What is a no-logs policy? A no-logs policy means a VPN provider does not collect, store, or share your browsing activity, IP address, or connection logs. By routing your internet traffic through their servers, they blind your ISP – but remember, not all privacy claims are equal, and you must verify their technical proof.
If you are looking for the truth behind VPN privacy claims, here are the fast answers you need:
- What does “no-logs” actually mean?
→ It guarantees zero retention of activity data (browsing history) and identifiable metadata (IP addresses/timestamps). - Does “no-logs” mean zero data existence?
→ No. VPNs still process traffic in real-time and store basic billing information. - How can you verify a claim?
→ Ignore the marketing. Look for RAM-only servers and recent independent audits (e.g., PwC, Deloitte). - Do free VPNs have no-logs policies?
→ Rarely. Most free services actively log and sell your data to cover their costs. - Can police request data from a no-logs VPN?
→ Yes, but a genuine provider will have empty servers and nothing to hand over.
In the VPN industry, marketing promises and technical reality are often two completely different things. Just because a company promises not to track your data does not mean they actually have the infrastructure or the legal backing to pull it off. In fact, some “no-logs” free VPNs have been caught red-handed selling user data to third-party advertisers.
So, what is a no-logs policy, exactly? And more importantly, how do you separate the empty marketing buzzwords from genuine privacy protection? In this guide, I will break down everything you need to know.
We are going to explore the critical difference between connection logs and activity logs. We will look at the actual server technology that makes zero-logging possible. Additionally, we will provide a clear framework to verify if your VPN provider is truly keeping your secrets safe. Let’s dive in.
1. What is a no-logs policy?
At its core, a no-logs policy is a strict operational commitment from a VPN provider. When you connect to their network, they pledge to act like a completely blind middleman. They actively refuse to monitor, record, or store any information about what you do online. This means your search history, the files you download, and the websites you visit remain entirely invisible to them.
To make this easier to understand, let me share my favorite way to explain this to beginners: The hotel analogy. Imagine your Internet Service Provider (ISP) as a standard hotel. They keep a highly detailed guestbook. They know your name, exactly when you checked in, who you brought to your room, what you ordered for room service, and when you left.
A true no-logs VPN, on the other hand, operates like a secret, self-service motel. It has no guestbook, no security cameras in the hallways, and no receptionist. You walk in, do your business, and leave. If the authorities show up the next day demanding to know who stayed in room 302, the manager literally has no information to hand over. They cannot give away what they never collected in the first place.
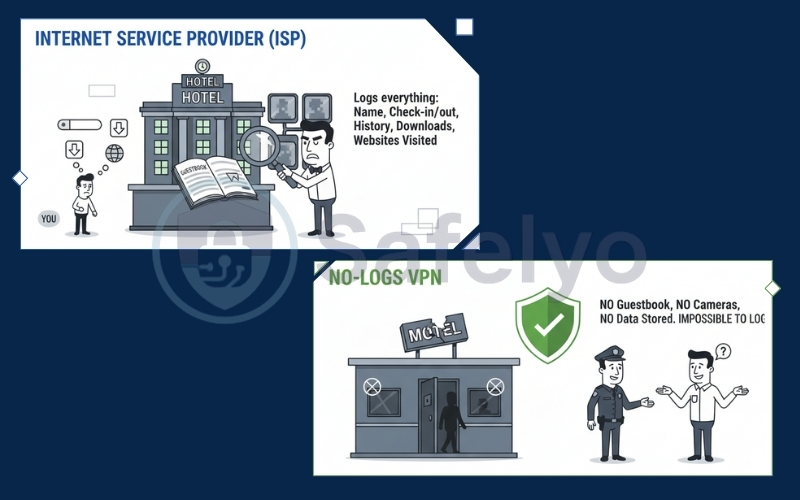
However, to fully grasp what a no-logs policy means in the tech world, we have to look under the hood. When a provider claims “no logs”, they usually mean “no activity logs”. But in reality, running a global server network requires handling different types of data. Here is how I break them down:
- Activity logs (The absolute no-go): This is the actual content of your internet traffic. It includes your search queries, visited URLs, downloaded files, and DNS (Domain Name System) requests. A genuine no-logs policy means these are never collected. Period.
- Connection logs (The gray area): This refers to the metadata about your VPN session. It might include your original IP address, the IP address of the VPN server you connected to, connection timestamps, and the total bandwidth used. While keeping basic bandwidth data for server maintenance is sometimes acceptable, a premium no-logs VPN will never store your real IP address or exact session times.
- Account data (The necessary evil): To run a premium subscription service, a VPN company needs basic information, such as your email address and payment details. Storing this does not violate a no-logs policy, because this information cannot link your identity back to your specific web browsing history. Besides, privacy purists can always bypass this by using a disposable email and paying with cryptocurrency.
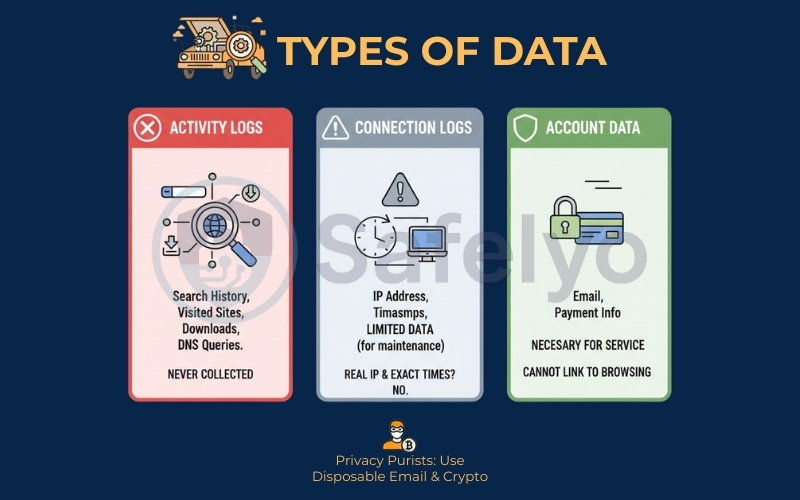
To make things clear, here is a quick visual breakdown of what a true no-logs provider will and will not keep:
| Type of data | What it includes | Kept by a true no-logs VPN? |
| Activity logs | Search history, visited URLs, downloaded files, DNS queries | Absolutely never |
| Connection logs | Real IP address, exact connection timestamps, session duration | No (Only anonymous, aggregated bandwidth data is acceptable) |
| Account data | Email address, payment details, subscription status | Yes (Required for the service, but totally unlinked from your traffic) |
2. Why is a no-logs policy important?
If you find yourself wondering, “Do I really need a no-logs VPN?”, the answer is an absolute yes.
