You search for a vacation spot, and shortly after, related flight and hotel ads begin appearing across your apps and browser. While it may seem like your devices are listening, this is simply the result of tracking technologies logging your clicks, searches, and browsing habits to understand your preferences.
You have options to limit this routine data collection. Regaining control of your digital privacy is a manageable process once you learn how to stop being tracked online using practical strategies.
In this guide, we will explore how tracking works, the signs that your activity is being monitored, and 17 actionable steps to secure your personal data.
-
Switch to anti-tracking browsers
Download and install privacy-focused browsers like Brave or Firefox → Set to “Strict” tracking protection.
-
Connect via a VPN
Subscribe to a trusted VPN service → Connect to a server to mask your IP address and encrypt your traffic.
-
Install privacy extensions
Go to your browser’s extension store → Search for and add tools like uBlock Origin to block invisible data collectors.
-
Disable third-party cookies
Open your browser settings → Navigate to Privacy & Security → Select the option to block all third-party cookies.
-
Delete data from brokers
Submit manual opt-out requests directly to data brokers or use automated tools like Incogni or DeleteMe.
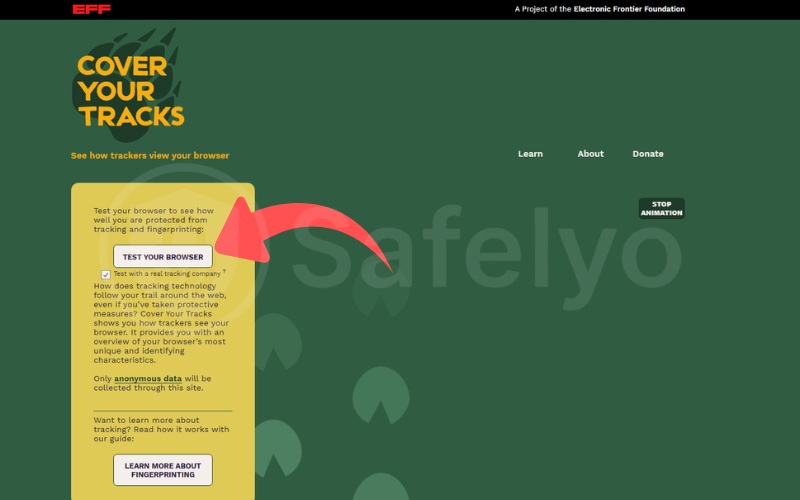
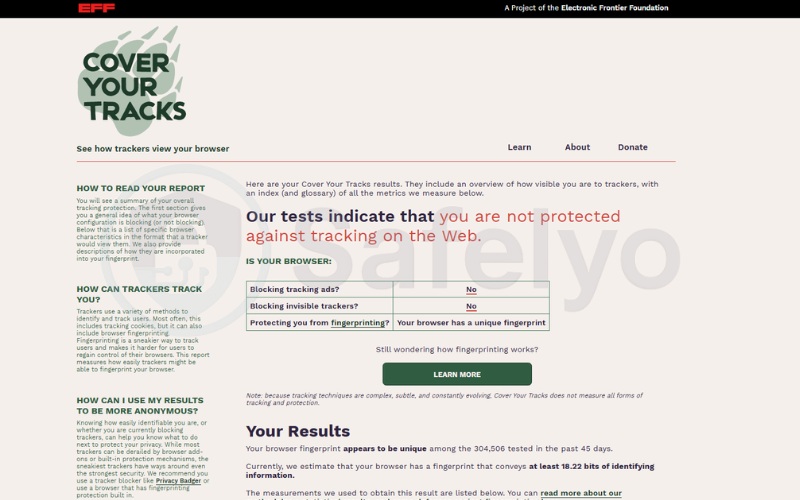
1. Test your browser fingerprint
Before you start blocking trackers, it helps to see exactly what websites can see about you. The Electronic Frontier Foundation (EFF) offers a free diagnostic tool called Cover Your Tracks (https://coveryourtracks.eff.org/).
By running a quick test on their website, you can see if your browser fingerprint is recognized as unique among millions of users. If the test shows that you have a unique fingerprint, it means companies can easily track you across the web, even if you clear your cookies. This is a great starting point to understand your baseline privacy before applying the fixes below.
2. How to stop being tracked online: 17 proven ways
The good news is that you don’t need to be a cybersecurity expert to protect your online privacy. If you’re asking how to stop being tracked online, there are practical tools and habits that can reduce your digital footprint without sacrificing everyday convenience. These methods range from simple browser tweaks to more advanced privacy systems.
Importantly, you don’t have to implement all 17 methods at once. We recommend reviewing the strategies below and starting with the ones that seem most achievable for you. Every single layer of protection you add makes it significantly harder for trackers to monitor your personal life.
2.1. Use anti-tracking browsers (Brave, Firefox, Tor, Mullvad)
Switching to a privacy-focused browser can help reduce commercial data collection. Unlike some standard browsers that may allow extensive tracking by default, these alternatives are designed with built-in privacy features. Some widely used browsers for limiting online tracking include:
- Brave: Best for users who want a fast, “out-of-the-box” experience with automatic ad and tracker blocking.
- Firefox: A highly customizable open-source browser that offers strong privacy settings.
- Tor Browser: The gold standard for anonymity, routing your traffic through three layers of encryption.
- Mullvad Browser: A modern alternative to Tor that provides elite fingerprinting protection using a standard high-speed connection.
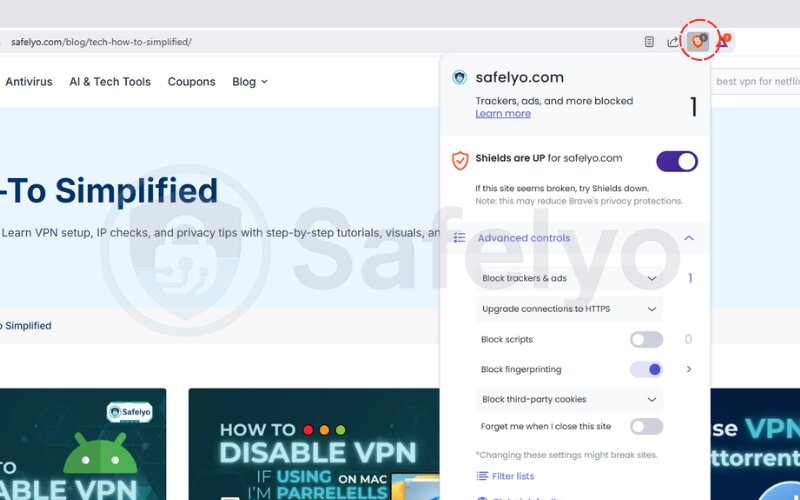
Setting up Brave:
- Go to the Brave website and download the browser.
- Install and open Brave.
- By default, Brave enables Shields, which block ads, trackers, fingerprinting scripts, and more.
- Click the lion icon next to the address bar to view or customize protection settings per site.
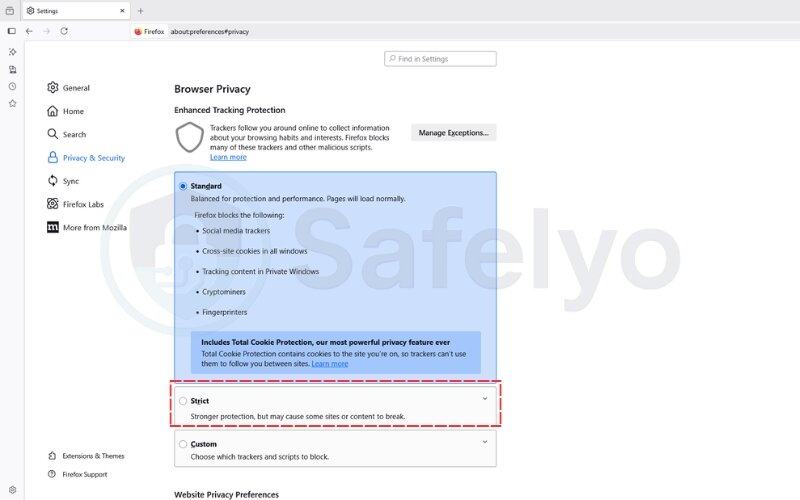
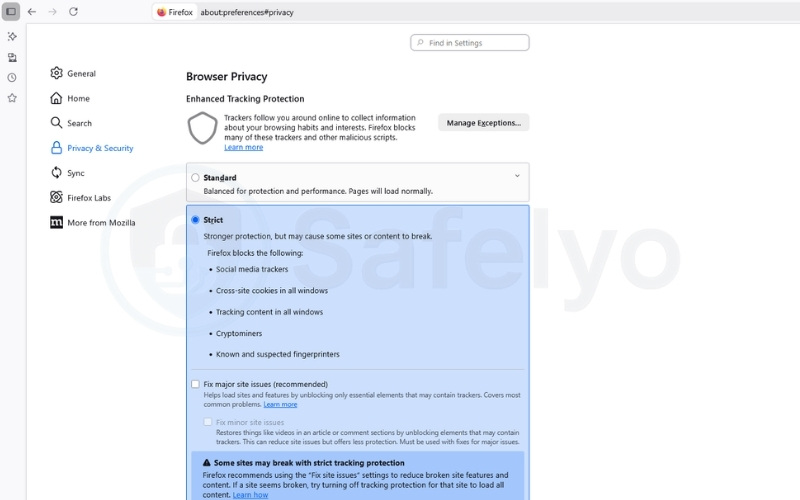
Setting up Firefox:
- Visit the Mozilla Firefox website.
