You pay for a Virtual Private Network (VPN) subscription every month, but you might wonder if it really works. When you turn it on, does a VPN encrypt data effectively, or are those just marketing claims? We understand the skepticism. It is hard to trust an invisible process happening in the background of your computer or phone.
This guide breaks down exactly how that hidden protection works and shows you how to test the connection yourself for actual proof.
Key takeaways:
- VPNs successfully scramble traffic passing from your device to the VPN server.
- Encryption does not cover the journey from the VPN server to the final website.
- Modern services use AES-256 and ChaCha20 standards to secure your information.
- You can manually verify your safety using free DNS and WebRTC leak tests.
1. Does a VPN encrypt data?
Yes. A VPN encrypts your data by converting your readable internet traffic into a scrambled, unreadable format.
When you activate the software, it applies a complex mathematical algorithm to your information before it ever leaves your device. This process changes plain text (like your search queries, website requests, or private messages) into ciphertext.
Ciphertext is simply a random sequence of characters that is completely unreadable without the correct decryption key. Even the world’s most powerful supercomputers would take trillions of years to crack AES-256 encryption by brute force.
As this scrambled data travels through your local Wi-Fi network and the infrastructure of your Internet Service Provider (ISP), it remains completely protected. Even if a network administrator or a local hacker intercepts your connection, they will only see meaningless code. The information is only unscrambled when it safely reaches the provider’s remote server, effectively hiding your browsing activity from all outside observers.
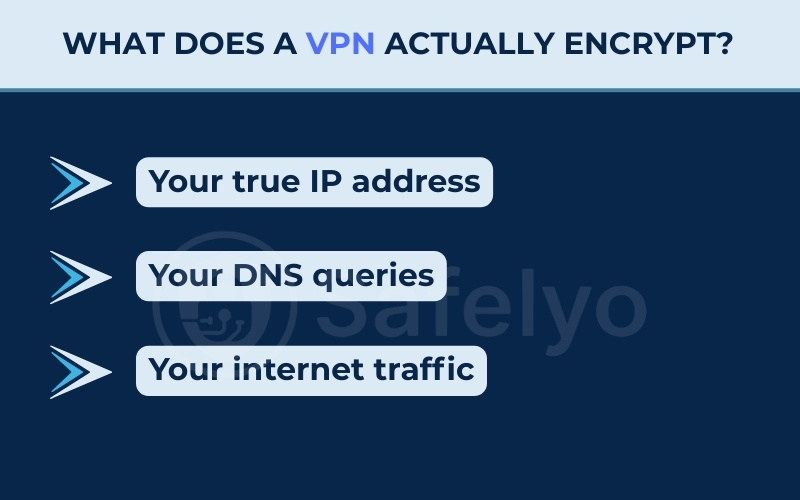
2. What does a VPN actually encrypt?
When you connect to a server, the software protects several specific pieces of information. It creates a secure shield around your device to protect the following data:
- Your true IP address: This hides your actual physical location from the websites you visit.
- Your DNS queries: This hides the invisible requests your browser makes when you type in a website address.
- Your internet traffic: This scrambles the actual contents of your messages, searches, and file downloads.
This protection is especially valuable on shared networks. If you are curious about how does a VPN encrypt data on public wi-fi, the process remains the same. The secure shield activates before the data even reaches the coffee shop router. By securing the data early, it prevents local hackers from intercepting your passwords or reading your private messages.
3. How does VPN encryption work?
The encryption process might seem complicated, but it actually follows a clear, logical sequence. The software creates a private digital tunnel between your computer and the remote server.
Here is the four-step process used to build that secure tunnel:
Step 1: The asymmetric handshake.
Before any information moves, your device and the server must verify each other. They check digital IDs to confirm they are talking to the correct machine. This authentication prevents malicious servers from tricking your computer into handing over private data.
Step 2: Key exchange.