I always tell people: Using a VPN without a strict no-logs policy is like putting a heavy-duty lock on your front door, but leaving the key right under the welcome mat. It creates an illusion of security, but leaves you completely exposed when it matters most.
When a provider actively tracks your digital footprint, it defeats the entire purpose of paying for a privacy tool. Here are the three major risks you face when your VPN decides to keep records of your online life:
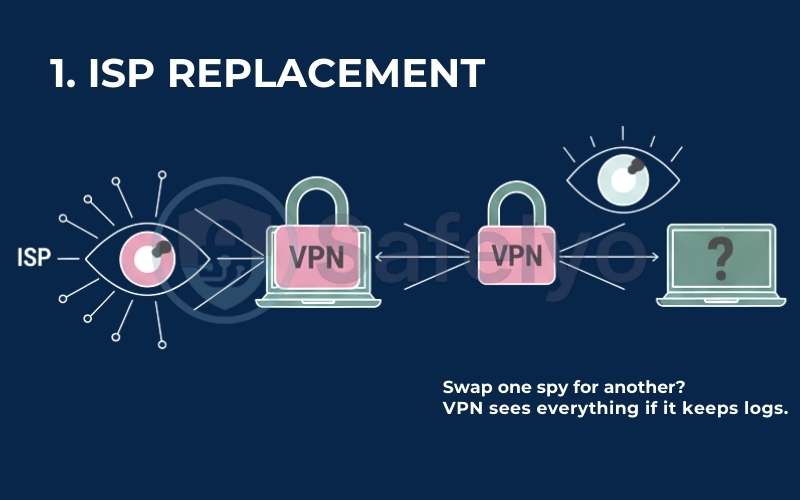
The ISP replacement problem
Normally, your ISP can see everything you do online. When you connect to a VPN, you successfully blind your ISP – but you hand that exact same power directly to the VPN company. If that provider keeps logs, you haven’t actually improved your privacy; you have simply swapped one corporate spy for another.
Data breach risks
No technology company is immune to hackers. If a VPN stores vast amounts of user data, its servers become a massive honeypot for cybercriminals. In the event of a successful cyberattack, your private search history, real IP address, and downloaded files could end up for sale on the dark web. A true no-logs VPN eliminates this threat through sheer logic: Hackers cannot steal what does not exist.
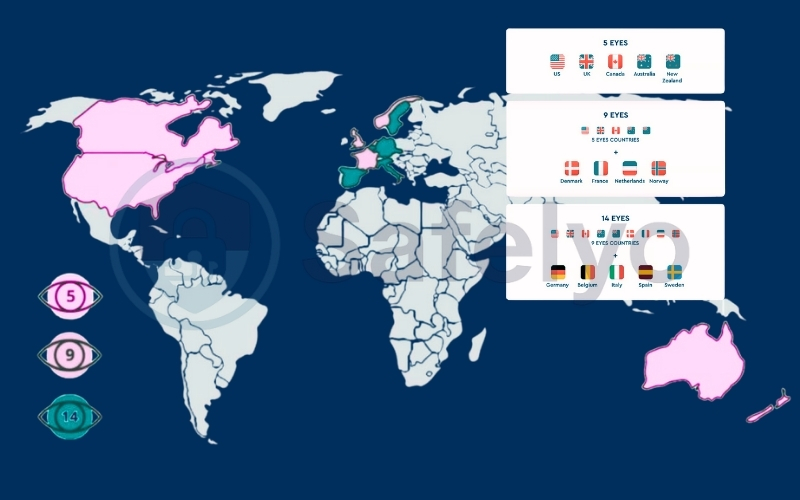
Government requests and global surveillance
Governments and law enforcement agencies frequently serve tech companies with legal warrants, demanding access to user data. This is especially dangerous if the VPN operates in countries belonging to the Five Eyes, Nine Eyes, or Fourteen Eyes intelligence-sharing alliances. These nations actively monitor internet traffic and share surveillance data across borders.
If your VPN keeps logs, they can be legally forced to hand your data over. A strict no-logs policy acts as the ultimate legal shield – they can comply with the subpoena, but they will have blank hard drives to show for it.
Ultimately, a no-logs policy is important because it transforms blind trust into mathematical certainty. Instead of hoping a company will not misuse your data, a verified no-logs architecture ensures they physically cannot.

3. What exactly does a strict no-logs policy cover?
Many users mistakenly believe that “no-logs” means a VPN company deletes absolutely everything, including your email address and subscription renewal date. This is incorrect.
To give you a legal-grade definition: A strict no-logs policy refers specifically to the complete absence of activity data and identifiable connection metadata. It guarantees that the provider cannot match a specific user to a specific online action, even under legal pressure.
To clarify the confusion, we must break down logging into three distinct levels of risk. A true no-logs VPN protects you against Level 1 and Level 2, while Level 3 is generally necessary for the service to function.
Level 1: Activity logs (The “Never” zone)
This is the content of your internet traffic. A strict policy guarantees that the following are never recorded:
- Browsing history: The specific websites you visit.
- DNS queries: The domain names you type into your browser.
- Files downloaded: The actual data packets you retrieve.
- Search queries: What you type into Google or Bing.
Risk level: Critical.
If a VPN logs this, they are not a privacy tool; they are a surveillance tool.