- Install Firefox and launch it.
- Go to Settings → Privacy & Security.
- Under Enhanced Tracking Protection, select “Strict” mode to block most known trackers and scripts, making Firefox a reliable anti-tracking browser.
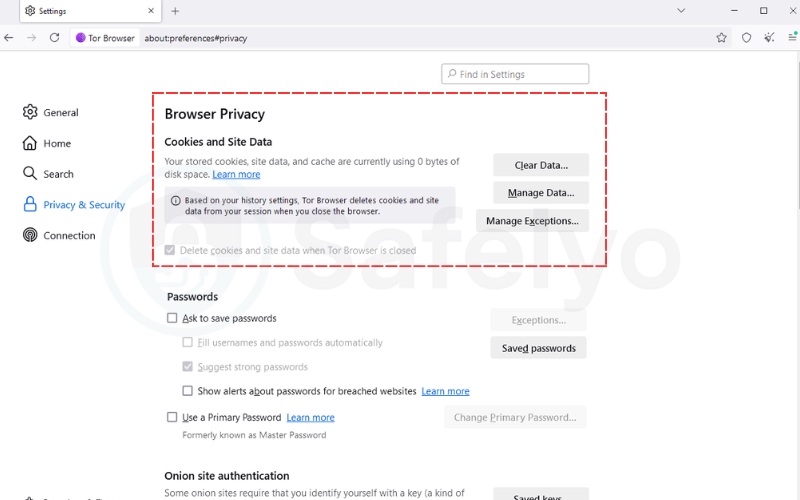
Setting up Tor Browser:
- Visit the Tor Project website (https://www.torproject.org/).
- Download and install the Tor Browser.
- Tor automatically routes your traffic through multiple encrypted layers, making it extremely difficult for anyone to track your location or browsing activity. It also clears all cookies and history upon closing.
Setting up Mullvad Browser:
- Visit the Mullvad website.
- Download and install the Mullvad Browser.
- Built in collaboration with Tor, it offers similar fingerprinting protections but without routing traffic through the Tor network, providing faster speeds while still effectively masking your online identity.
You may also be interested in this article: How to browse the web anonymously in 2025: Easy 4-step guide
2.2. Install tracker-blocking extensions
Even with a privacy-focused browser, adding tracking blockers gives you an extra layer of control. Tools like uBlock Origin, Ghostery, or Privacy Badger block invisible trackers that run in the background on many websites. These are essentially ad blockers that double as privacy shields. These tools can stop a web tracker from silently following your clicks across sites.
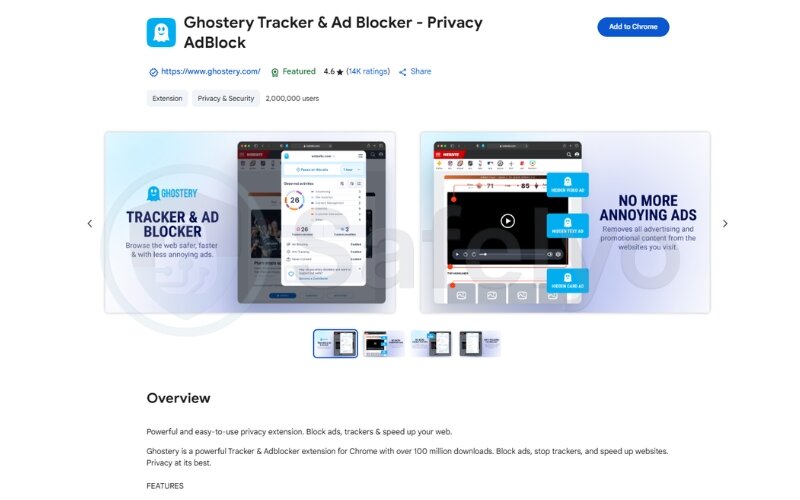
How to install Ghostery (on Chrome):
- Open Google Chrome and go to the Chrome Web Store.
- In the search bar, type “Ghostery”.
- Click “Add to Chrome”.
- Confirm the installation by clicking “Add Extension”.
- After installation, the Ghostery icon (a friendly ghost) will appear in your browser toolbar.
- Click the icon to view blocked trackers, adjust settings, or enable blocking modes.
2.3. Browse in private browsing mode
Private or incognito mode helps prevent your browser from saving your history, cookies, and form data. While it doesn’t stop websites from tracking you, it limits local data stored on your device. Pairing incognito with a private browser gives even stronger protection.
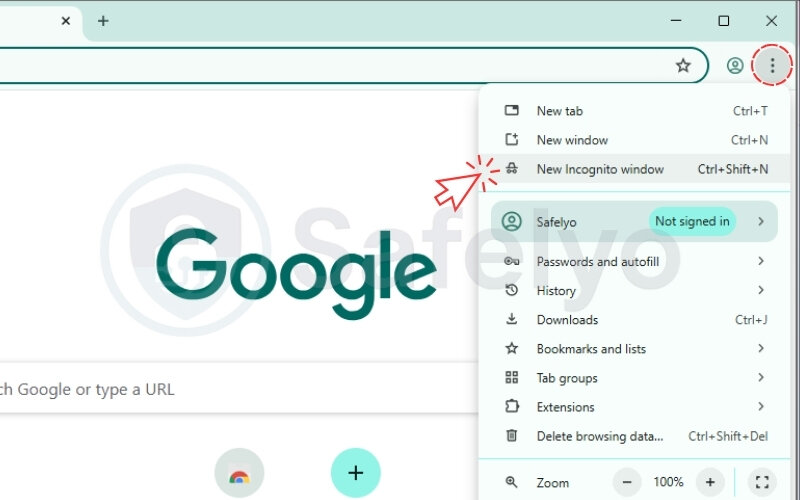
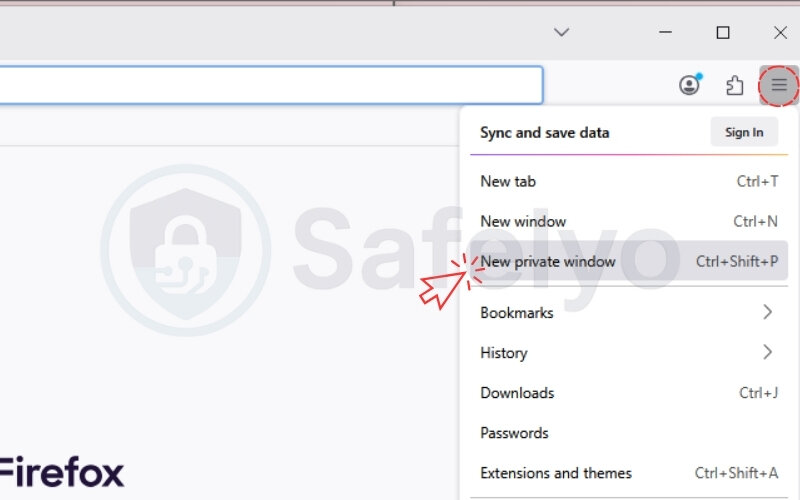
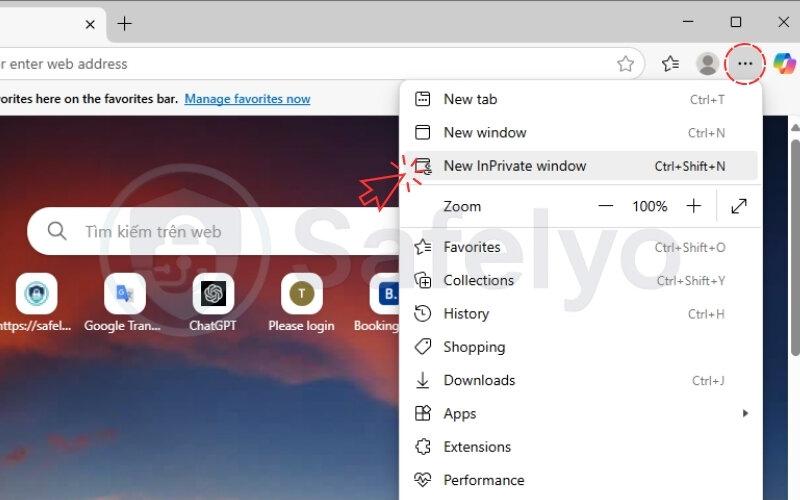
How to use private browsing:
- Chrome: Press Ctrl + Shift + N (Windows) or Cmd + Shift + N (Mac).
