. These features work together to make your identity harder to trace.
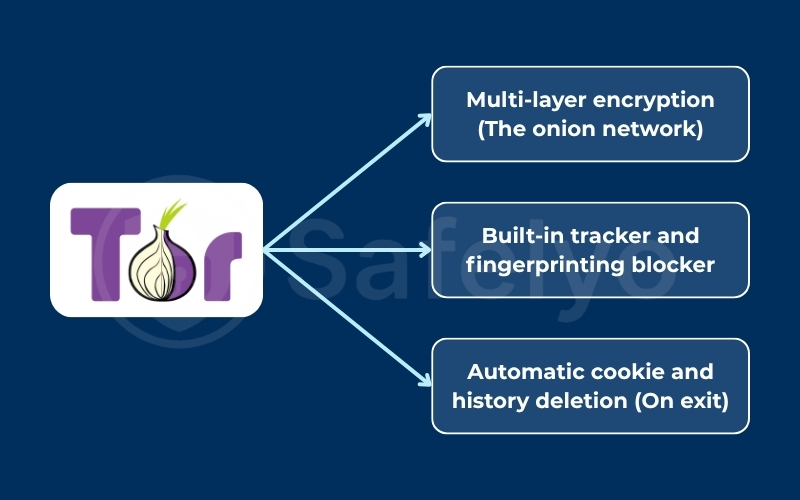
4.1. Multi-layer encryption (The onion network)
Tor’s name comes from “The Onion Router”. Your data is wrapped in three layers of encryption.
It then travels to the network through a 3-step process.
First, the guard node peels off the first layer. This node only knows where you came from, but not your final destination.
Second, the middle node peels off the second layer. It only knows the guard and exit nodes.
Finally, the exit node peels off the last layer. It sees the website you are visiting, but has no idea who or where you are. Note that the exit node decrypts the traffic to send it to the destination website. This is a key vulnerability not present in end-to-end VPN encryption.
This entire process means no single point in the network knows your full path.
4.2. Built-in tracker and fingerprinting blocker
Tor Browser actively fights against online tracking. It automatically blocks many of the third-party scripts, ads, and trackers that follow you across the internet.
More importantly, it prevents browser fingerprinting. This is a technique where sites build a unique profile of you. They use details like your screen size, installed fonts, and browser version.
Tor Browser makes every user look the same by standardizing these settings. This makes it very difficult for a website to single you out from the crowd of other Tor users.
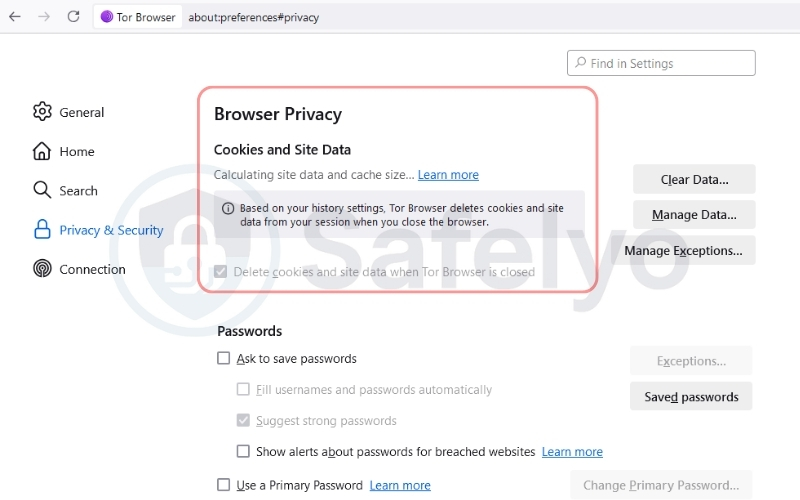
4.3. Automatic cookie and history deletion (On exit)
When you click the “X” to close the browser, everything is instantly wiped. This includes all your browsing history, any cookies from websites, and your cache of stored images or files.
It leaves no trace of your activity on your computer. The next time you open Tor Browser, it is a completely fresh, clean session.
5. Tor Project’s actual VPN: Orbot and beta options
While the desktop browser lacks a VPN, the Tor Project offers solutions for mobile devices that effectively bridge this gap. These tools are designed to answer the user demand for system-wide protection.
5.1. Orbot proxy app
Orbot is a free proxy app specifically designed for Android and iOS. It acts as a bridge between the operating system and the Tor network.
When you activate Orbot, it intercepts traffic from other applications on your phone. It then routes this traffic through the encrypted Tor network. This means apps like Twitter, Gmail, or YouTube can be anonymized even though they do not have built-in Tor support.