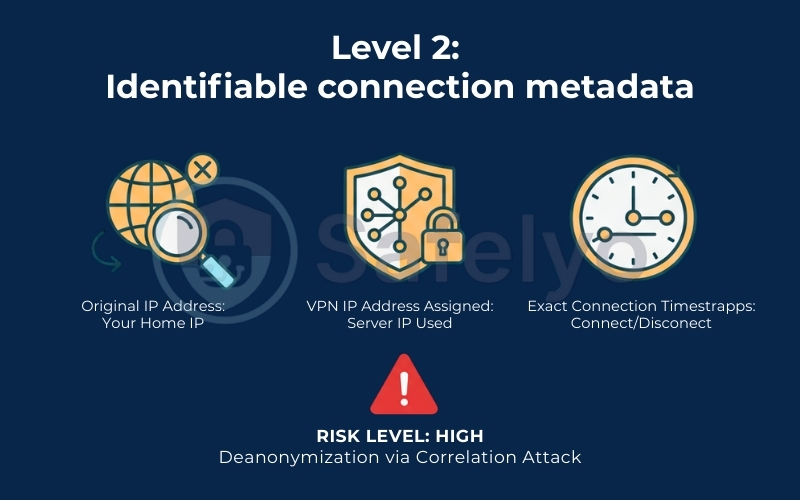
Level 2: Identifiable connection metadata (The “Hidden Danger”)
This is where most “fake” no-logs VPNs get caught. They might not record what you visited (Level 1), but they record how you connected. This often includes:
- Original IP address: Your real home IP.
- VPN IP address assigned: The specific server IP you used.
- Exact connection timestamps: The precise second you connected and disconnected.
Risk level: High (Deanonymization via Correlation Attack).
Here is why this is dangerous: If authorities have your original IP (from your ISP) and the VPN’s IP (from a website server log), they can use timestamps to link the two. By cross-referencing Time A at the ISP with Time A at the VPN, they can mathematically prove that User X was the person who visited Website Y. A strict no-logs policy must actively discard these identifiable timestamps.
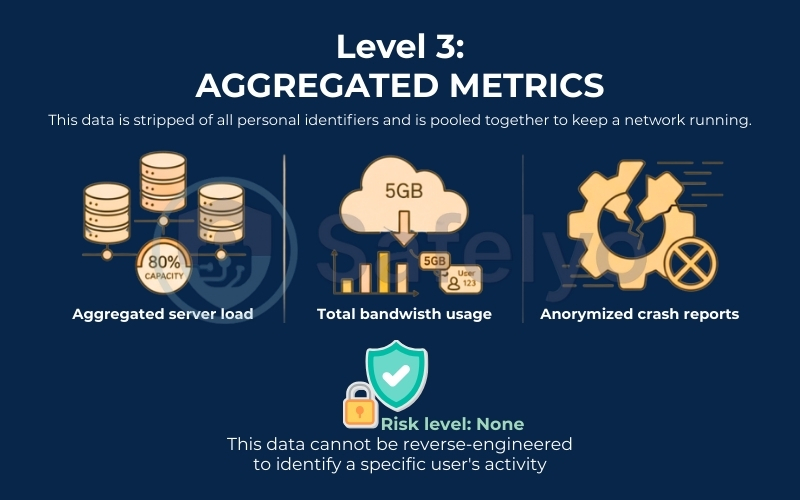
Level 3: Aggregated metrics (The “Safe” zone)
This data is stripped of all personal identifiers and pooled together to keep the network running.
- Aggregated server load: Knowing a server is at 80% capacity (without knowing who is filling it).
- Total bandwidth usage: Tracking that “User Account 123” used 5GB of data (without knowing what files made up that 5GB).
- Anonymized crash reports: Technical error codes to fix bugs.
Risk level: None.
This data cannot be reverse-engineered to identify a specific user’s activity.
What is guaranteed vs. What is ossible?
To verify if a provider meets the “strict” standard, use this breakdown:
| Data type | Strict no-logs policy guarantee | Can they still see it in real-time? |
| Browsing History & DNS | Absolutely No (Never stored) | Yes (Only in RAM for milliseconds to route traffic) |
| Original IP Address | Absolutely No (Never stored) | Yes (Needed to establish the tunnel, then discarded) |
| Identifiable Timestamps | Absolutely No (Never stored) | Yes (Active session only, wiped on disconnect) |
| Aggregated Bandwidth | May Collect (For account limits) | N/A (Pooled data) |
| Account Email/Payment | May Collect (For subscription) | N/A (Stored in separate billing system) |
The bottom line: A strict no-logs policy does not mean “zero data existence”. It means zero identifiable data retention. The provider may know you are a customer (via billing), but they effectively have “amnesia” regarding what you did with their service.
4. No-logs vs zero-logs: Is there a difference?
When you browse different VPN websites, you will inevitably see flashy phrases like “100% zero-logs”, “strict no-logs”, or “absolute zero-logging”. As a consumer, it is completely natural to wonder if a zero logs VPN somehow offers better, more advanced protection than a standard no-logs provider.
Let me save you some time: There is absolutely no technical or legal difference between these terms. In the cybersecurity industry, the debate of zero logs vs no logs is entirely a battle of marketing wording. Companies choose to use the word “zero” simply because it sounds more absolute, definitive, and secure to the average buyer.
So, what is the actual strict no logs meaning? Again, this is just another layer of marketing emphasis. A VPN provider cannot be “partially” no-logs when it comes to your private browsing history. They either record your internet traffic, or they do not. Adding the word “strict” does not legally bind a company to a higher standard of privacy laws or data protection.
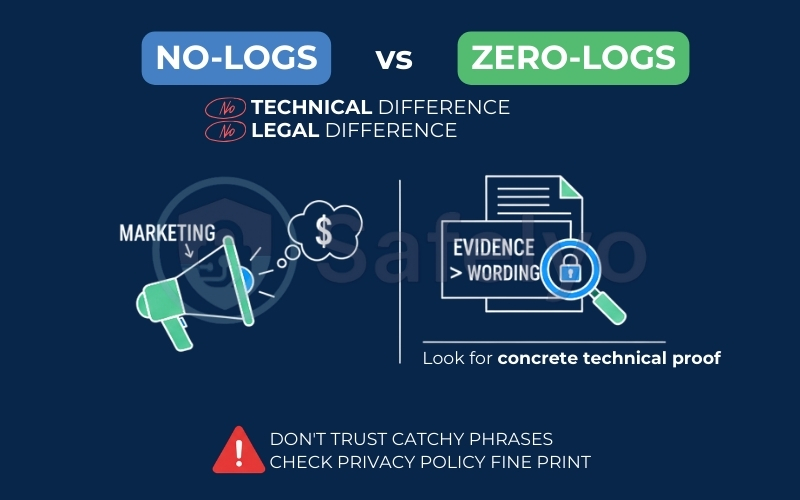
Ultimately, you should never base your buying decision on which catchy phrase a company slaps on its homepage. A massive “100% zero-logs” badge means absolutely nothing if the provider secretly stores your original IP address in the fine print of their privacy policy.