Once authenticated, both sides agree on a specific secret code. This cipher acts as a set of rules for scrambling the data. Only your device and the trusted server know this specific code. This ensures no third party can translate the information later.
Step 3: Symmetric encryption.
Now the actual data transfer begins. Your device uses the agreed-upon cipher to scramble your internet traffic into unreadable text. The remote server receives this scrambled package. It then uses the exact same key to unscramble the text back into a usable format.
Step 4: Integrity checks.
Finally, the software applies a digital seal to the data packets. This seal acts like tamper-evident tape on a shipping box. If anyone tries to alter the data while it travels, the server notices the broken seal. It will then drop the connection instantly to protect you.
4. Encryption standards: AES-256 and ChaCha20
VPN providers use specific mathematical models to scramble your information. The most common industry standard is AES-256. The number 256 means the cryptographic key has a massive number of possible combinations.
To put that in perspective, a supercomputer would need billions of years to guess the correct combination. It is the same standard used by governments and military organizations to protect classified files.
Another popular standard is ChaCha20. This cipher is the native encryption method for the WireGuard protocol. ChaCha20 is highly efficient. It often runs faster on mobile devices than AES-256 while providing the same level of exceptional security for everyday browsing.
Post-Quantum Encryption explained
While standard encryption is highly secure today, future quantum computers could potentially break it. Hackers may even collect encrypted data now to decrypt it years later when this technology advances.
To counter this theoretical threat, some providers are already upgrading their software with quantum-resistant cryptography, a new generation of algorithms designed to withstand immense processing power.
5. VPN protocols: Balancing speed and security
A VPN protocol acts as a set of instructions for building your secure tunnel. Because these rules prioritize speed, stability, or raw security differently, choosing the right setting in your app can feel confusing. We compiled a simple comparison to help you decide based on your specific needs:
| Protocol | Speed | Security Level | Best Use Case | Still Recommended? |
|---|---|---|---|---|
| WireGuard | Very Fast | High | Streaming and gaming | Yes |
| OpenVPN | Average | Very High | Maximum privacy tasks | Yes |
| IKEv2 | Fast | High | Mobile devices switching networks | Yes |
| L2TP/IPsec | Slow | Medium | Older device compatibility | Rarely |
| PPTP | Very Fast | Very Low | None | No |
You should strictly avoid the PPTP protocol. It is an obsolete standard containing known vulnerabilities. Hackers can exploit these weaknesses easily. Most modern services have removed it entirely to keep users safe.
From a practical standpoint, you rarely need to overthink these choices. Most VPN apps feature an “Automatic” protocol setting. For normal everyday use, leaving the app on Auto is highly recommended. The software will dynamically select the best protocol based on your current network conditions, ensuring a stable connection without any manual tweaking.
Kill Switch = Encryption safety net
Sometimes your internet connection drops unexpectedly. If this happens, your device might try to reconnect using your normal internet provider. A kill switch prevents this by instantly blocking all internet traffic until the secure tunnel is re-established.
6. Do free VPNs encrypt data securely?
Yes, most free applications do encrypt your data securely. However, the level of overall privacy they offer can vary significantly.
Running secure servers requires significant financial resources. Because free providers do not charge a subscription fee, they must find alternative ways to cover their operating costs. This is where the privacy risks usually begin.
While the encryption effectively protects your data from outside hackers on a local network, it does not hide your activity from the VPN provider itself. To make a profit, some lower-quality free services log your connection data or browsing habits and share this information with advertising networks.
Fortunately, not all free services resort to selling your data. If you only need basic protection for simple tasks like checking emails on public Wi-Fi, there are reliable options available. The Best free VPN services will secure your connection properly without compromising your privacy. Instead of selling your data, they cover costs by restricting your data allowance and server locations.
Regardless of your choice, it is always important to read the privacy policy carefully to ensure the provider does not monetize your information.
7. VPN encryption vs. HTTPS: What is the difference?
You might notice a small padlock icon next to website names in your browser. This padlock represents HTTPS. This is a different type of encryption that specifically secures the transaction between your web browser and the website you are visiting.
