If you are exploring advanced ways to protect your digital footprint, you have likely encountered two heavyweights: VPNs and Tor. But what happens when you combine them? What is Onion over VPN, and is it the ultimate privacy solution you have been looking for?
At its most basic level, Onion over VPN (often called Tor over VPN) is a privacy configuration in which you first connect to a standard VPN server before routing your traffic through the Tor network. This method creates a double layer of encryption that hides your Tor usage from your Internet Service Provider (ISP) and masks your real IP address from the Tor entry node.
If you are short on time, here are the essential facts you need to know about the Onion over VPN setup:
- What is Onion over VPN?
→ It is a privacy method where you connect to a standard VPN first, then route your traffic through the Tor network. - What is the main benefit?
→ It hides your Tor usage from your ISP and protects your real IP address from potentially malicious Tor entry nodes. - Will it slow down my internet?
→ Yes, drastically. The multiple layers of encryption make it too slow for streaming, gaming, or torrenting. - Does it guarantee 100% anonymity?
→ No. While incredibly secure, your identity can still be compromised by user error (like logging into personal accounts) or browser fingerprinting. - Who should actually use it?
→ Journalists, activists, and people in high-censorship regions. For everyday browsing and privacy, a standard VPN is all you need.
While this sounds like a digital invisibility cloak, it is not without its trade-offs. In my experience testing various security setups, I have found that while it significantly boosts anonymity, it can also drastically impact connection speeds. In this guide, I will walk you through exactly how this technology works, the critical differences between it and standard VPNs, and whether the extra layer of security is worth the performance cost for your specific needs.
Let’s unravel the layers of Onion over VPN.
1. What is Onion over VPN?
To truly understand what is Onion over VPN, we first need to clear up a common misconception: It is not a single piece of software you simply download. Instead, it is a specific method of connecting to the internet that combines two powerful privacy tools: a Virtual Private Network (VPN) and the Onion Router (Tor).
I often describe this setup to my non-tech friends as “wearing a mask under a balaclava”. You are essentially layering two distinct types of anonymity to ensure that even if one layer is compromised, your identity remains hidden.
1.1 A simple explanation
Let’s break it down using a real-world analogy.
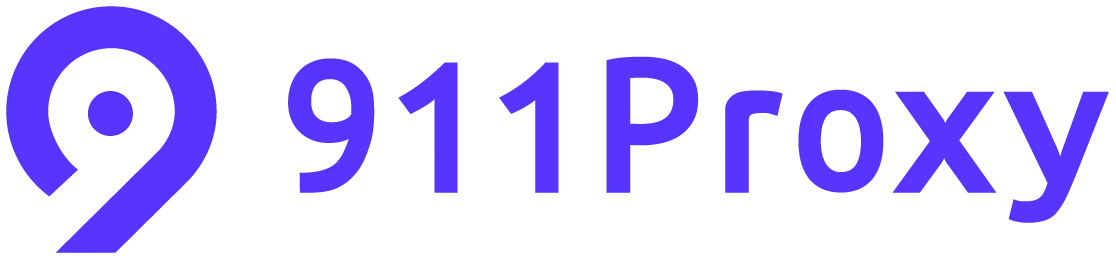
- Standard VPN: Imagine you drive your car through a private, underground tunnel. No one outside (like your Internet Service Provider or hackers) can see your car or who is driving it. They only see that you entered a tunnel.
- Tor (The Onion Router): Imagine you get out of your car and hop into a series of three different taxis. The first driver knows where you came from but not where you are going. The second driver knows nothing. The third driver knows where you are going but not where you came from.
- Onion over VPN: You drive your car through the private tunnel (VPN) first. When you exit the tunnel, you immediately hop into the series of taxis (Tor).
In this scenario, the tunnel operator (VPN) knows who you are but not where you are going. The first taxi driver (Tor Entry Node) sees the tunnel’s exit, not your house. This creates a highly compartmentalized system where no single entity has the full picture of your online journey.
1.2 The technical breakdown
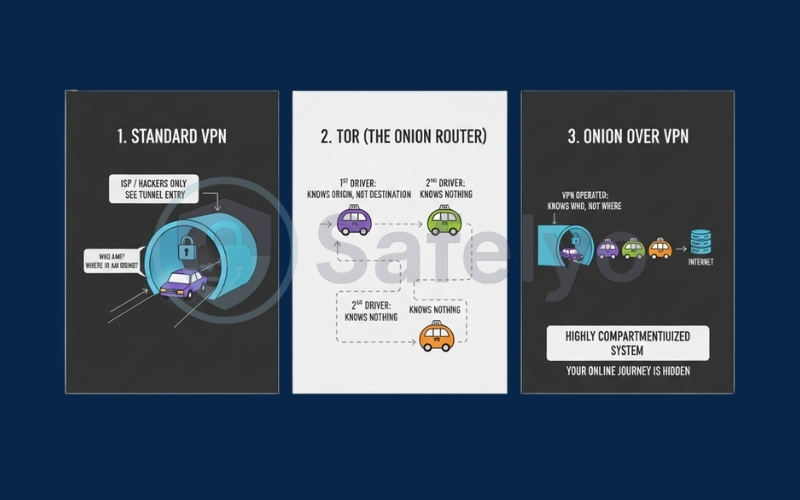
For those of you who prefer the technical details, Onion over VPN explained works by establishing a secure VPN connection before launching the Tor browser. Here is the technical flow of data in this configuration:
- Encryption: Your device encrypts your data and sends it to the VPN server.
- VPN Tunnel: Your traffic travels through the encrypted VPN tunnel. At this stage, your ISP can only see encrypted gibberish going to a VPN server; they cannot see that you are accessing the Tor network.
- Tor Entry: The data leaves the VPN server and enters the Onion Router and VPN circuit via a Tor Entry Node. Crucially, the Entry Node sees the IP address of the VPN server, not your real residential IP address.
- Onion Routing: The traffic bounces through the standard Tor circuit (Entry -> Middle -> Exit).
- Destination: The traffic exits the Tor network and reaches the website or service you are visiting.
By using this Tor over VPN method, you mitigate a specific vulnerability in the Tor network: The entry node. Since Tor relies on volunteers, there is always a risk that a malicious actor could control an entry node and log your real IP address. With a VPN in the mix, that malicious actor only logs the VPN IP address – data that is essentially useless to them.
2. How does Onion over VPN work?
Understanding the mechanics behind this setup is crucial because it highlights exactly where your data is protected and where potential vulnerabilities might still exist. How does Onion over VPN work in practice?