When evaluating a VPN’s trustworthiness, I always advise my readers to follow one golden rule: Evidence is greater than wording. Instead of focusing on clever marketing slogans, you need to look for concrete technical proof to verify their claims.
5. How do no-logs VPNs technically avoid logging?
As a cybersecurity reviewer, I always look past a company’s privacy policy and straight at its server architecture. Why? Because anyone can type a promise on a website, but hardware does not lie.
The industry’s gold standard for a proven no-logs policy relies on advanced infrastructure that physically prevents long-term data storage. Here are the technical mechanisms top-tier providers use to ensure they cannot log your data, even if they wanted to:
- RAM-only servers (Diskless infrastructure): This is the biggest breakthrough in modern VPN security. Traditional servers use standard hard drives, which write and store data permanently until someone manually erases it. If authorities seize a hard drive, they can easily extract its contents. RAM-only servers, however, use volatile memory. RAM requires continuous electrical power to store information.
- Automatic wipe on reboot: Because these diskless servers run entirely on RAM, the operating system and any temporary session data exist only in the active memory. The moment someone powers down, unplugs, or restarts the server, an automatic wipe on reboot occurs. If a government agency physically rips the server out of the data center, it instantly turns into a blank, useless piece of metal before it ever reaches a forensics lab.
- Strict log rotation policies: For the minimal, anonymous diagnostic data that providers do need to collect (like overall server load), they implement aggressive log rotation. The software automatically overwrites this temporary data every few minutes, ensuring no historical records ever accumulate.
- Internal access control: A true no-logs VPN protects you from its own staff. Premium providers enforce strict internal access controls. This means even their own system administrators and engineers cannot log into the live server environment without multiple layers of cryptographic keys. They also require zero-trust verification for access.
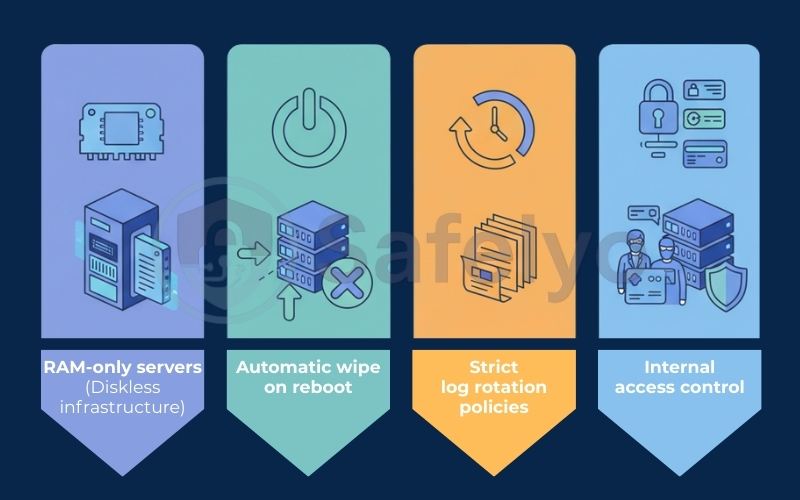
Several industry leaders have built their reputations on this exact technology. For instance, ExpressVPN pioneered this concept with its proprietary TrustedServer tech. Shortly after, giants like NordVPN and Surfshark upgraded their entire global networks to fully diskless infrastructure.
When a VPN runs on RAM, it transforms a legal promise into a mathematical and physical certainty. They literally lack the hard drives required to save your browsing history.
6. Does VPN jurisdiction affect no-logs policies?
In my years of reviewing privacy tools, one of the most common questions I get is whether the physical location of a VPN company actually matters. Does jurisdiction matter for a VPN? The short answer is absolutely yes.
A VPN’s legal jurisdiction is simply the country where the corporate entity is headquartered. This location determines which national privacy laws, court orders, and government regulations the company must comply with. If authorities serve a legally binding warrant, the VPN provider has no choice but to comply with that country’s laws.
To understand why this is a massive deal for your privacy, we have to look at how different countries handle digital surveillance:
- Data retention laws: Some countries force telecommunications and tech companies to store user data for a specific period (often 6 to 24 months). If a VPN operates in one of these countries, it cannot offer a true no-logs policy, no matter what its marketing department claims.
- The intelligence alliances: Countries within the 5/9/14 Eyes alliances (like the US, UK, Canada, and Australia) actively share surveillance data with one another. Furthermore, agencies in these countries can issue secret subpoenas or “gag orders”, forcing a company to hand over data while legally forbidding them from telling their users about it.
- Privacy-friendly havens: On the opposite end of the spectrum, countries like Panama, Switzerland, or the British Virgin Islands have no mandatory data retention laws. The governments in these jurisdictions do not compel companies to record internet traffic, making them the best VPN countries for privacy.

However, I need to clarify a very important nuance: Jurisdiction does not mean automatic logging.
If a highly secure, RAM-only VPN operates in the United States, it does not mean they are secretly recording your every move. If a US court orders them to hand over a user’s browsing history, a true no-logs VPN will still have zero data to give. You cannot hand over what you never stored.
But operating in a high-surveillance country significantly increases the pressure risk. A hostile government could theoretically raid the data center, seize the servers, or attempt to force the VPN company to start logging traffic going forward. This is why pairing a proven no-logs policy with a safe, offshore jurisdiction is the ultimate gold standard for digital anonymity.
