Wondering exactly what is obfuscated VPN? An obfuscated VPN is a specialized privacy feature that strips identifiable metadata from your connection, making your encrypted data look exactly like normal internet browsing.
If your standard secure tunnel keeps getting disconnected on public Wi-Fi or restricted networks, an obfuscated VPN is the exact solution you need to bypass network filters.
In this guide, we explain how an obfuscated server outsmarts Deep Packet Inspection, explore four everyday situations where you absolutely need it, and show you how to enable it effortlessly.
Key takeaways:
- VPN obfuscation hides VPN usage from internet service providers, firewalls, and network administrators.
- Obfuscated servers remove VPN protocol signatures from data packets, utilizing advanced techniques like Obfsproxy and Stunnel.
- Core use cases: censorship bypass, restricted office/school networks, ISP throttling prevention, and evading government tracking.
- Not recommended for everyday use: It carries a minor speed overhead of 11% to 44%.
1. What is an obfuscated VPN (and obfuscated server)?
An obfuscated VPN is a virtual private network (VPN) equipped with a feature designed to strip VPN metadata from data packets, making the traffic look exactly like normal HTTPS web browsing. The primary job of an obfuscated VPN is to conceal your entire protective tunnel from being identified as a VPN connection.
We often see this feature referred to as stealth VPN, camouflage mode, or scrambled servers depending on the provider you choose.
An obfuscated server is simply a specialized VPN server configured specifically to perform this obfuscation process. To understand how this works, we must differentiate between two distinct layers of protection. Encryption protects the actual contents of your traffic so no one can read your data. Obfuscation disguises the identity of the traffic itself so outside observers cannot tell you are using a secure tunnel.
The ultimate goal of an obfuscated VPN is to bypass advanced network filtering systems that rely on Deep Packet Inspection (DPI). DPI is an analytical tool used by firewalls to scan the structure of incoming data and block anything carrying a VPN signature. By making your VPN connection look like standard web traffic, obfuscation neutralizes DPI entirely.
2. How does VPN obfuscation work?
VPN obfuscation works by altering the signature or fingerprint of your data packets so that automated systems can no longer recognize the traffic as coming from a VPN protocol. While the engineering behind it is complex, the concepts are quite straightforward.
2.1. How your ISP detects that you’re using a VPN
Before exploring obfuscation techniques, we must understand exactly how your Internet Service Provider (ISP) recognizes your virtual private network in the first place. VPN traffic generates specific data patterns that look completely different from standard HTTPS browsing. ISPs typically detect VPN usage through three primary methods:
- Checking port patterns: Standard VPN protocols use highly recognizable ports, such as UDP 1194 for OpenVPN.
- Monitoring unencrypted handshakes: During the initial connection phase, VPNs initiate unencrypted handshakes that monitoring systems can easily flag.
- Using Deep Packet Inspection: Network administrators deploy Deep Packet Inspection to scan the actual packet headers for known VPN fingerprints.
Additionally, some firewalls simply maintain an IP blacklist of known VPN server addresses to block connections regardless of the traffic pattern.
2.2. Obfuscation techniques: XOR Scramble, Stunnel, Shadowsocks, Obfsproxy, SSH
Providers use several distinct techniques to modify your data packets and evade detection.
- XOR Scramble (OpenVPN Scramble): This method applies a simple XOR bitwise operation to the OpenVPN packet signature. The process scrambles the metadata enough so that Deep Packet Inspection cannot recognize it, making it a fast option for basic network restrictions.
- Stunnel (SSL/TLS wrapping): This technique wraps your entire VPN connection inside an additional layer of SSL/TLS encryption. Because SSL/TLS is the standard encryption used by regular HTTPS websites, your traffic blends in perfectly with normal secure web browsing.
- Shadowsocks: This is an encrypted SOCKS5 proxy protocol originally created to bypass the Great Firewall of China. Shadowsocks acts as a highly effective proxy rather than a full VPN protocol, focusing purely on lightweight traffic disguise.
- Obfsproxy: Developed by the Tor Project, Obfsproxy is an open-source tool that changes the structural appearance of data completely to bypass censorship. Several commercial VPN providers integrate Obfsproxy to strengthen their stealth capabilities.
- SSH tunneling: This technique hides your VPN traffic inside an SSH tunnel using port 22. While less common in consumer VPN applications, SSH tunneling proves highly effective against exceptionally strict firewall rules.
3. Can an obfuscated VPN still be detected?
The ability to detect an obfuscated VPN depends entirely on the specific detection methods being used by the network administrator. Obfuscation successfully neutralizes automated Deep Packet Inspection and port-blocking firewalls.
However, obfuscation cannot bypass an IP blacklist. If a website or service maintains a database of known VPN IP addresses, they will still see that your traffic originates from a restricted server IP. This is why obfuscated servers often fail to unblock streaming platforms that rely heavily on IP blacklisting rather than traffic analysis.