- Firefox: Press Ctrl + Shift + P or use the menu to select “New Private Window”.
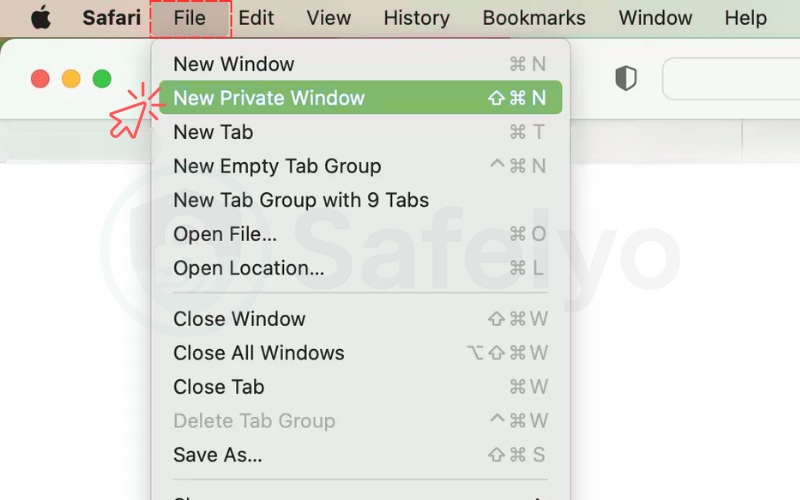
- Safari: Go to “File” and select “New Private Window”.
- Edge: Click the menu and select “New InPrivate window”.
When researching sensitive topics, using Incognito helps avoid personalized suggestions later.
2.4. Use a trusted VPN
A Virtual Private Network hides your Internet Protocol address and encrypts all internet traffic between your device and the web. This prevents websites, ISPs, and even public Wi-Fi operators from seeing your real location or tracking your online behavior.
Steps to use a VPN:
- Choose a reputable VPN provider like NordVPN, Surfshark, or ProtonVPN.
- Download and install the VPN app for your device.
- Open the app and log in.
- Connect to a server (preferably close to your actual location for better speed).
- Confirm it’s working by visiting a site like ipleak.net to check if your real IP is hidden.
2.5. Turn off ad personalization across accounts
Many platforms offer ad personalization by default. This allows them to use your behavior to target you with specific ads. While turning this off doesn’t stop all tracking, it reduces how your data is used. You should manually opt out of these features on your major tech accounts.
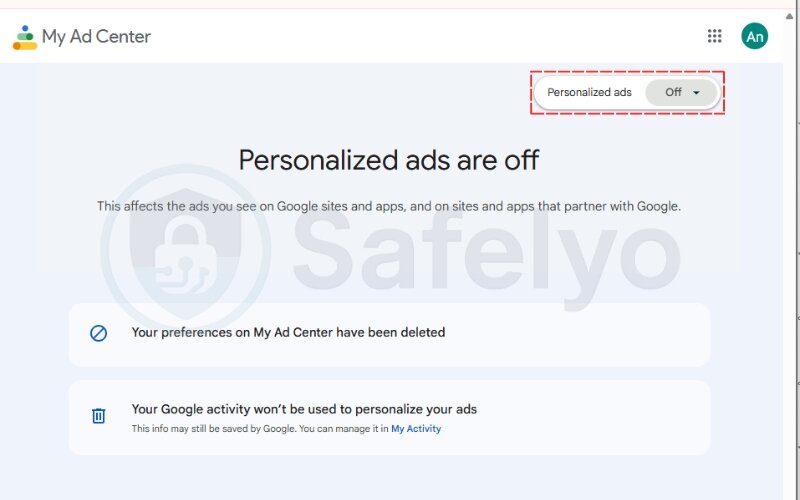
How to turn off Google Ad Personalization:
- Visit the Google My Ad Center website (https://myadcenter.google.com/).
- Sign in with your Google account.
- Toggle Ad Personalization to Off.
- Review the “My Activity” section and remove anything you don’t want associated with your profile.
For broader control across the web:
You can also visit optout.aboutads.info to opt out of targeted advertising from dozens of participating external ad networks. Opting out of major platforms often shifts the ads you see from eerily relevant to more generic ones.
2.6. Revoke unnecessary app permissions
Many apps request access to data they don’t actually need, like your camera, microphone, or location. Revoking these permissions limits how much personal information is shared in the background.
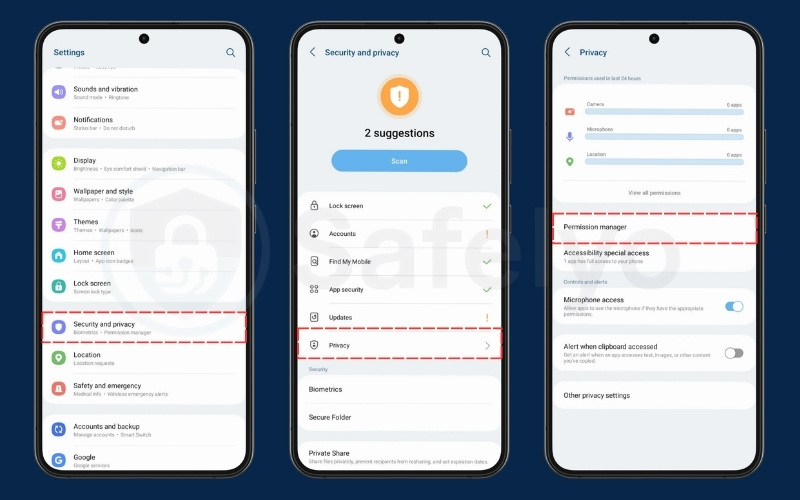
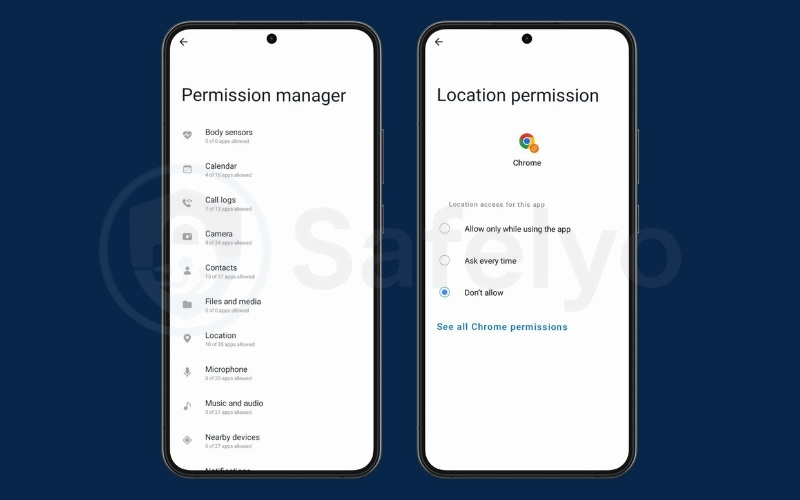
How to manage app permissions on Android:
- Go to Settings → Security and Privacy → Privacy → Permission Manager.
- Review permissions like Location, Microphone, and Contacts.
- Tap each one and select “Don’t allow” for apps that shouldn’t have access.