HTTPS protects sensitive details like credit card numbers or login passwords. However, it only applies to the specific browser tab you have open. It does not cover other applications on your device.
A VPN works on a much broader level. It encrypts the entire data route from your device to the remote server. This includes background application updates, DNS requests, and all browser traffic.
The VPN hides your overall internet activity, while HTTPS secures the specific contents of your web pages.
8. What a VPN does not encrypt
It is important to understand the limits of this technology. A VPN does not provide absolute anonymity on the internet. Here is a list of what remains unprotected:
- Traffic beyond the server: Once your data reaches the remote server, it must be decrypted before traveling to the final website. The VPN does not encrypt this final leg of the journey (this relies entirely on HTTPS).
- Malicious downloads: The software cannot protect you from human error. It will not secure your device if you voluntarily download a virus or malware.
- Phishing attacks: It cannot stop you from typing your personal details or passwords into a scam website.
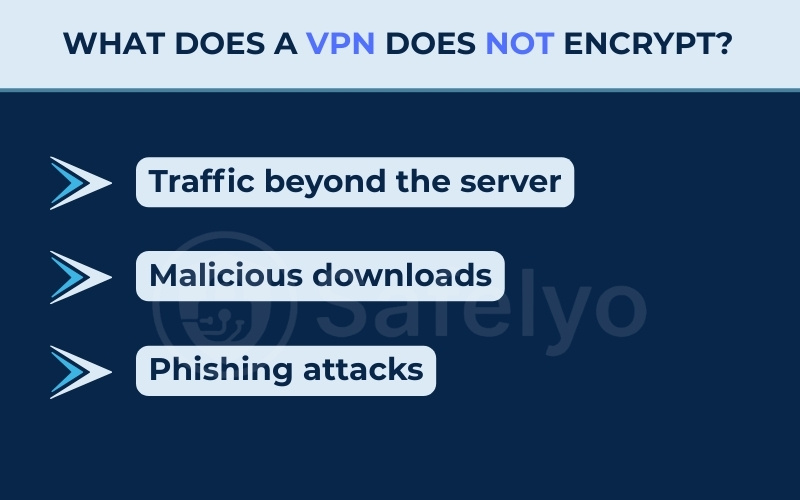
Lastly, while the encryption tunnel itself is highly secure, no system is entirely foolproof. If you are wondering Can VPN be hacked, the reality is that the servers themselves can sometimes be compromised, which is why choosing a reputable provider is so critical.