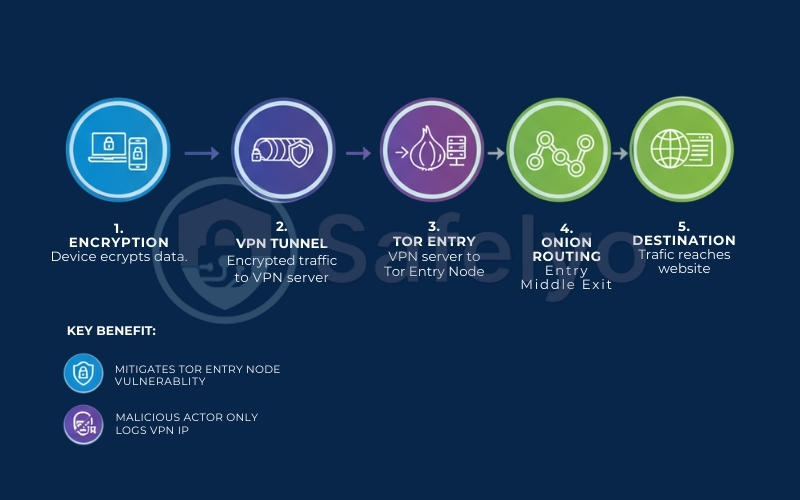
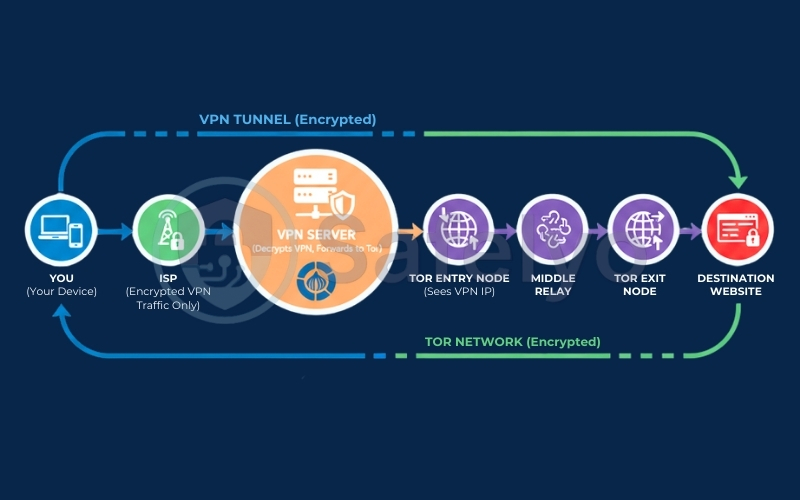
It effectively creates a “tunnel within a tunnel”. To visualize the Onion over VPN path, think of it like this:
You (Your Device) → ISP (Sees encrypted VPN traffic only) → VPN Server (Decrypts VPN layer, forwards to Tor) → Tor Entry Node (Sees VPN IP) → Middle Relay → Tor Exit Node → Destination Website
When I configure this for my own privacy testing, the process follows a strict, linear path. Here is the step-by-step journey your data takes from the moment you click a link:
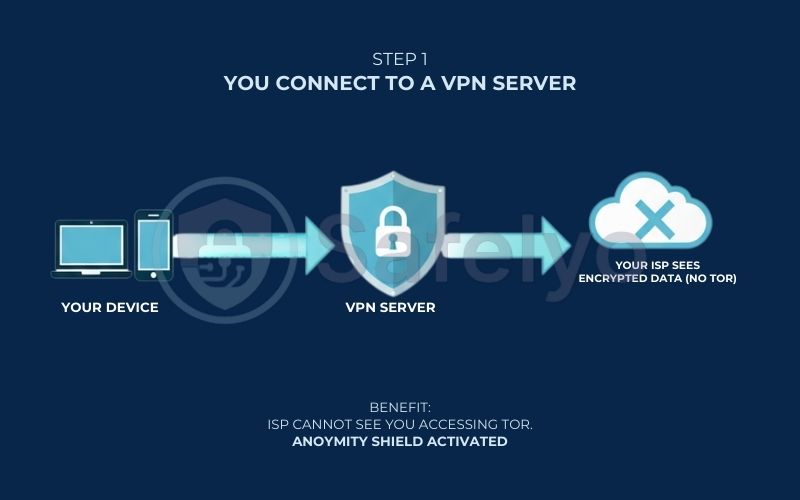
2.1. Step 1: You connect to a VPN server
Before you even launch the Tor browser, your device establishes a connection to a standard VPN server.
- What happens: Your internet traffic is encrypted on your device and sent through a secure tunnel to the VPN provider’s server.
- The benefit: This is the “shield” phase. Your ISP can see that you are sending encrypted data, but they cannot see what that data is or where it is going. Crucially, they cannot see that you are about to access the Tor network. This is vital if you live in a region where Tor is blocked or flagged as suspicious activity.
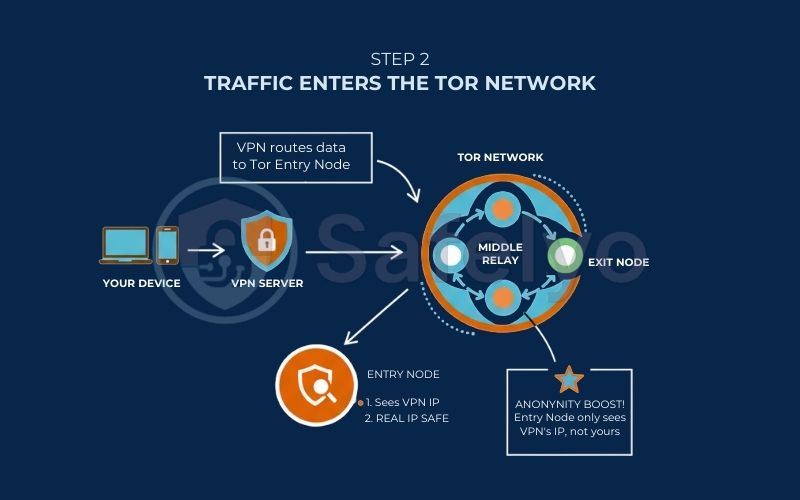
2.2. Step 2: Traffic enters the Tor network
Once your data reaches the VPN server, it is then routed toward the Tor network.
- The Entry Node: Your traffic enters the Tor network through a volunteer-operated computer called an “Entry Node” (or Guard Node).
- The anonymity boost: This is where the magic happens. Normally, the Entry Node sees your real IP address. However, because you are using Onion over VPN, the Entry Node only sees the IP address of your VPN server. If the Entry Node is malicious or compromised, your real identity remains safe.
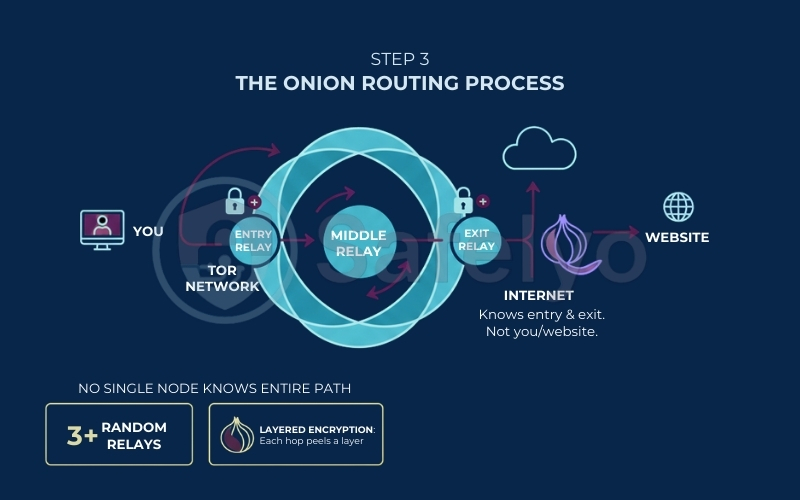
2.3. Step 3: The Onion routing process
Inside the Tor network, your traffic bounces through at least three randomly selected relays (computers).
Layered encryption: At each hop (Entry → Middle → Exit), a layer of encryption is peeled off – hence the “Onion” metaphor. No single node knows the entire path; the Middle Relay knows the Entry and the Exit, but not who you are or what website you are visiting.
2.4. Step 4: The Exit Node sends traffic to the destination
Finally, your traffic reaches the “Exit Node”. This is the final gateway between the anonymous Tor network and the open internet (the Surface Web).
- The reveal: The Exit Node decrypts the final layer and sends your request to the destination website (e.g., a news site or a forum).
- What the website sees: The request comes from the Tor Exit Node’s IP address, not your VPN IP, and certainly not your home IP.