>> You may also be interested in: 5 best VPN for privacy in 2026 (Audited no-logs VPNs only)
7. Can you trust a no-logs VPN?
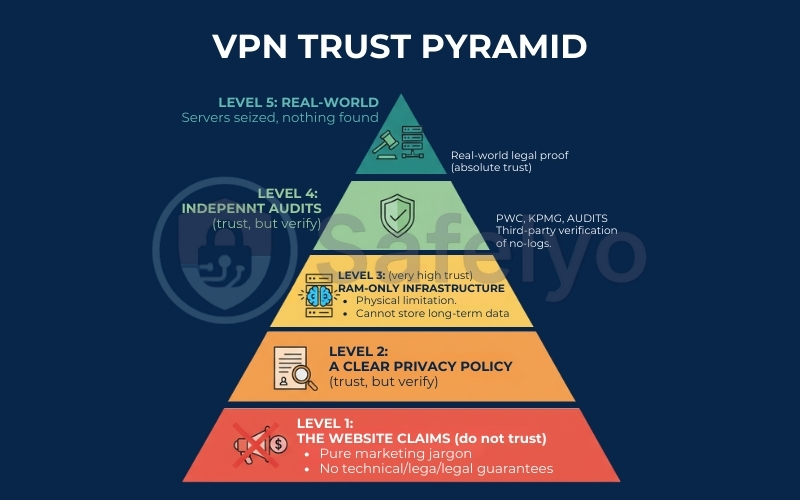
Over the years, I have tested hundreds of privacy tools, and I quickly realized that taking a VPN company at their word is a terrible security strategy. Trust in the cybersecurity world should never be given freely; it must be earned and mathematically proven.
To help my readers separate marketing fiction from technical reality, I developed what I call the VPN Trust Pyramid. When evaluating whether an audited no-logs policy is legitimate, I run the provider through these five distinct levels of verification, starting from the bottom up.
Level 1: The website claims (Do not trust)
Every single VPN provider slaps a bold “100% strict zero-logs” badge right on their homepage. As a consumer, you should treat this with zero absolute trust. This is the lowest tier of evidence. It is purely marketing jargon designed to get you to click the “Buy” button, and it offers absolutely no technical or legal guarantees.
Level 2: A clear privacy policy (Trust, but verify)
Moving up the pyramid, we look at the actual legal document. A detailed, transparent VPN privacy policy legally binds the company to its claims. It should clearly outline exactly what data they process and what they ignore.
However, while a strong policy is a great starting point, it is still just a piece of paper. You must blindly trust that the company is actually following its own rules behind closed doors.
Level 3: RAM-only infrastructure (High trust)
This is where trust becomes technical rather than theoretical. As we discussed earlier, if a VPN runs its entire network on diskless, RAM-only servers, it physically cannot store long-term data. Hardware limitations provide a massive leap in trustworthiness. Even if a rogue employee wanted to log your data, the server architecture physically prevents them from doing so.
Level 4: Independent audits (Very high trust)
You should never just take a VPN’s word for it; you need third-party verification. The gold standard in the industry is an independent security audit.
Top-tier providers voluntarily hire highly respected global firms like PricewaterhouseCoopers (PwC), KPMG, or Cure53 to aggressively inspect their server configurations, source code, and internal access controls. If an auditor publicly verifies that zero logging occurs, you can confidently trust the service.
Level 5: Real-world legal proof (Absolute trust)
At the very top of the trust pyramid sits undeniable, real-world evidence. The ultimate test of a no-logs policy happens when law enforcement physically seizes a VPN server or issues a binding court order demanding a specific user’s browsing history. If the provider goes to court and literally has empty servers to show the judge, their policy is officially battle-tested.
8. What happens if authorities request user data?
Let’s play out a hypothetical scenario that readers constantly ask me about: What actually happens behind closed doors when a government agency hands a VPN provider a legally binding warrant for your data?
It is a scary thought, especially if you live in a region with heavy digital surveillance. However, a VPN company cannot simply ignore a judge’s order without facing severe legal consequences. They must respond. The outcome for your privacy entirely depends on the provider’s actual logging practices.
Here are the two ways this situation typically plays out:
Scenario A: The true no-logs VPN
When authorities serve a warrant to a verified, strict no-logs provider, the company’s legal team accepts the request. However, because they route traffic through RAM-only servers and refuse to track activity, they physically possess zero user data. They do not break the law by ignoring the subpoena; they comply by legally stating, “We have absolutely no information to give you”. Your identity remains 100% secure.
Scenario B: The partial-logs VPN
Now, imagine that same warrant hits a provider that secretly keeps connection logs. Even if they do not record the exact websites you visited, they still hold your original IP address and your exact login timestamps. When legally pressured, the VPN hands over this metadata. Law enforcement will then take those timestamps, cross-reference them with your local ISP, and easily expose your real identity.
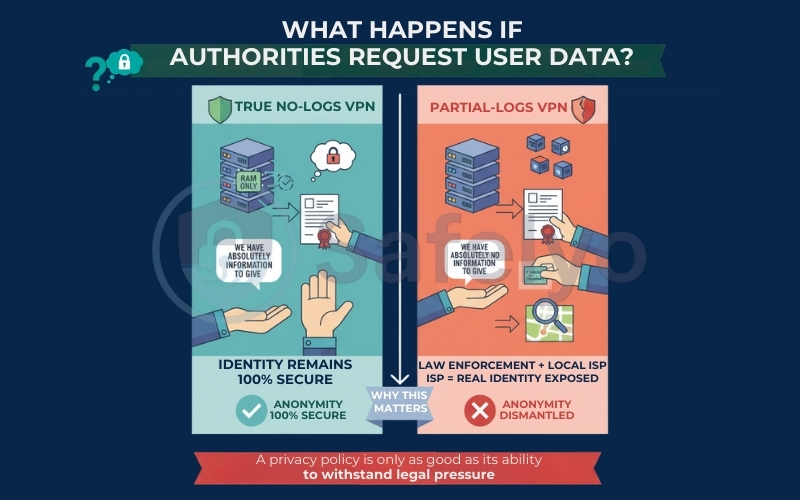
This stark contrast is exactly why I constantly warn people about fake marketing promises. A privacy policy is only as good as its ability to withstand legal pressure. If a VPN stores even a fraction of your connection data, a single government request can completely dismantle your anonymity in a matter of minutes.
9. Real-world examples of proven no-logs VPNs
Anyone can pay a fancy PR firm to write a flawless privacy policy, and while third-party audits are fantastic, they are still scheduled events. In my opinion, the absolute ultimate test of a no-logs policy happens when a VPN provider faces an unexpected, highly aggressive real-world threat.