9. How to verify your VPN is encrypting
You do not have to blindly trust your software provider. You can manually test your connection to ensure the encryption tunnel is working correctly. Follow these simple guides to confirm your data remains hidden.
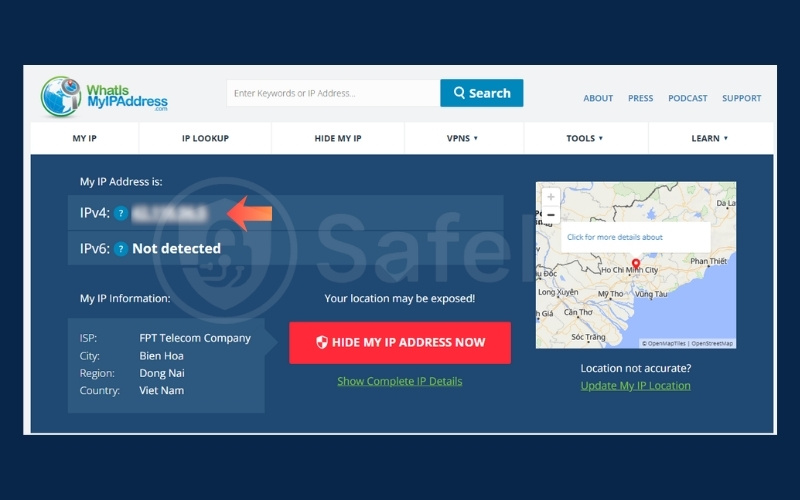
9.1. Step 1: Check your public IP address
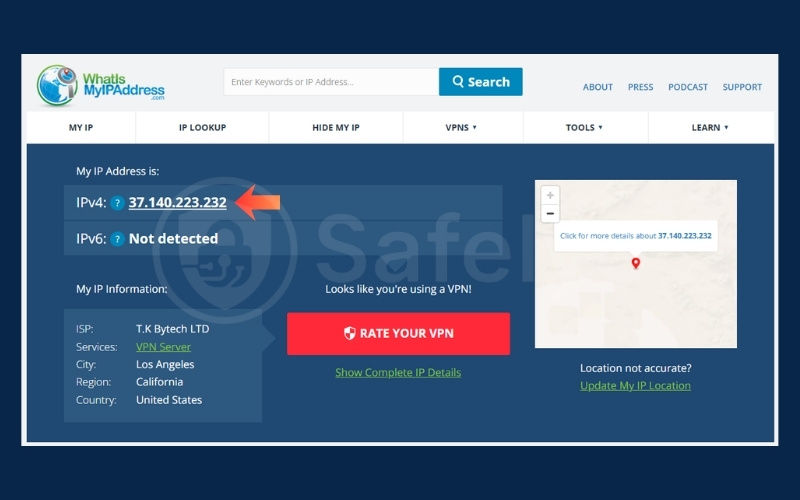
You can quickly verify that your traffic is routing properly by checking your visible location.
- Turn off your VPN completely.
- Open a web browser and go to whatismyipaddress.com.
- Write down the number that appears on the screen.
- Turn your VPN on and connect to a server in a different country.
- Refresh the webpage. The number should change completely, proving your new location is active.
9.2. Step 2: Run a DNS leak test
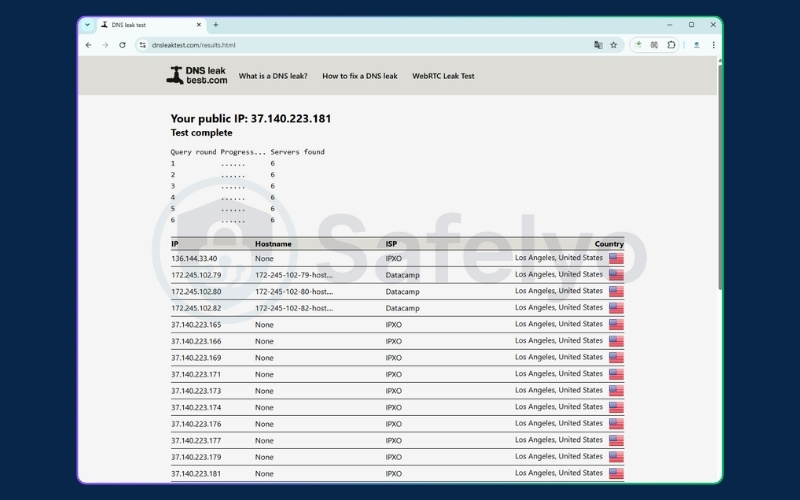
A DNS leak happens when your device accidentally sends DNS requests outside the secure tunnel. Running this test confirms whether your internet service provider can still see which websites you are visiting even while the VPN is active.
Here is how to check for that flaw:
- Keep your VPN turned on and connected.
- Go to a free testing website like DNSLeakTest.com.
- Click the “Standard Test” or “Extended test” button.
- Look at the results on the screen. If you see your actual physical location or your real internet service provider listed, your connection is leaking data. If it only shows the VPN’s server location, you are safe.