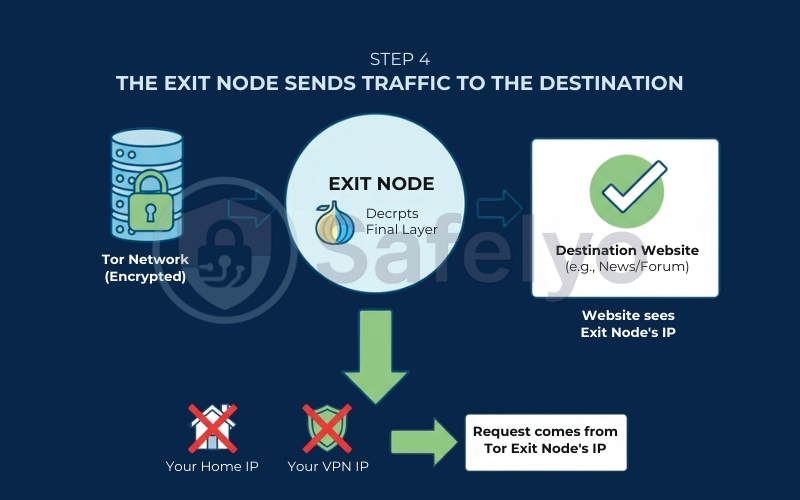
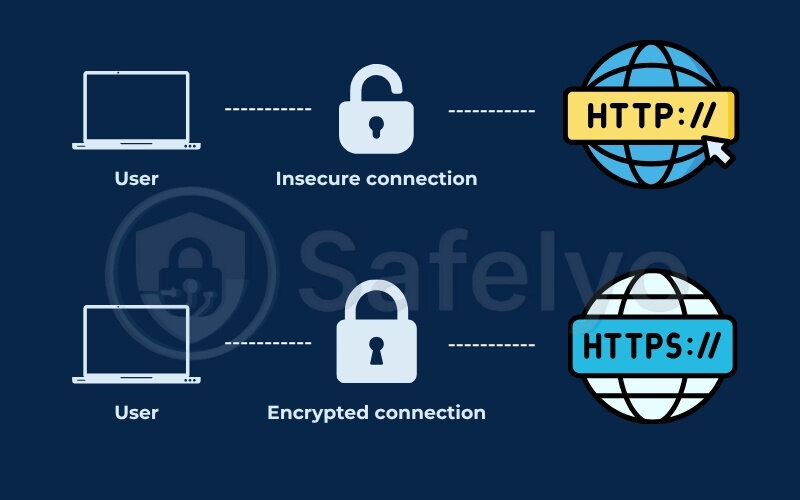
Note: It is important to remember that while the Exit Node cannot see who you are (thanks to the VPN + Tor layers), it can technically see the data you are sending if the website does not use HTTPS encryption.
3. What are the benefits of Onion Over VPN?
Now that we have covered the technical “how”, you might be wondering: Why go through the trouble? Is the extra step of connecting to a VPN before Tor really necessary?
In my experience testing privacy tools for high-risk scenarios, Onion over VPN isn’t just about adding layers – it is about fixing specific vulnerabilities in the standard Tor network. Here are the four key benefits that make this setup a gold standard for anonymity.
3.1. Hides Tor usage from your ISP
This is arguably the biggest advantage. When you use the Tor browser directly, your ISP can clearly see that you are connected to the Tor network.
- Why it matters: Even if your ISP cannot see what you are doing inside Tor, the mere act of using it can raise red flags. In some countries with strict censorship, or even on certain corporate/university networks, using Tor can lead to throttling, monitoring, or being placed on a “watch list”.
- The solution: By connecting to a VPN server first, all your ISP sees is encrypted traffic going to a VPN server. The fact that you are subsequently entering the Tor network is completely hidden inside that VPN tunnel.
3.2. Protects your real IP from Tor Entry Nodes
The Tor network relies on thousands of volunteer-run nodes. While most are operated by privacy activists, some can be set up by malicious actors (hackers or government agencies) looking to de-anonymize users.
- The risk: In a standard Tor connection, the first node (the Entry Node or Guard Node) must know your real IP address to accept your connection. If a malicious actor controls this node, they know who you are and that you are using Tor.
- The fix: With Onion over VPN, the Entry Node only sees the IP address of your VPN server, not your home IP. This adds a critical layer of separation between your identity and the Tor network.
>> Read more: Does Tor have a built-in VPN? What you need to know
3.3. Adds an extra encryption layer
Tor encrypts your traffic multiple times, but there is a catch: The Exit Node (the last computer in the chain) decrypts your data to send it to the destination website.
- The vulnerability: If the website you are visiting does not use HTTPS (encryption), a malicious Exit Node could theoretically spy on your data.
- The boost: While a VPN cannot encrypt traffic after it leaves the Exit Node, using a VPN ensures that your traffic is encrypted before it even enters the Tor network. This means that even if someone were monitoring your local network or the connection between you and the Entry Node, they would face an impenetrable wall of VPN encryption plus Tor encryption.
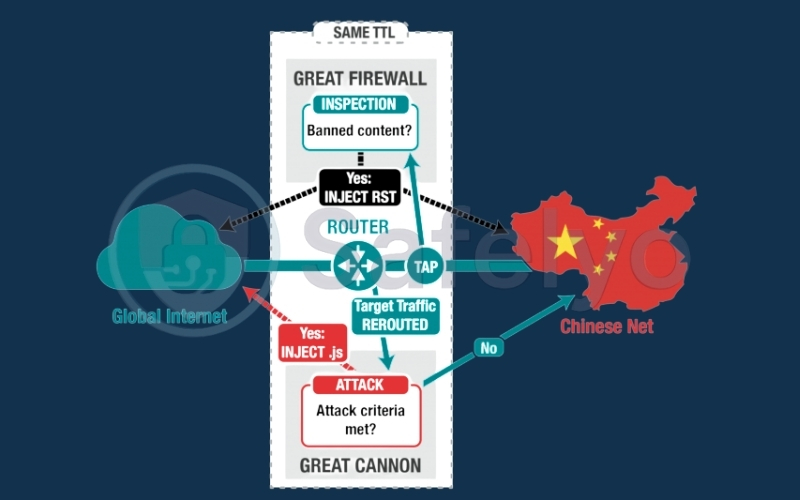
3.4. Useful in restrictive countries
For users living under regimes with heavy internet censorship (like the “Great Firewall”), accessing the Tor network directly is often impossible because the public list of Tor nodes is blocked.
The workaround: By connecting to a VPN first, you bypass the local censorship block. Since the censorship firewall only sees a connection to a VPN server (which is often allowed or harder to block), you can then “tunnel through” to the Tor network without interference. This makes Onion over VPN a vital tool for journalists and activists needing to bypass sophisticated blocking mechanisms.
Key takeaway: Think of Onion over VPN as an insurance policy. You are not just trusting Tor to keep you anonymous; you are ensuring that even if Tor fails or is compromised at the entry point, your true identity remains safe behind the VPN shield.
4. What are the risks and limitations?
While Onion over VPN is a powerhouse for privacy, I always remind my readers: There is no such thing as a “silver bullet” in cybersecurity. This setup comes with significant trade-offs that might make it unsuitable for your daily browsing.
Before you enable this feature, you need to be aware of the performance hits and the specific security nuances that even a double-layer encryption system cannot fix.
4.1. Severe speed reduction
If you are used to lightning-fast fiber speeds, Onion over VPN will feel like stepping back into the dial-up era.
- The Bottleneck: Tor creates anonymity by bouncing your traffic through three random volunteer nodes around the world. Each “hop” adds latency.
- The Compound Effect: When you add a VPN encryption layer on top of that, the slowdown is compounded. In my own speed tests, I have seen connection speeds drop by 80% to 90%.
- The Reality: This setup is strictly for secure communication, reading text, or accessing specific .onion sites. Do not expect to stream 4K video, play online games, or download large files. It is simply too slow.