When armed law enforcement agents physically raid a data center and unplug a server, marketing buzzwords stop mattering. Hardware takes over. Here are two of the most famous real-world cases where a sudden government investigation accidentally proved a VPN’s zero-logging claims to the world.
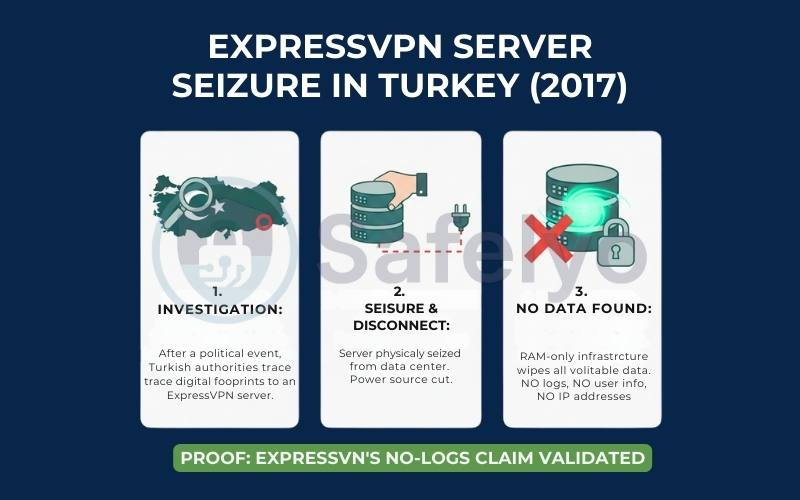
9.1. The ExpressVPN server seizure in Turkey (2017)
One of the most high-profile stress tests in VPN history happened in Turkey. Following a tragic, high-profile political assassination, Turkish investigators tracked the suspect’s digital footprint back to an ExpressVPN server. Seeking the user’s connection logs, authorities physically seized the server from the data center to extract the hard drives.
However, they quickly ran into a massive roadblock. Because ExpressVPN utilized RAM-only infrastructure, the moment the authorities disconnected the server from its power source, the volatile memory instantly wiped itself clean. The investigators found absolutely no useful user data, no activity logs, and no IP addresses. This surprise government raid unintentionally provided the strongest possible real-world proof that ExpressVPN’s no-logs claims were 100% legitimate.
>> Read more details in the ExpressVPN review (2026): Fast, secure, but worth the price?
9.2. The OVPN court battle in Sweden (2020)
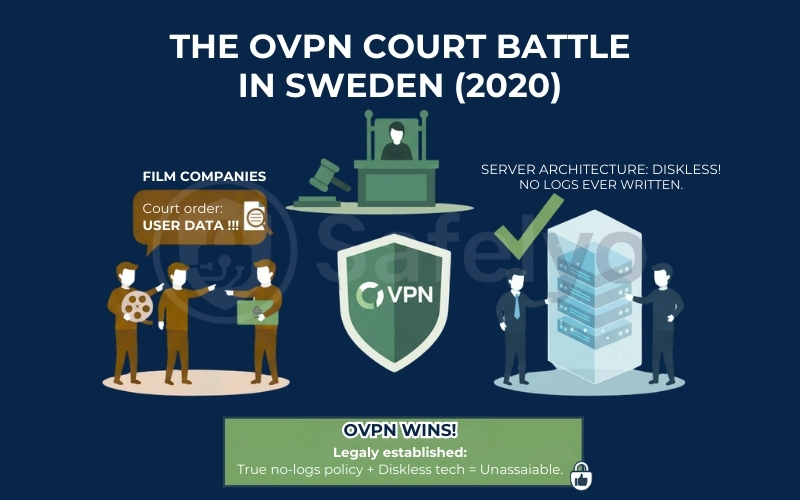
Another fascinating example of legal resilience comes from the Swedish provider OVPN. In 2020, an alliance of film companies suspected an OVPN user of copyright infringement. They obtained a court order demanding that OVPN hand over the user’s identity, connection timestamps, and downloaded files linked to a specific IP address.
Instead of quietly settling, OVPN took the matter to court. They legally demonstrated their entire server architecture to the judge, proving that their infrastructure ran entirely without physical hard drives. Their lawyers successfully argued that it was physically and mathematically impossible to extract logs that were never written in the first place. OVPN won the case, legally establishing that a true audited no-logs policy backed by diskless tech can withstand direct court injunctions.
These unexpected incidents highlight exactly why I emphasize technical evidence over empty promises. When the pressure is on, a genuine no-logs VPN will have absolutely nothing to hide – and more importantly, nothing to hand over.
10. Do free VPNs really have no-logs policies?
It is incredibly tempting to open your app store and download the first free VPN you see. However, as a cybersecurity analyst, I constantly remind people of one golden rule of the internet: If you are not paying for the product, you are the product.
Running a global network of highly encrypted, fast servers costs millions of dollars in hardware, bandwidth, and maintenance. When an app claims to offer this entirely for free while also promising a strict no-logs policy, you need to ask yourself a critical question: How are they making money?
Here is the harsh reality of the free VPN business model:
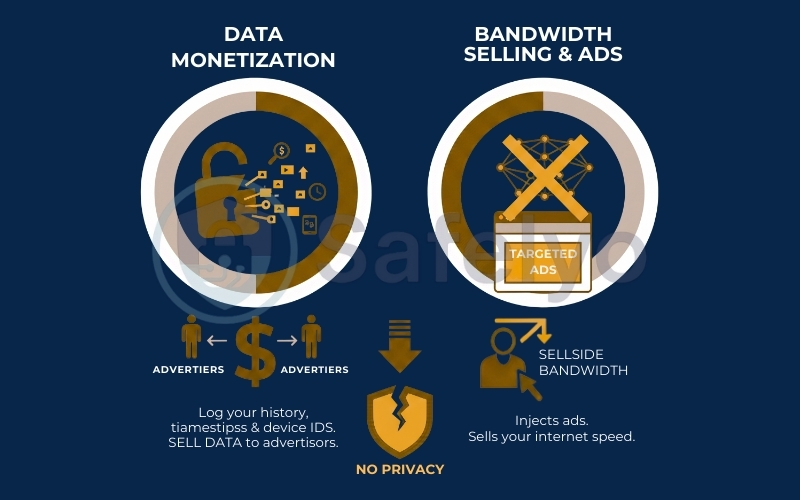
- Data monetization: The vast majority of completely free VPNs survive by secretly acting as data brokers. They aggressively log your browsing history, connection timestamps, and device identifiers, then sell that highly profitable data to third-party advertisers. This entirely defeats the purpose of downloading a privacy tool in the first place.