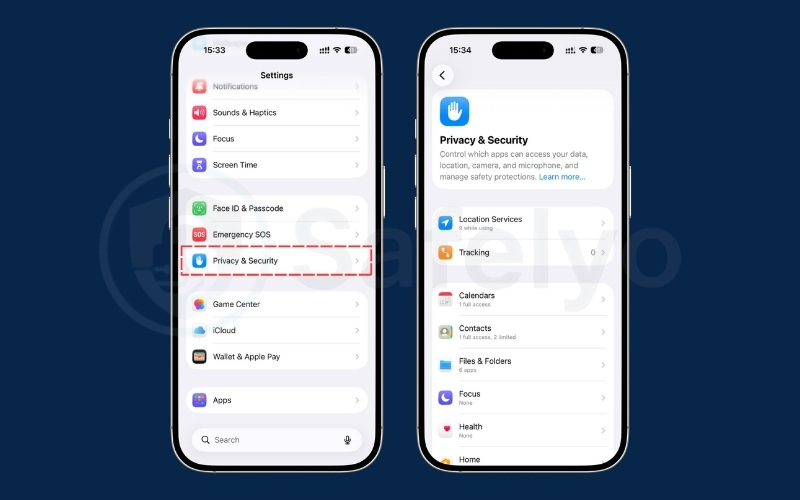
How to manage app permissions on iPhone:
- Go to Settings → Privacy & Security.
- Tap each category (e.g., Location Services, Microphone).
- Turn off access for apps that don’t need it.
2.7. Use search engines that don’t track you
Mainstream search engines like Google track your queries, clicks, and browsing behavior. Privacy-focused alternatives don’t log your searches or build a profile around you.
Top private search engines:
- DuckDuckGo: Blocks trackers and shows non-personalized results.
- Startpage: Uses Google search results but strips identifying info.
- Brave Search: Independent index with built-in privacy.
How to switch:
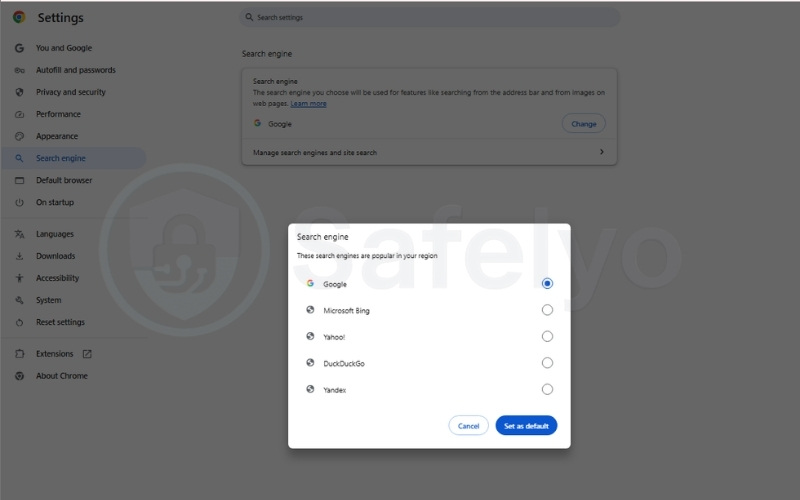
- Visit your browser’s settings.
- Look for the Search engine section.
- Set your default to DuckDuckGo or another private option.
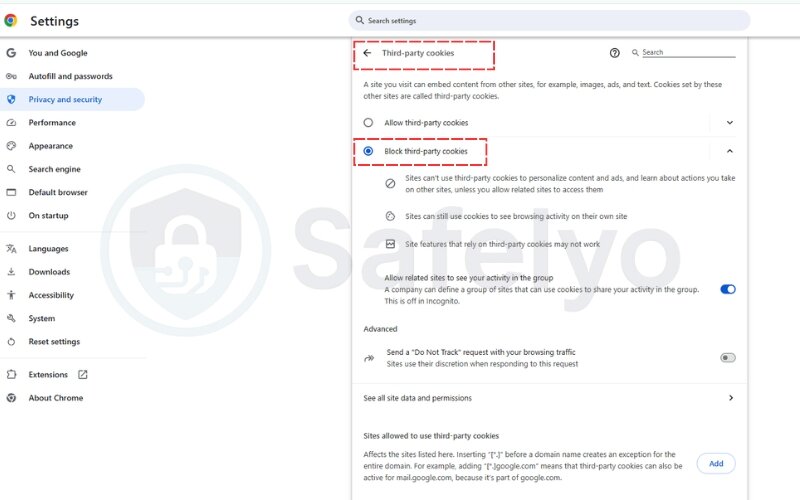
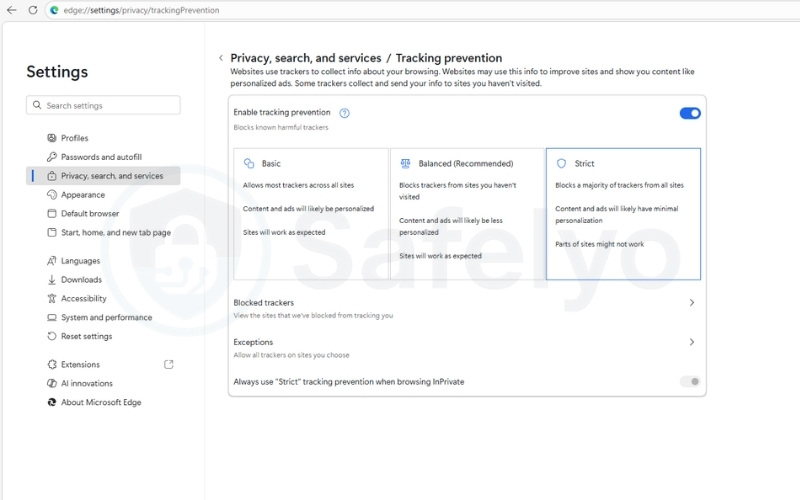
2.8. Reduce or disable third-party cookies in your browser
Third-party tracking cookies are one of the most common tools advertisers use. Blocking them can reduce cross-site tracking significantly.
How to reduce/disable third-party cookies on desktop (Chrome/Edge/Firefox):
- Chrome: Go to Settings → Privacy and security → Third-party cookies. Select Block third-party cookies.
- Edge: Go to Settings → Privacy, search, and services. Under Tracking prevention, select “Strict”.
- Firefox: Go to Settings → Privacy & Security. Under Enhanced Tracking Protection, select “Strict”.
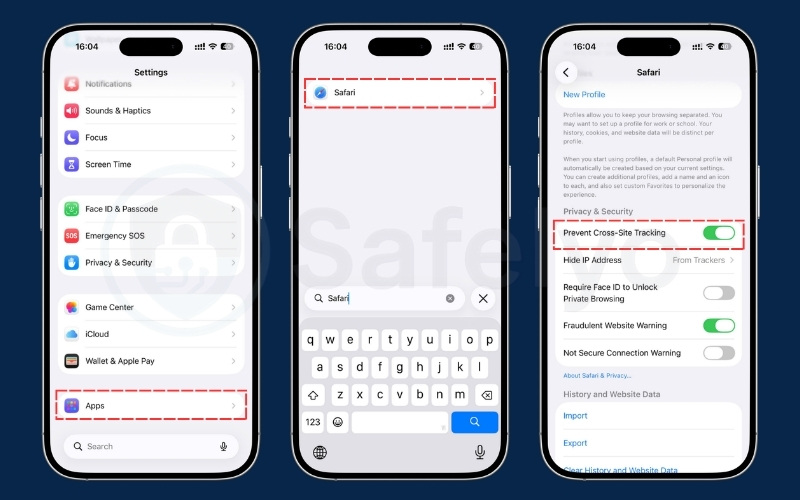
How to reduce third-party tracking on iOS/iPhone (Safari):
- Go to Settings → Apps → Safari (iOS 18 and later) or Settings → Safari (iOS 17 and earlier).
- Scroll down to Privacy & Security.
- Toggle on Prevent Cross-Site Tracking. This activates Safari’s Intelligent Tracking Prevention (ITP), which restricts third-party cookies used for cross-site tracking.