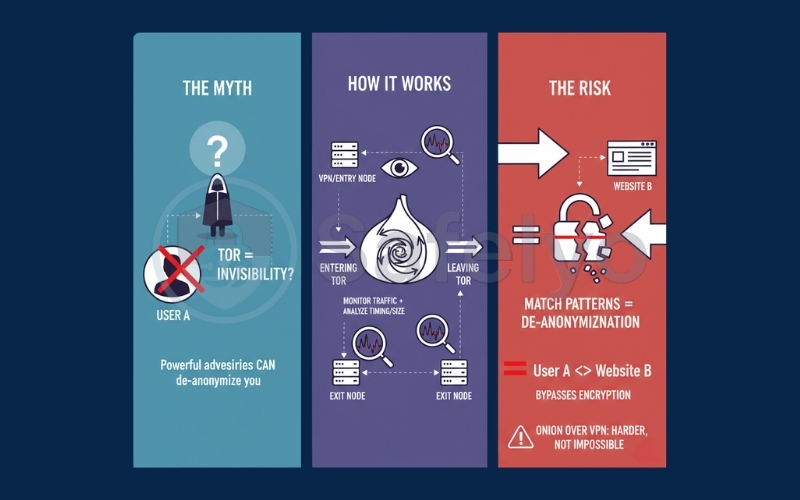
4.2. Not 100% anonymous (Traffic Correlation)
A common myth is that Tor makes you invisible. In reality, a sufficiently powerful adversary (like a global intelligence agency) can still theoretically de-anonymize you using Traffic Correlation Attacks.
- How it works: If an entity can monitor the traffic entering the Tor network (at your VPN server or Entry Node) and the traffic leaving the Tor network (at the Exit Node), they can analyze the timing and size of the data packets.
- The Risk: By matching the patterns, they can mathematically prove that “User A” is talking to “Website B”, bypassing the encryption entirely. While Onion over VPN makes this harder, it does not make it impossible.
4.3 Malicious Exit Nodes
The “Exit Node” is the final computer in the Tor chain that decrypts your traffic and sends it to the destination website. Because anyone can volunteer to run a Tor node, hackers sometimes set up malicious Exit Nodes.
- The Danger: If you visit a website that does not use HTTPS encryption (look for the padlock icon), a malicious Exit Node can read (and even alter) the unencrypted data passing through it.
- The Limit: Using a VPN before Tor does not protect you here. Your VPN encryption ends before the traffic enters Tor. Once it reaches the Exit Node, you are relying solely on the website’s HTTPS encryption.
4.4 Browser fingerprinting is still possible
Hiding your IP address is only half the battle. Advertisers and trackers now use “Fingerprinting” to identify you based on your device’s unique characteristics.
- What they see: Screen resolution, installed fonts, battery level, operating system version, and browser window size.
- The Mistake: If you use Onion over VPN with a standard browser (like Chrome or Safari) instead of the dedicated Tor Browser, you are likely still identifiable. The Tor Browser is specifically built to make every user look exactly the same (same window size, same fonts) to defeat fingerprinting.
Pro Tip: Never maximize the Tor Browser window to full screen. Doing so reveals your monitor’s resolution, which is a key data point for fingerprinting scripts.
5. Onion Over VPN vs other privacy configurations
It is easy to get lost in the jargon of privacy tools. Tor over VPN, VPN over Tor, and Double VPN might sound like variations of the same thing, but they offer vastly different levels of protection, speed, and anonymity.
| Feature | Tor Alone | Onion Over VPN | VPN Over Tor | Double VPN |
| Hides Tor use from ISP? | No | Yes | No | N/A |
| Protects Real IP from Entry Node? | No | Yes | Yes | N/A |
| Setup Difficulty | Easy | Medium | Hard | Easy |
| Speed Impact | High | Very High | Extreme | Moderate |
In my testing, understanding these distinctions is often the difference between a secure connection and a frustratingly slow (or even exposed) one. Let’s compare Onion over VPN against the alternatives.
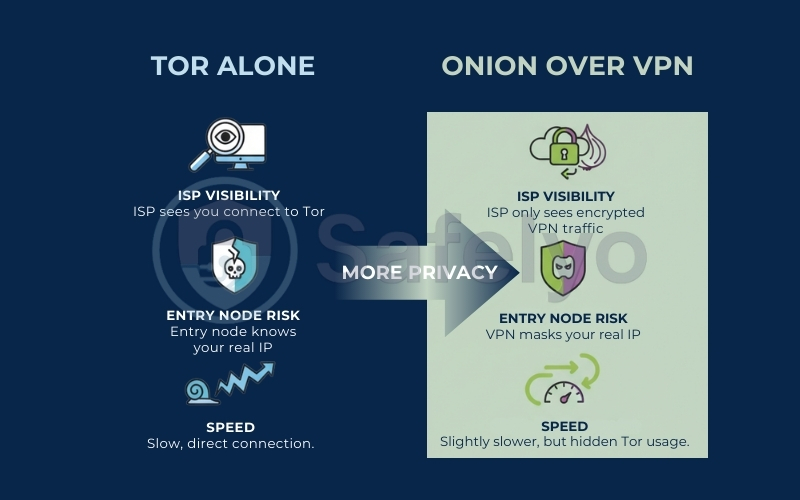
5.1. Onion Over VPN vs using Tor alone
The standard way to use Tor is simply downloading the Tor Browser and connecting directly. So, why add a VPN?
- ISP Visibility: When you use Tor alone, your ISP can clearly see that you are connected to the Tor network. While they cannot see what you are doing inside, the mere act of using Tor can flag you for surveillance in some countries. With Onion over VPN, your ISP only sees encrypted VPN traffic.
- Entry Node Risk: In a standard Tor connection, the first volunteer computer (the Entry Node) knows your real IP address. If that node is malicious or compromised, your identity could be exposed. Onion over VPN masks your real IP with the VPN server’s IP, neutralizing this risk.
- Speed: Tor is inherently slow due to bouncing your data around the world. Adding a VPN encryption layer generally adds a small amount of latency, but the trade-off for hiding your Tor usage from your ISP is often worth it for privacy-conscious users.
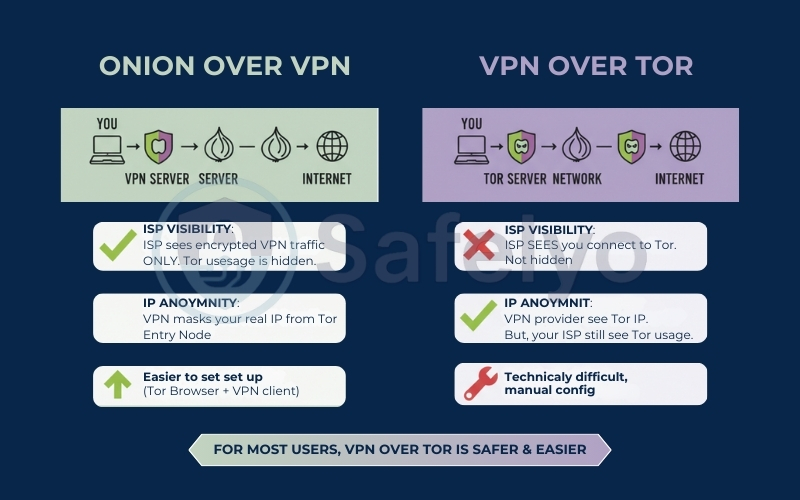
5.2. Onion Over VPN vs VPN Over Tor
This is the most common point of confusion. VPN over Tor is the reverse configuration: You connect to the Tor network first, and then tunnel a VPN connection through it.
- How it works: Your traffic goes: You → Tor Entry v Tor Exit → VPN Server → Internet.
- The key difference: Because you connect to Tor first, your VPN provider cannot see your real IP address (they only see the Tor Exit Node IP). However, your ISP can still see that you are using Tor.