Furthermore, if a network administrator performs manual packet inspection rather than relying on automated scans, they might still identify anomalies in your connection. Advanced artificial intelligence systems are also developing sophisticated traffic fingerprinting techniques that analyze timing and packet size to guess VPN usage. Ultimately, obfuscation is incredibly effective against standard automated firewalls but still carries risks against manual inspection or IP blocking.
4. 4 situations where you need an obfuscated VPN
While a standard VPN is perfect for everyday privacy, obfuscation becomes essential in specific situations where your connection itself is under scrutiny. Here are the four most common scenarios where we highly recommend activating this feature.
4.1. Bypassing internet censorship and government firewalls
Strict internet censorship systems actively deploy DPI to identify and block standard VPN connections. Countries like China (using the Great Firewall of China), Iran, and Russia rely on these deep scans to cut off access to global news sites and social media platforms.
For journalists, activists, researchers, and travelers in these regions, an obfuscated server provides a critical lifeline. A standard VPN will fail immediately because the firewall detects the protocol signature at the port level. By utilizing obfuscation, users can bypass government firewalls and maintain access to the open internet. We note that users must choose a provider that constantly updates its obfuscation methods, as governments continuously upgrade their detection capabilities.
4.2. Evading VPN blocks on school and office networks
If your VPN fails to connect on a company or university Wi-Fi network, the cause is usually intentional VPN port blocking. Network administrators frequently block specific ports, such as UDP 1194 for OpenVPN or ports 500 and 4500 for IKEv2, to enforce strict local content filters.
Obfuscation solves this problem by disguising your traffic as standard HTTPS web traffic routed through port 443. Since blocking port 443 would break the entire internet for the organization, your disguised VPN traffic slips right through. We always recommend pairing this feature with a Kill Switch to ensure your true IP address remains hidden if the obfuscated connection drops unexpectedly.
4.3. Preventing ISP throttling and surveillance
Even in regions with open internet access, your internet service provider might monitor your traffic patterns and intentionally slow down your speeds. ISPs frequently use traffic-based throttling when they detect high-bandwidth activities running through a VPN.
By hiding your VPN usage, obfuscation prevents your ISP from identifying the nature of your traffic. The ISP only sees a generic stream of HTTPS data, leaving them with no specific trigger to throttle your connection. However, we must point out a critical limitation. If your ISP applies bandwidth throttling based on your total monthly data quota, obfuscation will not help you regain speed.
4.4. Hiding VPN usage from government tracking
Hiding your activity from government surveillance is a distinctly different threat model than simply bypassing blocked content. Some governments do not just block websites; they actively conduct VPN usage logging to track which citizens are attempting to use privacy tools.
Obfuscation prevents government surveillance systems from knowing that an individual is using a VPN at all. This protection is vital for whistleblowers and activists operating in heavily monitored environments. While bypassing censorship focuses on unlocking websites, this specific use case focuses purely on concealing your behavioral footprint to avoid suspicion.
5. When you do NOT need an obfuscated VPN
Obfuscation is not a feature you should leave turned on constantly. Here are three common situations where a standard VPN connection is the better choice:
- Streaming your favorite movies and shows: Platforms like Netflix block VPNs via an IP blacklist rather than Deep Packet Inspection. Obfuscation cannot bypass an IP blacklist. You simply need a standard server with a clean, unrecognized IP address to stream content successfully.
- Browsing securely at your own home: Your home internet service provider rarely blocks standard VPN ports. Unless you actively experience targeted speed throttling, standard encryption provides complete privacy without any speed penalty.
- Using basic public Wi-Fi at a cafe: If you want to protect your passwords at a local coffee shop, a regular VPN is perfectly safe. Local cafes do not deploy enterprise-grade Deep Packet Inspection to block privacy tools.
6. Obfuscated VPN vs. Double VPN: What’s the difference?
Users frequently confuse these two advanced features, but they solve entirely different privacy problems. An obfuscated VPN hides the fact that you are using a secure tunnel, whereas a Double VPN adds an extra layer of encryption without hiding the tunnel itself.
| Feature | Obfuscated VPN | Double VPN (Multi-hop) |
| Primary Goal | Hides the fact that you are using a VPN from ISPs. | Adds a second layer of encryption for maximum anonymity. |
| Server Routing | Traffic passes through 1 specialized server. | Traffic passes through 2 separate VPN servers consecutively. |
| Hides VPN Usage? | Yes. Traffic looks like normal HTTPS. | No. Your ISP can clearly see you are using a VPN. |
| Speed Impact | Moderate speed drop. | Heavy speed drop due to double routing. |
| Best Use Case | Bypassing strict network blocks and censorship. | Protecting highly sensitive data when VPN usage is allowed. |
According to information from Surfshark, you can actually combine both features if your provider supports it. We advise using obfuscated servers when your network blocks your connection, and relying on Double VPN when you need maximum anonymity on an unrestricted network.