Orbot uses the VPN mode feature found in Android settings to function. It does not connect to a commercial VPN server. Instead, it creates a local tunnel on your device that forces your data packets into the Tor network. This provides system-wide anonymity for mobile users.
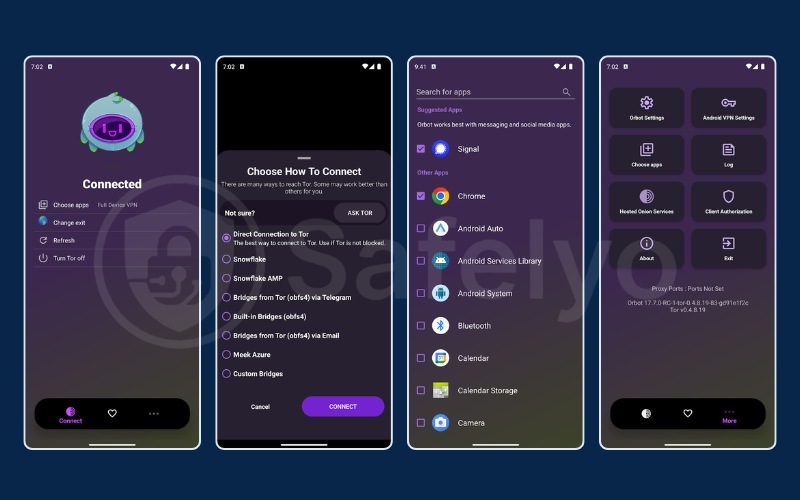
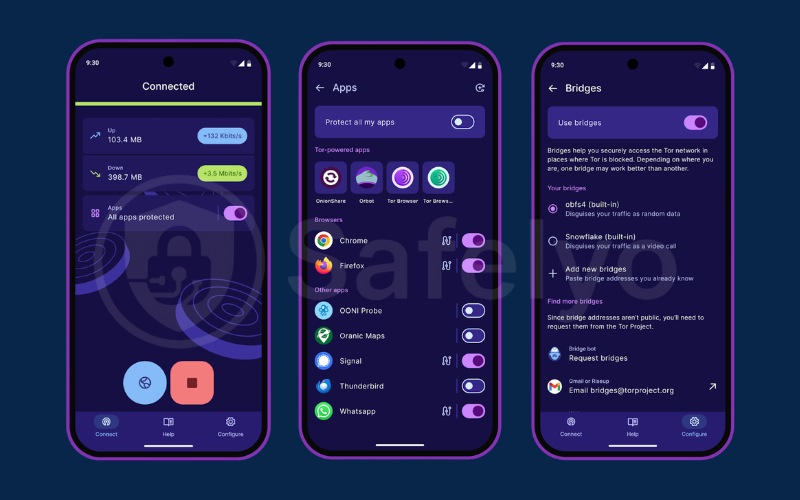
5.2. Tor VPN beta
The Tor VPN beta is a standalone application launched by the Tor Project in September 2025. It serves a different purpose than Orbot. It is designed to be a simplified, user-friendly alternative for people who find technical settings confusing.
This app mimics the interface of standard commercial VPNs. It features a simple connect button that routes your entire device’s traffic through the Tor network. The goal is to make Tor accessible to non-technical users who want privacy without configuring proxies.
Unlike Orbot which offers granular control over which apps use Tor, the Tor VPN beta focuses on ease of use. It ensures that all traffic is routed securely by default. This reduces the risk of user error and accidental leaks.
6. How to combine a VPN with Tor Browser
Since Tor doesn’t have a built-in option, it’s natural to ask if you can combine them manually.
Advanced users layer these tools for maximum privacy. The main goal is to hide the fact that you are using Tor from your internet service provider.
There are two ways to do this. One is safe and recommended, while the other is not.
6.1. Method 1: Tor over VPN (recommended)
This is the simplest, safest, and most common method. “Tor over VPN” means you route your Tor traffic through an active VPN connection. Your computer connects to the VPN server first, and only then does your Tor traffic pass through that encrypted tunnel.
Here are the steps to do it:
- Open your standalone VPN application and connect to a server. Your entire internet connection is now encrypted.
- After your VPN is connected, open the Tor Browser and use it normally.
The primary benefit of this method is that your ISP cannot see that you are using Tor. It only sees a block of encrypted traffic going to your VPN server, which looks like normal VPN use.
This setup offers protection in other ways. Your VPN provider knows your real IP address, but it cannot see activity on Tor. It only detects a connection to the Tor network.