- Why it is rare: Setting this up is technically difficult and often requires manual configuration. Furthermore, it does not protect you from ISP snooping on the fact that you are using Tor. For most users, Onion over VPN (connecting to VPN first) is the safer and more practical choice.
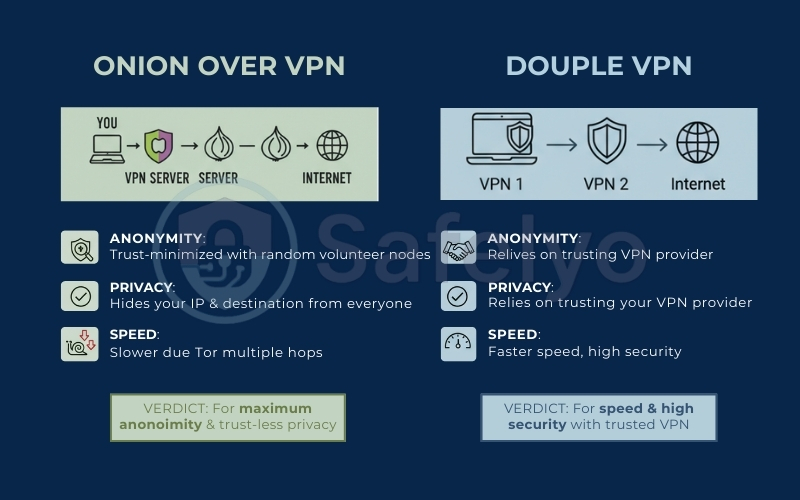
5.3. Onion Over VPN vs Double VPN
Double VPN (or Multi-Hop) is a feature offered by many premium VPN providers where your traffic is routed through two separate VPN servers instead of one.
- The mechanism: You → VPN Server 1 → VPN Server 2 → Internet.
- Anonymity vs. Privacy: Double VPN offers excellent privacy and is significantly faster than Tor. However, it relies entirely on trusting your VPN provider. Onion over VPN offers true anonymity by distributing trust across multiple random, volunteer-run nodes that are not owned by any single company.
- Verdict: If you need speed and high security, choose Double VPN. If you need maximum anonymity and want to hide your tracks from absolutely everyone (including your VPN provider seeing your destination), choose Onion over VPN.
6. Is Onion Over VPN legal?
This is the most common question I get from privacy-conscious users: Is adding a VPN to Tor going to land me in trouble? Is Onion Over VPN legal? The short answer is yes, Onion over VPN is legal in most of the world.
However, the longer answer depends entirely on where you are and how you use it. Let’s break down the legal nuances so you can use this technology with confidence.
6.1. Legal in most countries
In the vast majority of nations (including the US, UK, Canada, Australia, and most of Europe), using a VPN and Tor is completely legal.
- The right to privacy: These tools are considered legitimate software for protecting your personal data and online security.
- Legitimate use: Journalists use them to communicate with sources, activists use them to organize, and businesses use them to secure sensitive communications.
The caveat: Just because the tool is legal doesn’t mean illegal activities conducted through it are legal. Downloading copyrighted material, hacking, or accessing illegal marketplaces is still a crime, regardless of whether you are using Onion over VPN or not.
6.2. Countries where Tor is restricted
There are a handful of countries with strict internet censorship where accessing the Tor network is either blocked or legally risky.
- Examples: China, Russia, Iran, Turkey, and Belarus.
- The risk: In these regions, the government actively blocks access to Tor nodes. Using Tor can flag you for surveillance or lead to fines.
The role of VPN: Ironically, Onion over VPN is often safer in these countries than using Tor directly. Because you connect to a VPN server first, your local ISP (and by extension, the government) only sees encrypted VPN traffic, not a direct connection to the banned Tor network.
6.3. Is using Onion Over VPN suspicious?
Even in countries where it is legal, using Tor can sometimes raise eyebrows. Some ISPs flag Tor usage as “suspicious activity” because it is often associated with the Dark Web.
The solution: This is precisely why Onion over VPN is so valuable. By wrapping your Tor connection inside a standard VPN tunnel, you effectively hide the fact that you are using Tor from your ISP. To them, it just looks like you are using a VPN for work or streaming – a much more common and accepted behavior.
Disclaimer: I am a tech expert, not a lawyer. Laws regarding encryption and anonymity tools change frequently. Always check your local regulations before using Tor or VPNs, especially if you are traveling to a country with strict internet controls.
7. Who should use Onion Over VPN?
In the world of cybersecurity, we use a concept called a “Threat Model”. Essentially, it asks: Who are you hiding from, and what happens if you get caught?
Onion over VPN is a heavy-duty tool. For the average person, it is likely overkill. However, for specific groups facing high-level threats, it is a necessity. Here is a breakdown of who actually needs this level of protection.
Quick Check: Is Onion Over VPN right for you?
To make your decision easier, I have compiled this quick comparison based on common real-world scenarios.
| User scenario | Suitability | Why? |
| Whistleblowers & Journalists | Essential | Extremely slow speeds; the Tor network is not designed for high bandwidth. |
| Accessing Dark Web (.onion) | Recommended | Prevents malicious entry/exit nodes from seeing your real IP. |
| Bypassing Censorship (China, Russia, etc.) | Recommended | Masks Tor traffic as standard VPN traffic to bypass firewalls. |
| General Privacy (Hiding from ISP) | Overkill | A standard VPN is sufficient, faster, and easier to use. |
| Torrenting / P2P | Avoid | Buffering will be constant due to an 80-90% speed loss. |
| Streaming (Netflix, YouTube) | Avoid | Buffering will be constant due to 80-90% speed loss. |
| Online Banking & Shopping | Avoid | High risk of account freezing (banks flag Tor exit nodes as fraud). |
Bottom Line: If your safety depends on anonymity, use Onion over VPN. If you just want privacy and convenience, stick to a standard VPN.
7.1. Journalists, Activists, and Whistleblowers
If you are communicating with sensitive sources, organizing protests in restrictive regimes, or leaking evidence of corruption, your digital footprint can put lives at risk.
- The threat: State-level surveillance agencies often monitor internet traffic for Tor usage to identify dissidents.
- The solution: By using Onion over VPN, you hide the fact that you are using Tor from your local ISP and government. This allows you to use anonymous communication tools (like SecureDrop) without flagging yourself as a target.
7.2. Security researchers accessing the Dark Web
The Dark Web isn’t just for illegal activity; it is a vital resource for cybersecurity professionals analyzing malware, data breaches, and underground marketplaces.
- The threat: Many .onion sites are hostile. They may contain scripts or exploits designed to de-anonymize visitors by tricking their browser into revealing their real IP address.
- The solution: Even if a malicious site manages to bypass the Tor browser’s protections, the VPN layer ensures that the IP address revealed is that of the VPN server, not your home or office connection.
7.3. Users in high-censorship regions
For citizens living in countries with “Great Firewalls” (like China, Russia, or Iran), accessing the open internet is a daily struggle.
- The threat: Direct connections to the Tor network are often blocked by national firewalls. Attempting to connect can lead to internet service suspension or questioning by authorities.
- The solution: A VPN acts as a bridge. It encrypts your traffic so it looks like standard HTTPS data, bypassing the firewall and allowing you to connect to the Tor network safely from the other side.
7.4. Who SHOULD NOT USE it
I want to be very clear: Most people do not need Onion over VPN. If you fall into the categories below, a standard VPN is faster, cheaper, and sufficient.
- Streamers & Gamers: The speed loss (often 90%+) makes Netflix buffering unbearable and online gaming impossible.
- Online Banking & Shopping: Banks often flag Tor Exit Nodes as suspicious and will freeze your account if you try to log in. Standard HTTPS encryption is enough here.