- Bandwidth selling and ads: In more malicious cases, some shady free apps will inject targeted ads directly into your browser. Some have even been caught selling their free users’ idle bandwidth to other networks.
The freemium exception
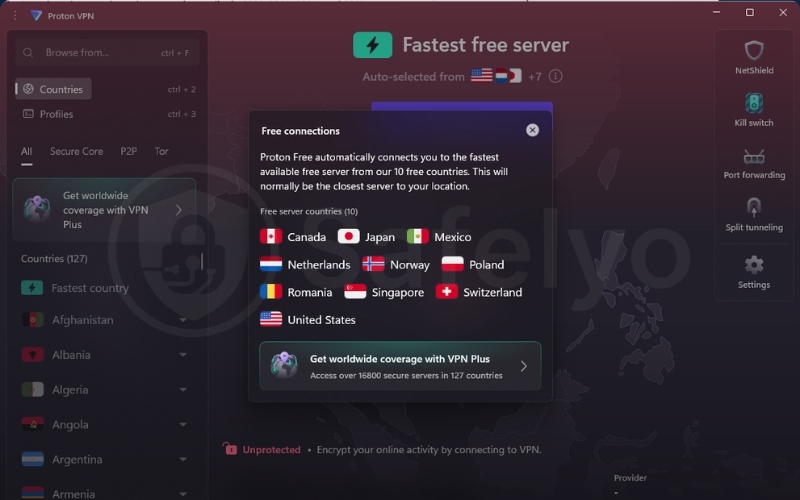
Are there any free VPNs that actually enforce a real no-logs policy? Yes, but only if they follow the “freemium” business model.
A freemium provider is a highly reputable paid service that offers a restricted, free version of its app. Because their premium, paying subscribers cover the massive infrastructure costs, the company has absolutely no financial incentive to sell your data.
For example, the Proton VPN free tier restricts your server choices and does not support advanced features. However, it strictly enforces the same audited no-logs policy as its paid counterpart. Ultimately, unless a free VPN is financially backed by a massive, paid subscriber base, you should safely assume they are logging your every move.
>> Read more details in the Proton VPN review: A suite of end-to-end encrypted services
11. Are no-logs VPNs truly anonymous?
I hate to be the bearer of bad news, but as a privacy advocate, I need to make a very clear distinction: No-logs does not mean invisible. A strict no-logs policy is a phenomenal privacy feature, but it does not magically grant you 100% absolute anonymity on the internet.
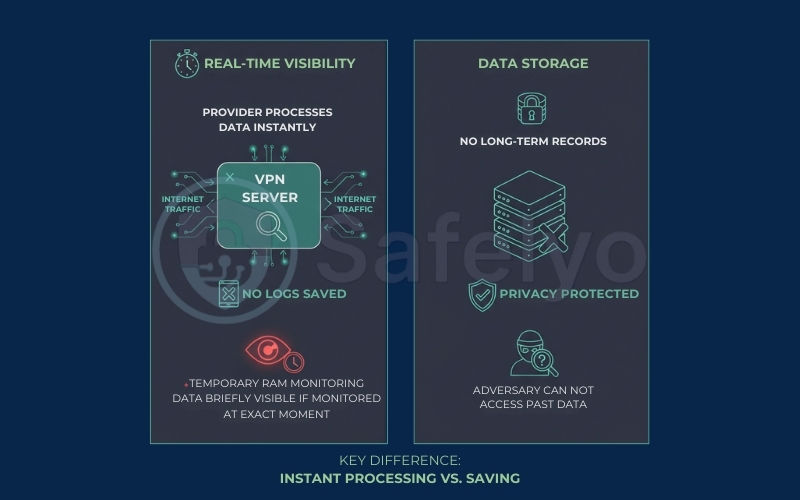
To understand why, we have to look at the crucial difference between real-time visibility and storage. When you connect to a VPN server, the provider must process your internet traffic in real-time to route it to the correct website. They have to see the data packets to move them; they just actively choose not to hit the “save” button. If a highly advanced adversary were actively monitoring that specific server’s RAM at the exact millisecond you clicked a link, your traffic would temporarily be visible.
Furthermore, the biggest threat to your anonymity usually happens before you even connect to a server. When you sign up for a premium service, you inevitably leave a digital paper trail:
- The email requirement: Most average users sign up using their primary, personal email address. Right away, your real identity is directly tied to the creation of your VPN account.
- Payment tracking: If you pay for your subscription using a personal credit card or PayPal, your bank creates a permanent, undeniable financial record that you purchased a specific privacy tool.
If you want to move past basic privacy and achieve genuine, untraceable anonymity, you have to change how you buy the service. True privacy purists bridge this gap by signing up with a disposable email (or a secure, encrypted email service) and completely bypassing banks by using a crypto payment method.
>> Check out for: Best free secure email providers (2025): A private alternative to Gmail

Ultimately, a verified no-logs VPN is an incredibly powerful shield against mass surveillance and historical data tracking. It protects your past, but it is not a magical invisibility cloak.
12. How to verify a VPN’s no-logs claim (Checklist)
By now, you understand that trust is good, but verification is better. To help you cut through the marketing noise, I have compiled the exact criteria I use whenever I review a new VPN service.