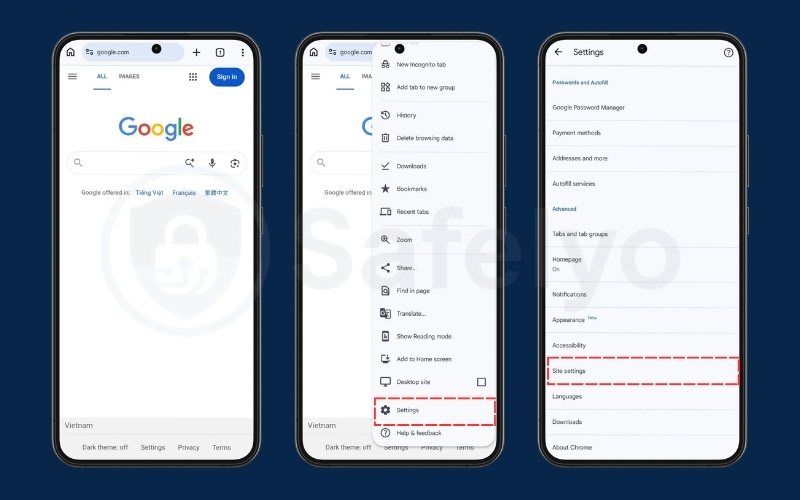
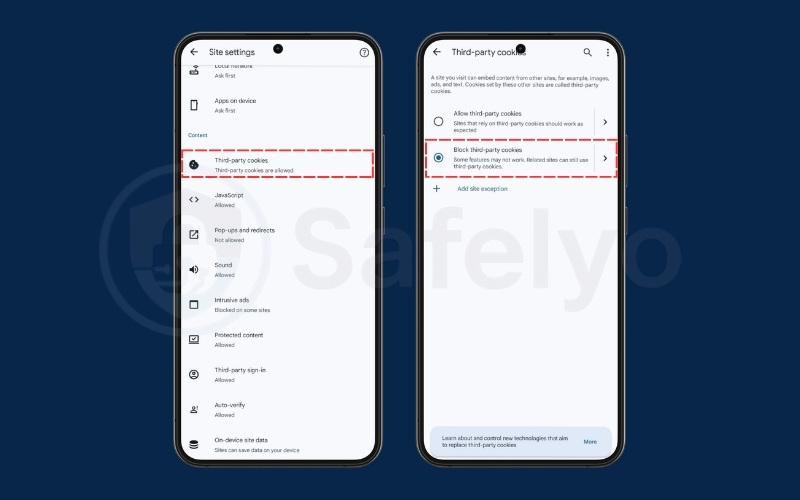
How to reduce/disable third-party cookies on Android (Chrome):
- Open Chrome, tap the three dots, and go to Settings → Site settings.
- Tap Third-party cookies and select Block third-party cookies.
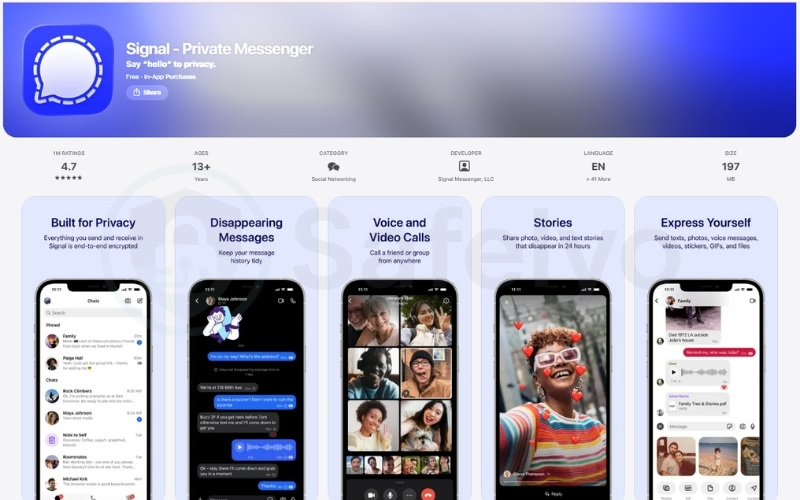
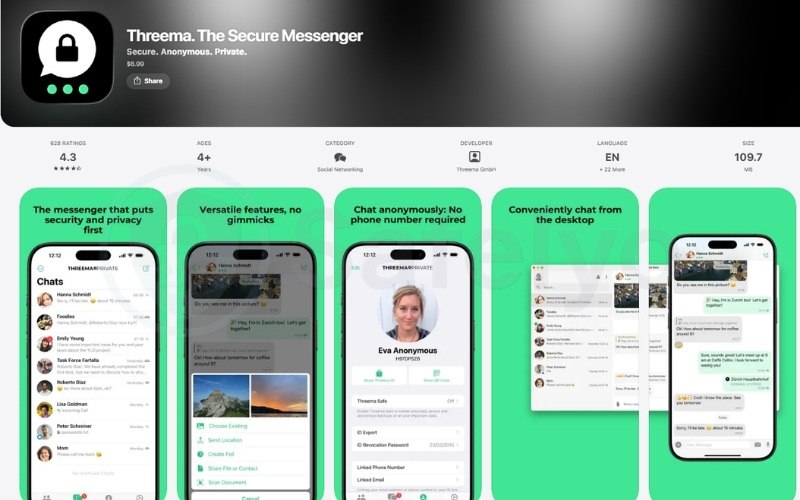
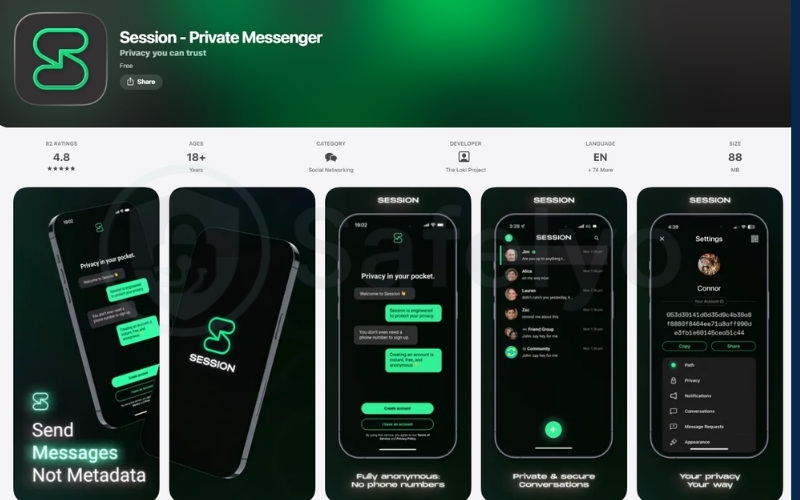
2.9. Use secure messaging apps
Some messaging apps track metadata or scan content for ad-targeting purposes. Choosing apps that only connect through secure websites is also important. Switching to secure, end-to-end encrypted apps protects your conversations from prying eyes.
Recommended apps:
- Signal: Open-source, no ads, and doesn’t collect metadata.
- Threema: Paid app with full anonymity.
- Session: Doesn’t require a phone number or a central server.
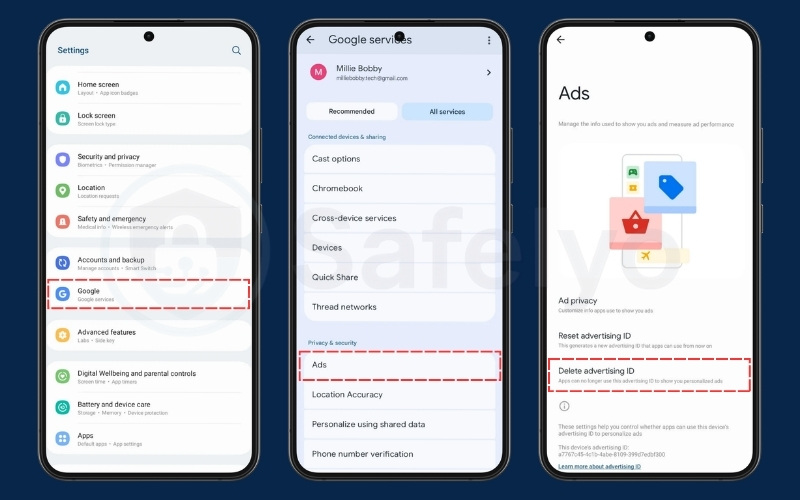
2.10. Turn off ad ID tracking on your device
Mobile devices assign you an advertising ID that helps marketers track your behavior across apps and services. Turning this off reduces cross-app profiling.
On Android:
- Settings → Google → All Services → Ads.
- Tap Delete advertising ID.