- Casual Browsers: If you just want to stop Google from tracking your ads or hide your browsing history from your ISP, a standard high-quality VPN is perfectly adequate and much faster.
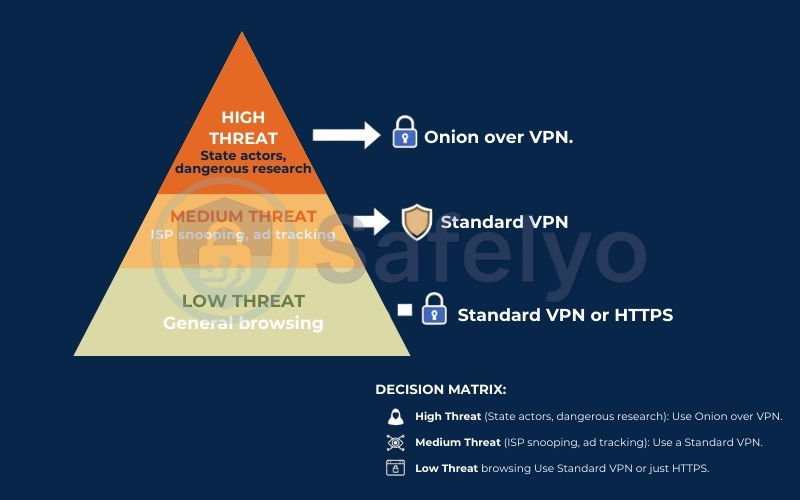
Decision Matrix:
- High Threat (State actors, dangerous research): Use Onion over VPN.
- Medium Threat (ISP snooping, ad tracking): Use a Standard VPN.
- Low Threat (General browsing): Use a Standard VPN or just HTTPS.
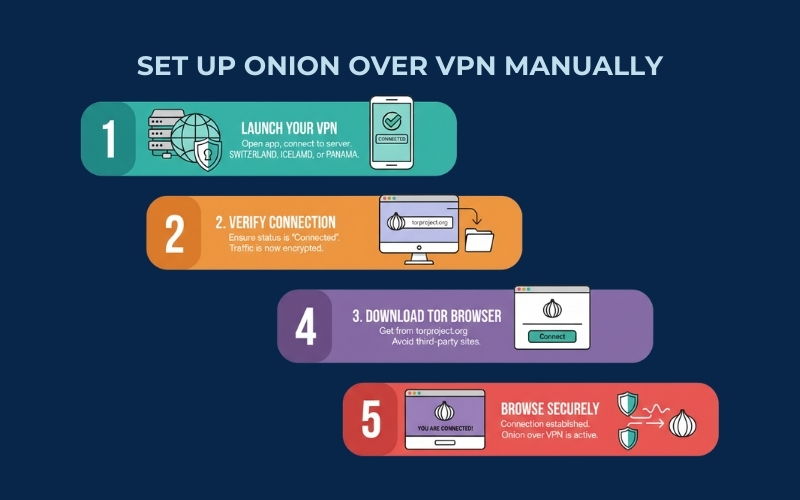
8. How to set up Onion Over VPN
Setting up Onion over VPN effectively requires choosing the right method for your needs. In my experience, you have two main paths: The Manual Method (using the official Tor Browser) and the Integrated Method (using a VPN’s built-in Tor feature).
Before we dive into the steps, here is a quick summary to help you decide which method fits your security model:
| Feature | Method 1: Manual Setup | Method 2: Integrated (Built-in) |
| Best For | Maximum Anonymity & Anti-Fingerprinting | Convenience & Accessing .onion sites quickly |
| Required Tools | VPN App + Tor Browser | VPN App only (Specialty Servers) |
| Security Level | ⭐⭐⭐⭐⭐ (Highest) | ⭐⭐⭐ (Medium – Fingerprinting Risk) |
| Complexity | Medium (Two separate apps) | Low (One click) |
| Browser | Tor Browser (Recommended) | Standard Browser (Chrome/Safari) |
8.1. Method 1 – Manual Setup
This is the gold standard for privacy. By using the official Tor Browser, you not only hide your IP but also blend in with millions of other Tor users to defeat browser fingerprinting.
- Launch your VPN: Open your VPN application and connect to a server.
- Tip: Choose a location with strong privacy laws (e.g., Switzerland, Iceland, Panama).
- Verify Connection: Ensure the VPN status is “Connected” or “Protected”. Your internet traffic is now encrypted.
- Download Tor Browser: Go to the official Tor Project website (torproject.org) and download the browser. Never download it from third-party sites.
- Open Tor Browser: Launch the application and click “Connect”.
- Browse Securely: Once the connection is established (indicated by a purple screen or the Tor homepage), you are successfully routing Onion over VPN.
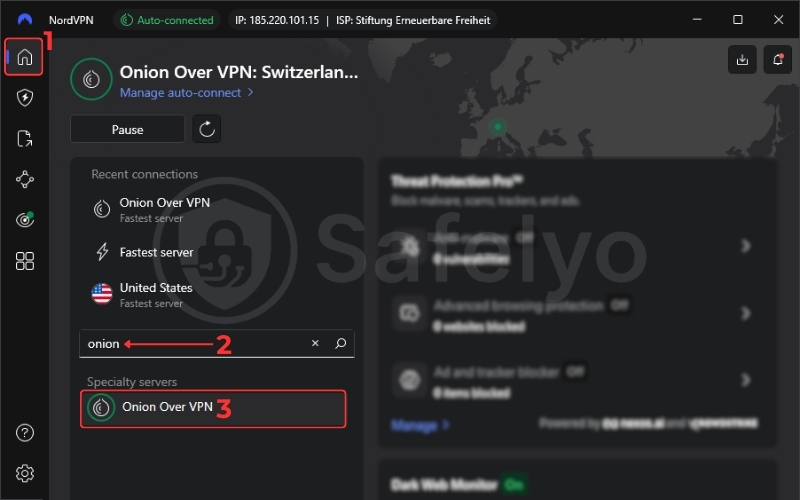
8.2. Method 2 – VPN with Built-in Onion Servers
Some premium providers (like NordVPN or Surfshark) offer “Onion over VPN” specialty servers. This routes all your device’s traffic through the Tor network automatically, allowing you to access .onion sites using your regular browser.
- Open your VPN App: Navigate to the server list and look for “Specialty Servers” or “Onion over VPN”.
- Select a Server: Click to connect. The VPN handles the Tor routing in the background.
- Browse the Web: You can now use Chrome, Safari, or Edge to access the Tor network.
- Warning: While convenient, standard browsers are unique and easily “fingerprinted” by advertisers. Use this method only for casual access to .onion sites, not for high-stakes anonymity.
8.3. Verification Checklist
Never assume your setup is working perfectly. Use this quick checklist to verify your connection before you start browsing.
| Action Step | Expected Result | Verified? |
| 1. Connect VPN | VPN app shows “Connected” / Green Shield. | [ ] |
| 2. Check VPN IP | Visit whatismyipaddress.com. Location matches VPN server (e.g., Switzerland). | [ ] |
| 3. Connect Tor | Open Tor Browser (Method 1) or Connect to Onion Server (Method 2). | [ ] |
| 4. Check Tor IP | Visit check.torproject.org. Message: “Congratulations. This browser is configured to use Tor”. | [ ] |
| 5. IP Mismatch | The IP address in Step 4 is different from Step 2. | [ ] |
| 6. WebRTC Leak | (Method 2 only) WebRTC is disabled in browser settings to prevent IP leaks. | [ ] |
9. Does Onion Over VPN guarantee anonymity?
If you are looking for a simple “Yes” or “No”, the honest answer from any cybersecurity expert is: No. Nothing guarantees 100% anonymity.