Meanwhile, the Tor network never sees your real IP. It only sees the IP address of the VPN server. This creates a powerful extra layer of anonymity.
You should use Tor alone for general privacy, whistleblowing, or simply avoiding ad trackers.
You should add a VPN if your ISP blocks Tor, or if you live in a country with strict censorship like Russia or China. It is also useful if you simply want to hide the fact that you are using Tor from your ISP.
You must be careful because using a cheap or free VPN with Tor can actually reduce your privacy. A bad VPN becomes the weak link in the chain because they may log your data. Only use high-grade, no-log VPNs if you choose to combine them.
6.2. Method 2: VPN over Tor (not recommended)
This method reverses the process and is not recommended for most people. It means you try to route your VPN connection through the Tor network.
This involves the following steps:
- Open the Tor Browser first.
- Configure your VPN application to route its own connection through the Tor network.
This setup is extremely difficult, as most VPN apps do not support this configuration. Even if you succeed, the connection will be incredibly slow. Tor is already slow due to its 3-node design, and forcing heavy VPN encryption through that slow network makes the internet almost unusable.
The most important reason to avoid this is security risk. The final exit node in the Tor network can see your internet traffic.
This means the volunteer running that node could potentially see unencrypted traffic on its way to the VPN, which might include login credentials. It exposes sensitive information to the most vulnerable part of the Tor network.
7. How to enable system-wide Tor protection
Some users want to force all their computer traffic through Tor, effectively making it act like a built-in VPN. This requires specific tools beyond the standard browser.
OnionFruit is a tool designed for Windows to route most of your system traffic through the Tor network. It handles the configuration for you. This allows applications outside the browser to use Tor.
Tortilla is a tool for tech-savvy users. It provides a secure way to route TCP and DNS traffic through Tor.
Tor-enabled routers can be configured to route all home traffic through Tor. This protects every device connected to your Wi-Fi.
Routing all system traffic through Tor will significantly slow down your connection. Gaming and high-definition streaming will likely become impossible due to the latency of the Tor network.
8. Can the FBI track Tor users?
A common fear is whether Tor is truly untraceable.
Tracking Tor users is extremely difficult but not impossible. While Tor is highly secure, nation-state actors like the FBI or NSA can use traffic correlation attacks. This involves monitoring both the entry and exit nodes of the network to match traffic patterns.
In most cases where Tor users are caught, it is not because the Tor network failed. It is usually due to user error. Logging into personal accounts like Facebook or Google while using Tor de-anonymizes you immediately.
9. FAQs about Does Tor have a built-in VPN
Let’s answer a few other common questions about using Tor and VPNs.
Is Tor Browser safer than a VPN?
They are different. Tor is better for anonymity (hiding who you are). A VPN is better for privacy (hiding what you do from your ISP). For daily browsing, a VPN is faster and more practical.
Can my ISP see me using Tor Browser?
Yes. If you use Tor without a VPN, your ISP can see that you are connecting to the Tor network. They cannot see what you are browsing, but they know you are using Tor.
Will a separate VPN slow down Tor Browser?
Yes. Tor is already slow because it routes your traffic through three nodes. Adding a VPN (Tor over VPN) adds another step. This will slow your connection further. This is the trade-off for increased security.
Can I use Tor Browser instead of a VPN for daily use?
It is not recommended. Tor is often too slow for streaming or large downloads. Many websites also block users coming from Tor exit nodes. A VPN is much more suitable for everyday internet use.
Is Tor legal in the US?
Yes, Tor is completely legal to use in the US. The Tor Project is a registered non-profit organization focused on education and research.
Does Tor Browser hide your location?
Yes, websites will see the IP address of the Tor exit node, not your real IP address. This exit node could be in a completely different country, effectively masking your physical location.
How do I enable VPN in Tor?
You cannot enable a VPN inside the Tor Browser because it does not exist. To use a VPN with Tor, you must download and run a separate VPN application on your computer before you open the Tor Browser.
10. Conclusion
So, does Tor have a built-in VPN? No, it doesn’t. Tor’s goal is anonymous, decentralized browsing. VPNs provide private, encrypted access from a central provider.
For daily privacy from your ISP, a VPN is the best choice. For maximum anonymity, Tor is the best choice. To hide usage, connect to your VPN before opening Tor Browser.
For free anonymous browsing, stick to the Tor Browser. If you need system-wide coverage on mobile, Orbot or the Tor VPN beta are your best options. However, if speed and streaming are priorities, you should invest in a paid VPN.
For more detailed tutorials and comparisons, explore our VPN Guides section or visit Safelyo for the latest privacy tips.