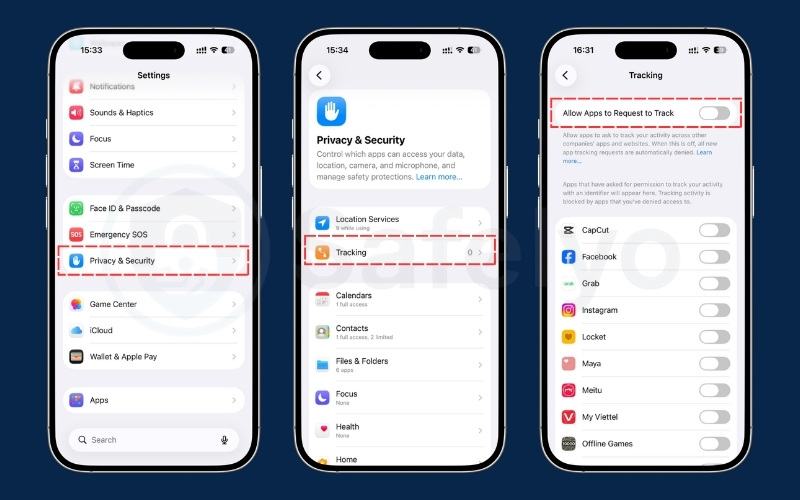
On iPhone:
- Go to Settings → Privacy & Security → Tracking.
- Turn off Allow Apps to Request to Track.
2.11. Disable default sync and history features
Syncing data across browsers and devices often enables passive tracking. Services like Google or Microsoft Edge sync history, passwords, tabs, and more by default.
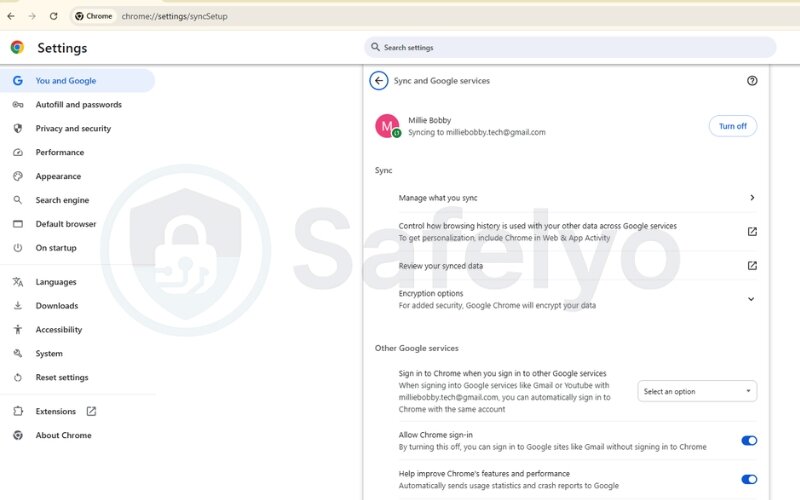
To disable syncing in Google Chrome:
- Go to Settings → You and Google.
- Click Sync and Google Services.
- Turn off all sync options or select only what you need.
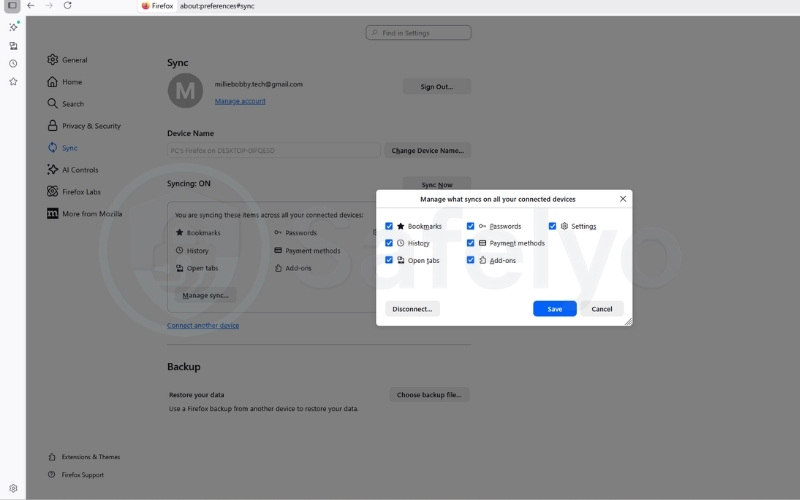
For Firefox:
- Go to Settings → Sync → Manage Sync….
- Uncheck options like history, bookmarks, and tabs.
2.12. Remove your data from data brokers
As mentioned earlier, data brokers harvest your information and sell it to the highest bidder. Blocking cookies won’t remove the data they already have. To truly reclaim your privacy, you must delete your profiles from their databases.
How to opt out:
- Manual removal: You can visit individual broker sites (like Acxiom, Experian, or Whitepages) and submit manual opt-out requests. This process is free but highly time-consuming.
- Automated tools: For a more efficient approach, use data removal services like Incogni, DeleteMe, or Aura. These tools automatically send and enforce deletion requests to dozens of data brokers on your behalf, ensuring your information is scrubbed and stays off the market.
2.13. Avoid Single Sign-On (SSO) options
You often see buttons like “Log in with Google” or “Continue with Facebook” when signing up for a new website. While convenient, this Single Sign-On (SSO) habit comes with a massive privacy cost.
Using these buttons grants the new website access to parts of your personal profile and tells Google or Facebook exactly which external services you are using. To keep your data compartmentalized, take the extra 30 seconds to create a standalone account using an email address and a unique password.
Since this means you will need to remember multiple logins, use a reliable password manager. A password manager will securely generate and store your unique passwords, giving you the convenience of a single click without the privacy risks associated with SSO.
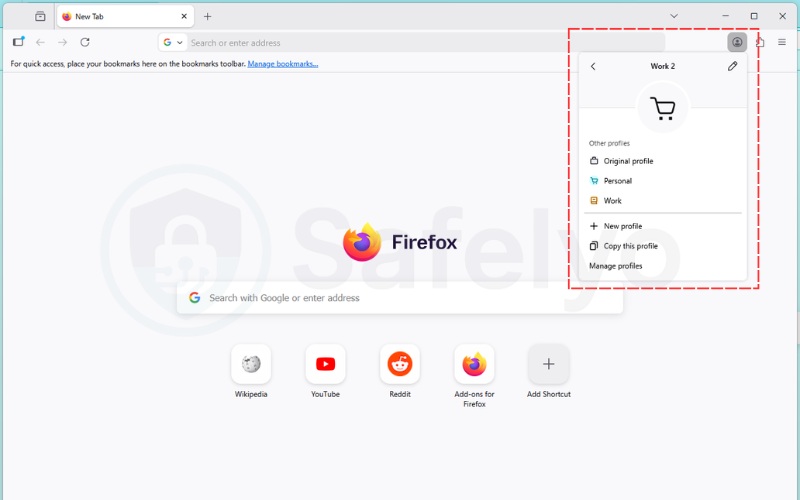
2.14. Isolate activities with multiple browser profiles
If you must use mainstream browsers like Chrome or Edge, you can limit data collection by creating separate user profiles for different tasks.
For example, use one profile strictly for work, another for personal banking, and a third for general web surfing or social media. This practice, known as compartmentalization, prevents tracking algorithms from combining your professional and personal data into one comprehensive profile.
2.15. Secure your smart home devices
Digital tracking extends far beyond your computer and smartphone. Smart home appliances consistently gather data about your daily routines and entertainment habits to personalize your experience.
To regain privacy in your living room, you need to adjust settings on two main types of devices:
- Smart TVs: Manufacturers often use a feature called Automatic Content Recognition (ACR) to log the programs you watch. To stop this, navigate to your TV’s main settings. Look for options labeled “Viewing Data,” “Smart Interactivity,” or “SyncPlus” (often hidden under “Terms and Policy” or “System” menus) and disable them completely.
- Voice Assistants: Devices like Amazon Echo or Google Home store audio recordings of your past commands. To secure them, regularly open their companion mobile apps (like the Alexa app) to review and delete your voice history. Additionally, press the physical mute button on the speaker itself to electronically disconnect the microphone when you are not actively using it.
2.16. Switch from mobile apps to web browsers
Mobile applications often request deep access to your device system, gathering far more personal data than a standard website ever could. They can easily pull your exact GPS coordinates, access your camera roll, or read your entire contact list.
To protect your digital privacy, consider uninstalling highly invasive apps and accessing those services through your mobile web browser instead. Browsers operate in a controlled environment, which naturally restricts how much information a company can extract from your phone.
2.17. Regularly clear your cache and cookies
If you use privacy-focused tools like anti-tracking browsers or incognito mode, your browser clears this data for you automatically. However, if you prefer sticking to standard browsers like Chrome or Edge, you must take manual action.