While Onion over VPN is arguably the strongest privacy configuration available to civilians, it is not a magic wand. Anonymity is not a switch you flip; it is a spectrum of difficulty for someone trying to find you. Here is exactly where this setup stands strong and where the cracks can still appear.
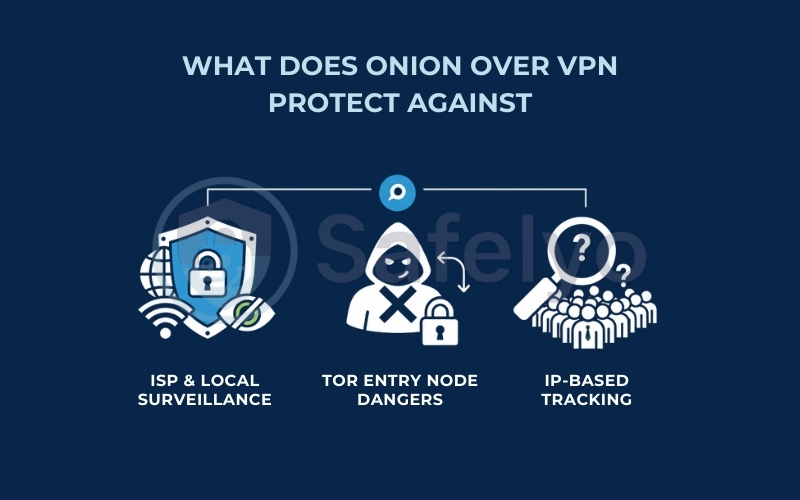
9.1. What it protects against
For almost all threats, this setup provides a near-impenetrable barrier.
- ISP & Local Surveillance: Your ISP, local network administrator (like a university or employer), and even local government surveillance cannot see that you are using Tor. They hit a wall of VPN encryption.
- Tor Entry Node Dangers: As mentioned earlier, the first node in the Tor network never sees your real IP address. You are protected from malicious volunteers trying to log user data at the entry point.
- IP-Based Tracking: Websites you visit see the IP of a Tor Exit Node, which changes frequently and is shared by thousands of people. You become a needle in a massive haystack.
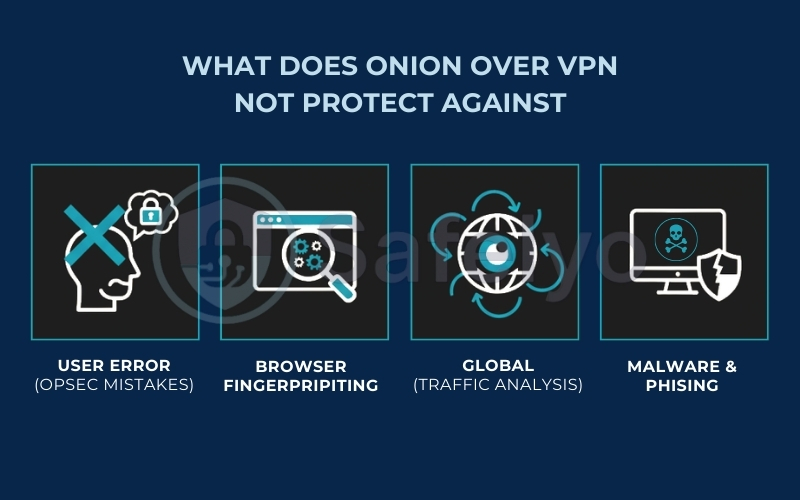
9.2. What it does not protect against
Even the thickest armor has gaps, and in the digital world, those gaps are usually you or the limitations of the technology itself.
- User Error (OPSEC Mistakes): This is the #1 reason anonymity fails.
- Example: If you use Onion over VPN to log into your real Facebook or Gmail account, you have instantly de-anonymized yourself. You just told Facebook: “Hi, I am [Your Name], and I am currently using Tor IP [X]”.
- Browser Fingerprinting: Websites run scripts to gather data about your device (screen resolution, battery level, installed fonts). If you are unique enough, they can track you across the web without needing your IP address.
- Solution: Always use the official Tor Browser and keep the window at its default size. Never maximize it.
- Global Adversaries (Traffic Analysis): If a powerful entity (like the NSA or Five Eyes intelligence alliance) can monitor both your entry into the VPN/Tor network and your exit from it, they can theoretically use statistical analysis to correlate the timing of data packets and identify you. While extremely difficult and expensive, it is mathematically possible.
- Malware & Phishing: Onion over VPN encrypts your connection, not your files. If you download a PDF infected with malware from the Dark Web, it can execute on your computer and send your real IP address directly to a hacker, bypassing your VPN/Tor setup entirely.
The Reality Check: Onion over VPN makes you incredibly difficult to track – prohibitively so for advertisers, hackers, and standard surveillance. However, if you are a high-value target (e.g., a state enemy), do not assume you are invisible. Your behavior (OPSEC) matters more than your tools.
10. Performance & speed: What to expect
If there is one “catch” to using Onion over VPN, this is it. In the world of networking, anonymity and speed are often inversely proportional: the more layers of encryption you add, the slower your connection becomes.
With Onion over VPN, you aren’t just adding one layer; you are routing your traffic through a VPN server plus three random volunteer nodes around the world. The result is a significant drop in performance.
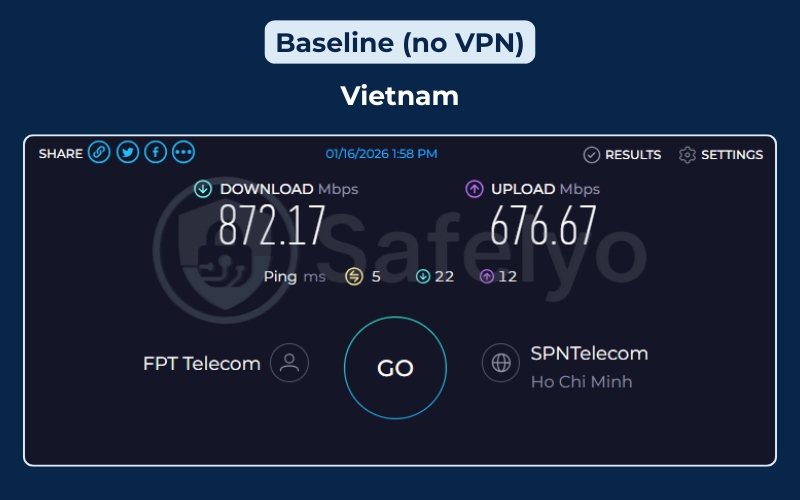
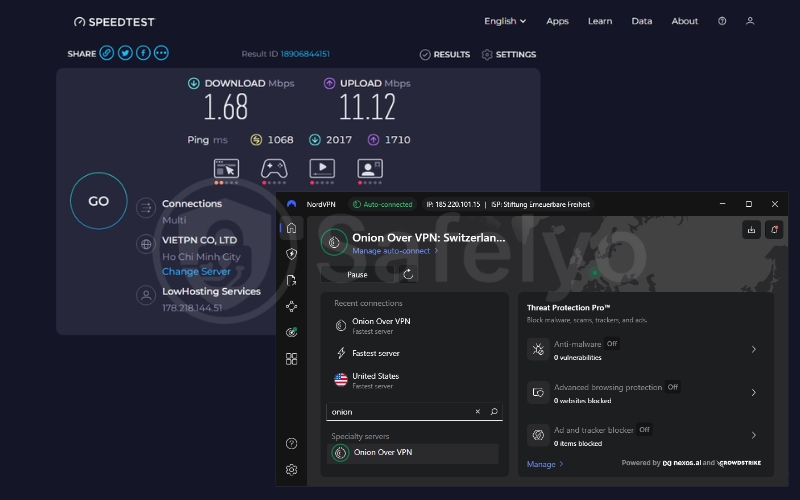
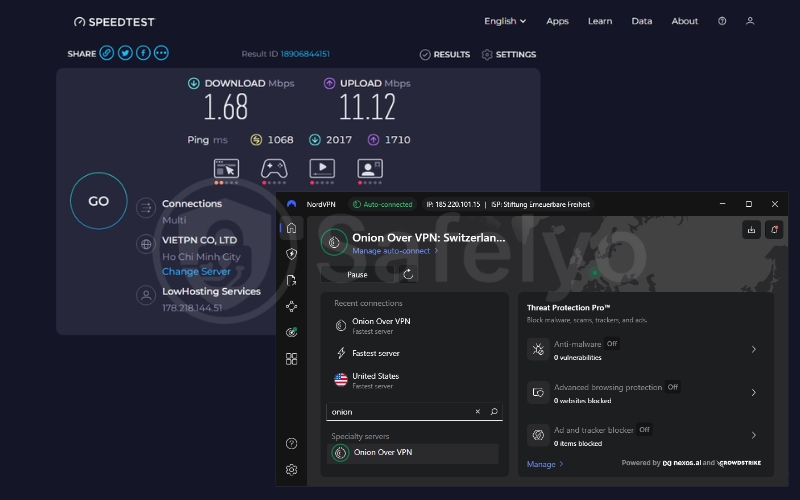
To give you a realistic picture, I ran a speed test on a high-speed fiber connection and compared it directly to a connection routed through a NordVPN “Onion Over VPN” specialty server.