12.1. The 5-minute no-logs verification table
I call this the “5-Minute Stress Test”. Before you commit to a long-term subscription, run the provider through this quick checklist. If they fail even one of these points, walk away.
| Verification step | What to look for (Pass) | Red flag (Fail) |
| 1. Privacy policy | Explicitly states: “We do not collect IP addresses, timestamps, or session duration”. | Vague phrases like: “We collect metadata to improve user experience”. |
| 2. Audit history | Public report from PwC, Deloitte, or Cure53 within the last 12–24 months. | No audit, or an audit that is 3+ years old. |
| 3. Server tech | RAM-only (diskless) servers that wipe data on reboot. | Standard hard drive servers (HDD/SSD) that store data permanently. |
| 4. Jurisdiction | Privacy-friendly havens (Panama, BVI, Switzerland). | 5 Eyes countries with mandatory data retention laws. |
| 5. Track record | Proven in court or server seizures (e.g., “authorities found no data”). | No history of legal challenges or a history of handing over logs. |
12.2. Step-by-step guide
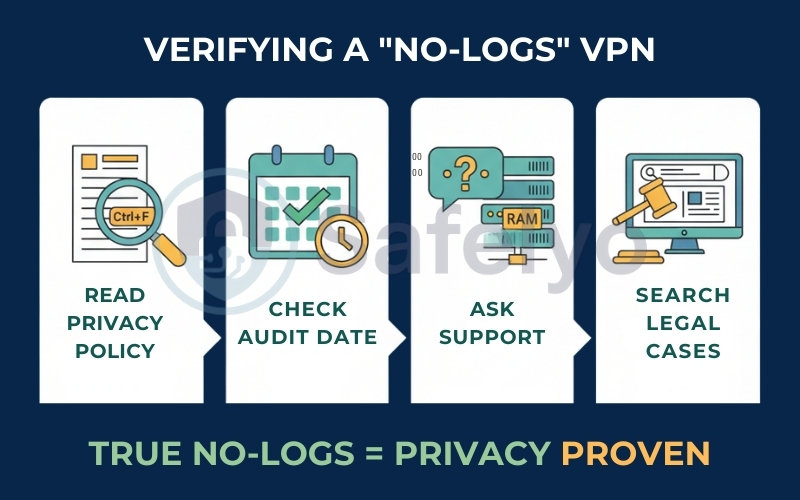
If you want to be thorough, here is how to manually verify the details from the table above:
- Read the actual privacy policy (Ctrl+F is your friend): Ignore the flashy homepage banners. Go straight to the footer, open the privacy policy, and search for keywords like “IP address” and “timestamps”. If the text admits to storing connection logs for an “indefinite period”, they are not a true no-logs VPN.
- Verify the audit date: A security audit from 2019 is ancient history in the tech world. You need recent proof. If a provider hasn’t been audited in the last two years, their infrastructure might have changed without anyone noticing.
- Ask support the hard questions: Open their live chat and ask directly: “Do your servers run on hard drives or RAM?” If the support agent gives you a vague answer or cannot confirm diskless infrastructure, it usually means they are running on cheaper, less secure technology.
- Search for real-world legal cases: Open Google and search for “[VPN Name] court case logs” or “[VPN Name] server seizure”. The best providers will have news stories confirming they refused data requests because they had nothing to show.
13. FAQs about no-logs policies
Here are the most common questions I receive regarding VPN logging practices, simplified for clarity.
What is a no-logs policy?
A no-logs policy is a commitment from a VPN provider. It means they do not collect, store, or share your browsing activity, such as visited websites and DNS queries. It also includes connection metadata, like your original IP address and timestamps. Essentially, they cannot hand over data about your online actions because they never recorded it in the first place.
Is a “zero-logs” policy the same as a “no-logs” policy?
Practically, yes. “Zero-logs” is largely a marketing term used to sound more secure. However, technically speaking, no VPN can run with literally zero logs; they must keep basic account data (email, subscription status) to process payments. The correct industry term is a “strict no-logs policy”, which refers specifically to user activity and identifiable connection data.
Can a VPN with a no-logs policy still see my traffic?
Yes, but only in real-time. To route your data to a website, the VPN server must momentarily process your traffic in its RAM (Random Access Memory). However, a true no-logs provider configures their servers to wipe this data instantly after the packet is forwarded. They see the stream as it flows, but they do not record it to a storage drive.
Which VPNs have a proven no-log policy?
While many claim to be no-logs, only a few have proven it via independent audits or real-world legal challenges. Notable examples include ExpressVPN (verified by a server seizure in Turkey and PwC/KPMG audits), NordVPN (verified by multiple PwC/Deloitte audits), and Private Internet Access (PIA) (verified in court twice).
Does NordVPN have a no-logs policy?
Yes. NordVPN has undergone multiple independent assurance engagements by PricewaterhouseCoopers (PwC) and Deloitte to verify its no-logs statement. They also operate on RAM-only servers, meaning no data is permanently stored on hard drives.
What is VPN jurisdiction, and why does it matter?
Jurisdiction refers to the country where the VPN company is legally headquartered. It matters because local laws dictate whether a government can force the company to start logging users. Privacy experts prefer VPNs based in Panama, the British Virgin Islands, or Switzerland, which fall outside the Five Eyes intelligence alliance and have no mandatory data retention laws.
Is using a VPN illegal in the US?
No. Using a VPN is 100% legal in the United States and most other countries. You have the right to protect your privacy. However, using a VPN to commit crimes (like copyright infringement, hacking, or buying illegal goods) remains illegal, and you can still be prosecuted if caught through other means.
Can police track me if I use a no-logs VPN?
If the VPN is truly no-logs and uses shared IP addresses, it is extremely difficult for police to track your specific activity. The police (via your ISP) can see that you are connected to a VPN server, but they cannot see what you are doing inside that encrypted tunnel. If they raid the VPN server, a no-logs policy ensures there is no historical data to link your identity to your browsing history.
14. Conclusion
Ultimately, a no-logs policy is the single most critical feature separating a genuine privacy tool from a digital trap. As we have explored, simply seeing “Zero Logs” on a website banner is never enough. In an industry filled with marketing fluff, your security depends entirely on technical reality: RAM-only servers, independent audits, and a proven legal track record.
Here at Safelyo, we believe that trust must be earned, not given. When you choose a VPN, you are entrusting a company with your most sensitive personal data. Always demand evidence before you hand over your credit card.
If you are ready to find a provider that actually passes the “5-Minute Stress Test,” check out our other in-depth articles in the VPN Guides category. If you want to understand more about encryption protocols and security features, those resources will be helpful. Your digital privacy is worth the extra homework.