9.3. Step 3: Run a WebRTC leak test
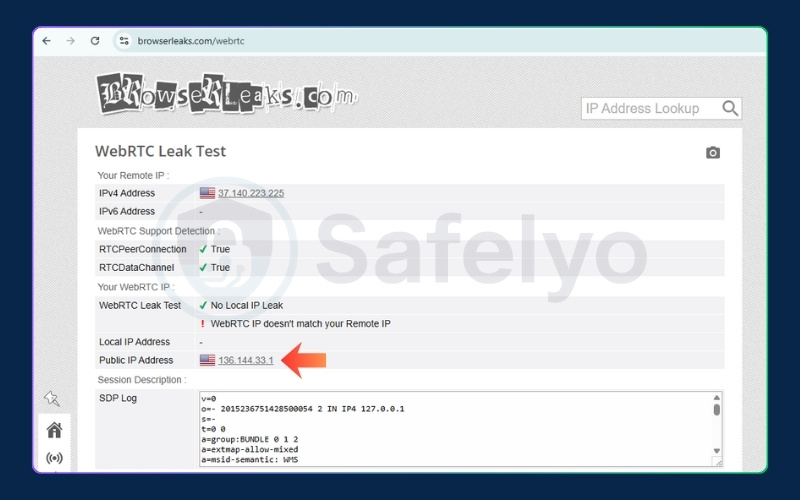
WebRTC is a browser feature used for voice and video chats, but it can accidentally reveal your true IP address.
- Keep your VPN connected.
- Visit a testing site like BrowserLeaks.com/webrtc.
- Find the “Public IP Address” section on the page.
- The result should only display the IP address of your remote server. If your real, home IP address appears here, you have a WebRTC leak.
9.4. Step 4: Inspect traffic with packet sniffers (advanced)
If you want visual confirmation that your data is scrambled, you can use network analysis tools to look at the raw information.
- Download a free network analysis tool like Wireshark.
- Open the program and start capturing your Wi-Fi network traffic.
- Turn on your VPN and browse a few random websites.
- Look at the captured data packets in the Wireshark dashboard. You will see that the text looks like random, unreadable characters, confirming the encryption is active.
Verifying your secure tunnel is a great first step. Since a VPN is just one piece of the privacy puzzle, we recommend reading our detailed guide on how to stop being tracked online to further protect your digital footprint.
10. FAQs about does a VPN encrypt data
Here are clear answers to common questions about internet security tunnels.
Do VPNs actually encrypt your data?
Yes. They scramble your internet traffic into unreadable text using complex mathematical standards like AES-256. This secure tunnel prevents local network administrators and internet service providers from monitoring your browsing habits.
How do I know if my VPN is encrypted?
You can verify your protection by running free online diagnostics. Check your public IP address, run a DNS leak test, and perform a WebRTC leak test. This ensures your true location remains hidden.
What is the downside to using a VPN?
The primary downside is a potential reduction in internet speed. The process of scrambling and unscrambling data requires processing power. It also adds physical distance to your connection route, which can cause minor delays.
Is it illegal to watch Netflix with a VPN?
Using a secure tunnel to watch Netflix breaks the streaming platform’s terms of service. However, it is not considered a legal offense or a crime in most Western countries.
Does a VPN encrypt all traffic, or only some?
A standard setup routes all device traffic through the secure tunnel. However, many applications offer a split-tunneling feature. This allows you to choose specific apps to bypass the encryption and use your regular local network.
What does a VPN service use to transfer encrypted data between a device and the VPN server?
Services use specific sets of instructions called VPN protocols. Common examples include WireGuard, OpenVPN, and IKEv2. These protocols dictate how the tunnel is built and how data moves securely across the internet.
11. Conclusion
Understanding the exact boundaries of your software makes you a much safer internet user. While it is true that a VPN provides robust security, it is not a magic shield. It relies on synergy with HTTPS to fully protect your information across the web.
Now that you know the answer to does a VPN encrypt data, take a few minutes to test your own setup. Turn on your application and run a quick DNS leak test to ensure everything functions correctly.
For more detailed tutorials, explore the VPN Guides category available right here on Safelyo.