Real-World Test Results
Here is the data from my testing session (Mar 2026):
| Metric | Baseline (No VPN) | Onion Over VPN | Impact |
| Download Speed | 872.17 Mbps | 1.68 Mbps | ~99.8% Drop |
| Upload Speed | 676.67 Mbps | 11.12 Mbps | ~98.3% Drop |
| Ping (Latency) | 5 ms | 1068 ms | >20,000% Increase |
As you can see from the numbers, the impact is massive. My download speed plummeted from a blazing 872 Mbps to just 1.68 Mbps. While the baseline speed is enough to stream 4K video on dozens of devices simultaneously, the Onion over VPN speed is barely enough to load a standard webpage or stream a low-quality video buffer-free.
Furthermore, the Ping (1068 ms) is critical to note. A ping over 1 second means there is a noticeable delay between clicking a link and the browser actually acknowledging the request.
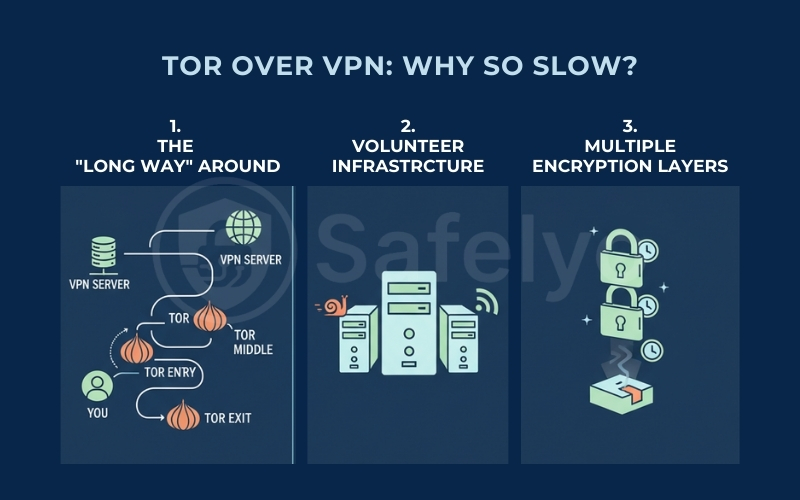
Why is it so slow?
You might be wondering why a fast VPN connection suddenly turns into a crawl when Tor is added. There are three technical reasons for this bottleneck:
- The “long way” around: In a standard connection, your data travels directly from A to B. With Onion over VPN, your data travels from You → VPN Server → Tor Entry → Tor Middle → Tor Exit → Website. That is a massive geographical detour.
- Volunteer infrastructure: Unlike premium VPN servers, which are enterprise-grade data centers, Tor nodes are often run by volunteers on home computers or limited bandwidth connections. You are only as fast as the slowest node in your circuit.
- Multiple encryption layers: At every single “hop” in the Tor network, data must be decrypted and re-encrypted. This processing time adds up, resulting in the massive latency (ping) you see in the test results above.
Realistic use cases (What can you actually do?)
Given the speed of 1.68 Mbps, you need to adjust your expectations. This setup is NOT built for entertainment; it is built for survival and security.
- Feasible: Sending encrypted emails, reading text-heavy websites, secure messaging, accessing .onion sites, and whistleblowing.
- Impossible/Frustrating: 4K or HD streaming (Netflix/YouTube), online gaming (due to the 1000ms+ lag), or downloading large files.
Note: If you see speeds faster than this (e.g., 5-10 Mbps), consider yourself lucky. However, you should generally treat Onion over VPN as a tool for specific tasks where privacy outweighs patience, not as a daily driver for browsing the web.
11. FAQs about Onion over VPN (Tor over VPN)
Is Onion over VPN better than Tor alone?
Yes, for privacy from your Internet Service Provider. Using Tor alone means your ISP can see you are connecting to the Tor network. Onion over VPN encrypts your connection before it reaches Tor, hiding your Tor usage from your ISP entirely. It also protects your real IP address from potentially malicious Tor Entry Nodes.
Can my ISP detect Tor if I use Onion over VPN?
No. Because you connect to a VPN server first, your ISP only sees encrypted traffic traveling to that VPN server. They cannot see the data inside the tunnel, nor can they see that the data is subsequently being routed to the Tor network.
Is Onion over VPN safe for the dark web?
Yes, it is one of the safest methods for accessing .onion sites. If you encounter a malicious website on the dark web that tries to uncover your real IP address, the VPN layer ensures that the IP revealed belongs to the VPN server, not your home connection.
Can I use any VPN for Onion over VPN?
Technically, yes, if you use the manual method (connecting your VPN app, then opening the Tor Browser). However, for the integrated method (using a VPN’s built-in Tor servers), you need a premium provider that specifically offers this feature, such as NordVPN or Surfshark.
Does it hide my browsing from the government?
It hides your browsing from local government surveillance and your ISP. However, highly sophisticated global adversaries (like state intelligence agencies) conducting advanced traffic correlation attacks across the entire internet could theoretically trace a connection, though it is incredibly difficult and resource-intensive.
Is Onion over VPN the same as Double VPN?
No. A Double VPN routes your traffic through two separate servers owned by the same VPN company. Onion over VPN routes your traffic through one VPN server, and then through three randomly selected, volunteer-run nodes on the Tor network. Double VPN is faster but relies on trusting one company; Onion over VPN is slower but distributes trust across a decentralized network.
12. Conclusion
Onion over VPN is undeniably one of the most powerful privacy configurations available today. By combining the encrypted tunnel of a VPN with the decentralized anonymity of the Tor network, you create a formidable defense against surveillance, censorship, and malicious actors.
However, this level of protection comes at a steep cost to your internet speed. For the vast majority of users – those looking to secure public Wi-Fi, hide their browsing history from their ISP, or bypass simple geo-blocks – a standard, high-quality VPN is more than enough. Onion over VPN should be reserved for those who truly need it: Journalists, activists, researchers, and individuals living under oppressive regimes where anonymity is not just a preference, but a necessity for safety.
At Safelyo, we believe in equipping you with the right tools for your specific digital lifestyle. If you decide this advanced setup is overkill for your daily browsing, explore our comprehensive VPN Guides to find the perfect, high-speed solution to keep your online life private and secure without sacrificing performance.