Whenever you visit a website, your browser saves snippets of data like images, fonts, and login tokens to make the page load faster the next time. Tracking companies use this local storage to hide persistent identifiers that follow your activity over time.
Making a habit of clearing your browser cache and cookies removes this stored data completely. This simple maintenance action directly disrupts ongoing tracking attempts and forces websites to treat you as a brand-new visitor.
3. Advanced tools & practices for digital privacy enthusiasts
If you’ve already applied the basics and want stronger protection, this section is for you. These advanced tools help reduce exposure to even the most persistent forms of online tracking. They’re designed for users serious about online privacy. While they may require some setup, the reward is much greater control over your digital identity.
3.1. Use encrypted operating systems (Tails, Qubes OS)
For maximum privacy, consider operating systems specifically designed to leave no trace and encrypt all activities.
- Tails is a live OS that runs from a USB stick and routes all traffic through the Tor network. It doesn’t store any data locally unless you choose to. Once you shut it down, your session is gone. It leaves no history, no residual files.
- Qubes OS takes another approach by isolating each app and activity into separate virtual machines (qubes). This “compartmentalization” prevents a single compromised app from exposing your entire system.
3.2. Rotate your IP with proxies or user-agent switchers
You can combine or use the following tools to enhance the management of your digital signals. Modern trackers often analyze patterns in hardware and software data to link your activities, even when your connection points change. These techniques are designed to either mask these signals or manage them for improved compartmentalization.
- Residential Proxies: Services such as Smartproxy or Bright Data provide access to IP addresses assigned to real home networks. By rotating through these pools, you can make it more difficult for trackers to associate activity history with a single network origin.
- Intelligent API Spoofing: Standard privacy tools that block all scripts can sometimes disrupt website functionality. Tools like CanvasBlocker & Trace (2026) attempt a more targeted approach by aiming to intervene only in specific APIs commonly used for fingerprinting (such as GPU rendering). This is intended to provide less distinctive data to trackers while keeping the sites you visit fully functional.
- Anti-detect Browsers: For tasks requiring significant isolation, dedicated browsers like Multilogin & GoLogin use engines designed to maintain consistent digital fingerprints for separate profiles. Instead of creating random noise that might appear suspicious to automated systems, these browsers aim to let you manage multiple personas that appear as distinct, “real” individuals within their respective sessions.
How to get started:
- Consider using residential proxy pools to vary your network presence across different regions.
- Explore rule-based spoofing extensions to manage how specific browser APIs report your data.
- Evaluate anti-detect browsers if your activities require maintaining separate, isolated digital identities for various online tasks.
Each technique can provide an additional layer of friction against tracking algorithms. By focusing on making your digital fingerprints less unique or better compartmentalized, you may achieve a more resilient level of online anonymity.
4. Understanding online tracking
If you’re looking for how to stop being tracked online, it helps to understand what online tracking actually is. Nearly every website or app you use collects data about your behavior, often without your knowledge.
These invisible systems are designed to monitor your activity, build digital profiles, and feed that information into advertising, analytics, or surveillance systems. Here’s how it all works and why it matters.
4.1. What is online tracking?
Online tracking is the process by which websites, apps, and third parties collect data about your behavior and user activity, often without your knowledge. This includes what you click, search, buy, or view. Over time, this data is used to build a digital profile of you.
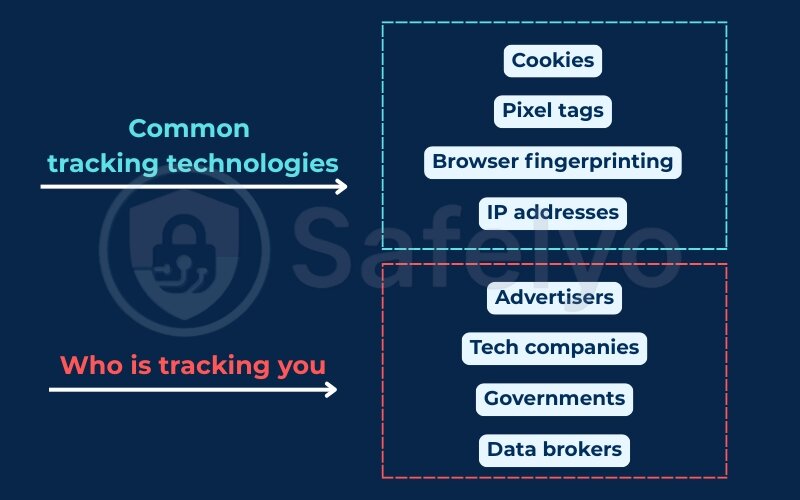
Common tracking technologies include:
- Tracking cookies that remember preferences or login sessions.
- Pixel tags that report your actions to a server.
- Browser fingerprinting that identifies you through system details to create a unique digital signature.
- IP addresses and device IDs that link your activity.
For example, you might visit a single shopping site, and within minutes, ads for that product will follow you across YouTube, Instagram, and even in email newsletters.
4.2. Who is tracking you and why?
Multiple players are involved in tracking you online:
- Advertisers use tracking data for marketing campaigns that feel highly personalized.
- Tech companies use data to improve products and increase engagement.
- Governments may track for national security or surveillance.
- Data brokers collect and sell your information to third parties.
Each of these actors has its own reasons, whether it’s profit, control, or insight.
4.3. What personal data is being collected?
The amount of personal data collected online is often underestimated. Much of this information is later used for targeted ads or data sharing with third parties. It can include:
- Your Internet Protocol address and geographic location.
- Device info, operating system, and browser type.
- Search history, visited websites, and clicked links.
- Purchase behavior, including payment methods.
- App usage, GPS data, and even biometric info.
If you download your data archive from major tech platforms, you will likely find years’ worth of location pings, search terms, audio logs, and ad preferences.
4.4. Is it really dangerous?
Yes, online tracking can go far beyond targeted ads. Risks include:
- Loss of control over your digital identity.
- Targeted scams and phishing based on your habits.
- Manipulation through political or behavioral profiling.
- Unwanted exposure of sensitive or private information.
Data collected from tracking can easily be used by cybercriminals to exploit your habits and push high-risk scams. For instance, you might receive a phishing email that perfectly mimics a real purchase you made the day before, using actual order info gathered through tracking tools.
Furthermore, seemingly anonymous browsing data can often be deanonymized. Data brokers piece together fragments of your online activity to create detailed profiles that eventually reveal your real identity and personal preferences. If any of these third-party applications or websites suffer a data breach, your personally identifiable information could easily be sold to cybercriminals on the dark web.
4.5. Know your legal privacy rights
Depending on where you live, you have specific legal rights regarding your personal data. Laws like the General Data Protection Regulation (GDPR) in Europe and the California Consumer Privacy Act (CCPA) in the US force companies to be transparent about what they collect.
These laws give you the right to ask websites exactly what data they have on you and request its immediate deletion. Furthermore, you can explicitly opt out of having your information sold to third parties. Understanding these rights allows you to demand accountability from the services you use.
5. How web and app tracking work
To protect your online privacy, it’s essential to first understand how tracking works on websites and mobile apps. From cookies to cross-device monitoring, these methods are built into nearly every platform and service you use. Understanding them is the first step in learning how to stop being tracked online.
5.1. Cookies, pixel tags, and browser fingerprinting
To understand how your data is collected, you need to know the specific tools websites use. These tracking methods range from basic text files to highly invasive, invisible codes:
- Cookies: Websites save these small text files on your device to remember your information and preferences.
- First-party cookies: The site you visit creates these to enhance your experience, such as keeping you logged in.
- Third-party cookies: External ad networks place these to follow your activity across different websites and build a behavioral profile.
- Session vs. Persistent cookies: Session cookies delete immediately when you close your browser, while persistent cookies stay on your device for months.
- Pixel tags (Web beacons): These tiny, invisible images hide in webpages or emails. They silently alert a server the exact moment you open a message or view a product.
- Session replay scripts: This code records your exact keystrokes, mouse coordinates, scrolling speed, and clicks to log exactly how you interact with a webpage.
- Browser fingerprinting: Trackers use this technique to collect your specific system settings, such as screen resolution and installed fonts. This creates a unique identifier to track you even if you clear your cookies. In 2026, artificial intelligence has elevated fingerprinting to an even more dangerous level. New scripts use machine learning to analyze hundreds of micro-signals simultaneously, such as how your GPU renders colors, JavaScript execution timing, and font sub-pixel rendering.
- The persistence of fingerprints: The resulting AI-driven fingerprints are highly stable, accurate, and can persist even if you switch browsers or use a VPN. This makes native browser protection (which we cover in section 2) more essential than ever before.
- Account tracking: Platforms like Google or Facebook monitor your cross-site activity when you stay logged in. This links your entire browsing history directly to your real identity.
Of all these tracking tools, third-party cookies and account tracking impact your daily experience the most, directly causing the highly targeted ads that follow you across the web. However, browser fingerprinting poses the most severe long-term privacy threat, as it allows companies to persistently identify you even after you have completely cleared your cookies and browsing history.
5.2. Tracking via apps and mobile devices
Mobile applications possess a unique advantage in data collection because they operate directly on your hardware, often with prolonged or continuous access. Unlike websites confined to a browser sandbox, apps can extract significantly more personal information:
- System Permissions: Apps routinely request deep access to your hardware, pulling your real-time GPS location, camera, microphone, local storage, and entire contact lists.
- Device Identifiers: Smartphones assign a unique identifier to your device, such as the Apple IDFA (Identifier for Advertisers) or Google Advertising ID (GAID). These mobile ad IDs serve as persistent device tags, allowing third-party trackers to monitor your behavior across completely different, unrelated applications.
- Background Telemetry: Even when an app is closed, background processes can periodically ping servers. They transmit telemetry data, network connection details, and even battery status.
Developers frequently integrate third-party Software Development Kits (SDKs) to monetize their free apps. This means your usage patterns, screen time, and location history are routinely packaged and transmitted to external advertising networks without requiring active user interaction.
5.3. Cross-site and multi-device tracking explained
To build a comprehensive digital profile, advertising networks must follow your activity outside of a single app or website. This continuous monitoring is achieved through two main strategies:
- Cross-site tracking: This occurs when a third-party entity monitors your browsing activity across multiple, unrelated domains. This is typically achieved through embedded resources like social media sharing buttons, analytics scripts, or hidden pixel tags. When you load a webpage, these scripts execute and read stored cookies, compiling a log of the sites you visit.
- Tracking across multiple devices: This takes monitoring a step further by linking your smartphone, tablet, and desktop computer to a single identity profile. This is accomplished using two primary methods:
- Deterministic tracking: Relies on concrete identifiers, such as logging into the same account (like an email provider or social media platform) on different devices.
- Probabilistic tracking: Uses algorithms to analyze data points like your IP address, Wi-Fi network, browsing habits, and device proximity. This allows networks to make highly accurate assumptions that multiple devices belong to the same user, effectively bridging the gap between your desktop searches and mobile application usage.
5.4. Data brokers and invisible tracking infrastructure
The online tracking ecosystem is heavily supported by data brokers, companies that specialize in aggregating, analyzing, and selling personal information. These organizations operate largely behind the scenes, fueling the invisible tracking infrastructure.
Here is how data brokers function:
- Data aggregation: They pull data from a vast array of sources to build exhaustive digital profiles. They harvest information from public records, retail loyalty programs, credit card transactions, and online tracking scripts.
- Profile segmentation: By combining offline purchasing behavior with online browsing habits, data brokers create detailed segments. They categorize consumers by income level, health interests, political affiliations, and purchasing intent.
- Monetization: Companies such as Acxiom, Experian, and Equifax manage databases containing thousands of data points on billions of individuals worldwide. This aggregated data is then sold or leased to advertisers, insurance companies, financial institutions, and political campaigns for highly targeted outreach.
Because data brokers operate as intermediaries, individuals rarely interact with them directly. This makes it extremely difficult to know exactly what information is being held, how it is being categorized, or who is ultimately purchasing access to it.
6. Signs you’re being tracked online
Even if online tracking is invisible, there are clear signs that your online privacy is being monitored. Recognizing these clues can help you take proactive steps to reduce exposure. From oddly personalized ads to apps demanding too much access, these common indicators show that your digital activity is being watched.
6.1. Personalized ads after visiting websites
One of the most obvious signs of being tracked is when ads start mirroring your recent browsing behavior. This is known as ad retargeting, a direct result of trackers embedding cookies or pixels on websites to follow your activity.
Watch for these specific behaviors:
- Instant retargeting: You visit an online store just once, and suddenly ads for that exact product appear on news sites or YouTube.
- Cross-platform persistence: You search for an item on your laptop, and the ad shows up on your mobile social media feeds.
- Highly specific recommendations: The ads are not just for a general category (e.g., shoes), but for the exact brand and model you were looking at minutes ago.
If you’re wondering how to stop being tracked online, identifying this aggressive ad behavior is your first indicator that cross-site tracking is active.
6.2. Apps requesting excessive permissions
Many mobile apps ask for permissions that go far beyond what they need to function. Granting unnecessary permissions allows apps to collect data in the background, which can then be sold or shared with third-party advertisers.
Be suspicious if you encounter:
- Utility apps wanting location: A simple flashlight or calculator app requesting access to your real-time GPS data.
- Offline games accessing contacts: A single-player puzzle game demanding access to your phone book and call logs.
- Always-on microphone access: Apps asking to use your microphone even when you are not actively using voice features.
Reviewing app permissions is a critical step in minimizing the background data collection that feeds tracking algorithms.
6.3. Search engine suggestions tied to past activity
Search engines often use your previous queries and browsing history to offer personalized suggestions in the autocomplete bar. While this feature can feel convenient, it clearly demonstrates that your data is being stored and analyzed.
You can observe this by checking:
- Hyper-local autocomplete: The search engine suggests very specific, local businesses before you even type a location.
- Predicting recent interests: Autocomplete heavily favors topics you were researching days or weeks ago, even if they aren’t trending broadly.
- The “Incognito” contrast: When you switch to a private window or a different device not logged into your account, the search suggestions are drastically different and more generic.
This personalization contributes to a unique digital fingerprint of your habits, which privacy-focused search engines actively try to avoid.
Read more:
7. FAQs on how to stop being tracked online
Does a VPN stop all tracking?
No. A VPN hides your IP address and encrypts your internet traffic, but it doesn’t block tracking cookies, fingerprinting, or trackers embedded in websites. For complete protection, combine a VPN with tracker blockers and privacy-focused browsers.
Can I be tracked in incognito mode?
Yes. Incognito mode only prevents your device from saving browsing history, cookies, or form data locally. Websites, search engines, and ISPs can still track your activity in real time. Even if you enable Do Not Track, many advertisers still ignore it.
Is Google tracking me even when I’m not signed in?
Yes. Google uses cookies, device identifiers, and IP addresses to track users, even if you’re logged out. To reduce tracking, consider disabling ad personalization in your Google account settings and using a privacy-respecting search engine. Using secure websites (HyperText Transfer Protocol Secure) reduces risks of interception.
Do iPhone and Android devices track me by default?
Yes. Both platforms collect location, app usage, and system activity data by default. You can limit this by adjusting privacy settings, turning off location services, and restricting app permissions. Checking your privacy settings regularly ensures you stay in control.
What’s the most effective way to stop being tracked online?
There’s no single solution. The best approach is layered:
- Use a Virtual Private Network
- Switch to a privacy-first browser
- Block trackers
- Limit app permissions
- Review your digital footprint regularly
These combined steps make it significantly harder for companies and trackers to invade your online privacy. For complete protection, combine a Virtual Private Network with tracking blockers and privacy-focused browsers.
Does the “Do Not Track” setting actually work?
No. You might have seen a “Do Not Track” (DNT) toggle in your browser settings, but do not rely on it. It is merely a psychological solution. Because the DNT signal lacks legal binding, major websites and ad networks completely ignore it. Instead of politely asking sites not to track you, use a real tracker blocker like uBlock Origin to forcibly stop them.
8. Conclusion
By protecting your data, you also protect your online reputation, which can be just as valuable as your identity. Knowing how to stop being tracked online is essential for protecting your personal data, digital identity, and everyday online privacy. In today’s connected world, online tracking is built into many websites, apps, and services, but that doesn’t mean you have to accept it.
By using tools like anti-tracking browsers, VPNs, and tracker blockers, and by adjusting your device and app settings, you can take back control of your personal data and digital footprint. For those who want deeper protection, advanced methods like encrypted operating systems and proxy tools offer additional layers of security.
Want to go further? Explore more guides on digital safety and tech know-how in the Tech How-To Simplified section at Safelyo to ensure your continued protection.