7. Is using an obfuscated VPN legal?
In the vast majority of countries, using an obfuscated VPN is completely legal. Obfuscation is simply an advanced technical feature of a standard privacy tool. If VPNs are legal in your jurisdiction, obfuscated servers are legal as well.
However, there are notable exceptions. In countries that ban or heavily restrict VPN usage entirely (such as China, North Korea, Belarus, Turkmenistan, and Iraq), using any VPN feature sits in a legal gray area or is explicitly illegal.
Additionally, using these servers to access certain platforms might constitute a Terms of Service violation. Streaming platforms often prohibit the use of proxies in their user agreements, which could result in an account suspension if detected. Crucially, any illegal online activity remains illegal regardless of whether you use an obfuscated VPN to hide your identity.
8. Benefits and drawbacks of VPN obfuscation
Understanding the exact trade-offs of this digital disguise helps you decide when to activate it.
Pros
Bypasses strict censorship and network blocks.
Hides your VPN usage from ISPs and network administrators.
Helps avoid targeted, traffic-based speed throttling.
Cons
Causes a speed drop of 11% to 44%.
Protocol limitation (often restricts you to OpenVPN).
Not offered by all VPN providers or on all servers.
Based on our testing data and industry benchmarks, the most significant drawback is the undeniable performance hit. Applying an extra processing layer to scramble data packets causes an average speed drop of 11% to 44%, depending on your proximity to the server. Because obfuscation usually requires the heavier OpenVPN protocol rather than faster alternatives like WireGuard, we always recommend disabling the feature when you return to an unrestricted network.
9. Best VPNs with obfuscation in 2026
Selecting a provider with reliable stealth capabilities requires looking for dedicated servers, robust protocol support, and consistent updates. Based on our evaluations, here are the top providers offering robust obfuscation features:
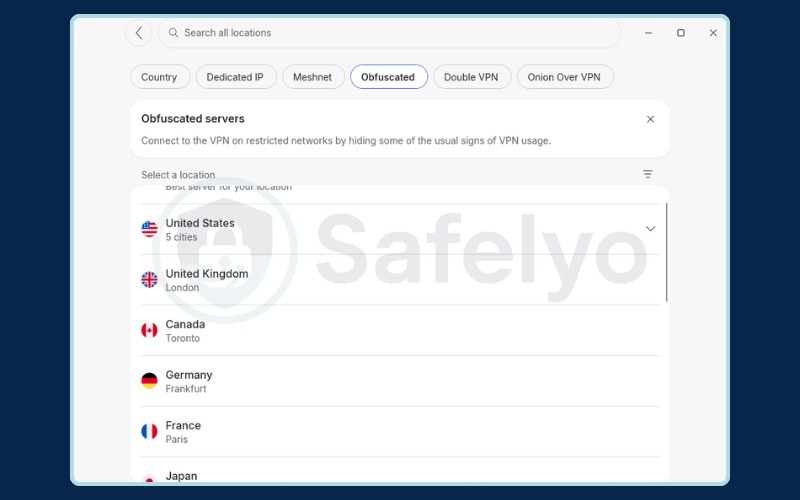
- NordVPN: NordVPN offers dedicated obfuscated servers located in its Specialty Servers menu. You must select the OpenVPN protocol manually on some devices to make these servers appear.
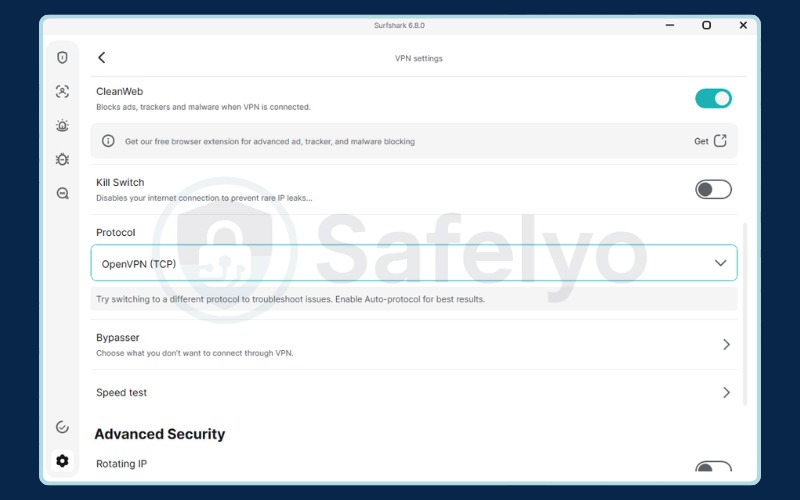
- Surfshark: Surfshark provides an automatic stealth feature called Camouflage Mode. You simply need to switch your protocol to OpenVPN, and the application applies the obfuscation automatically without requiring you to pick a specific server.
- ExpressVPN: ExpressVPN builds obfuscation directly into its proprietary Lightway protocol. The application detects restricted networks and applies the digital disguise automatically, requiring zero manual configuration from the user.
- Mullvad: While less heavily marketed, Mullvad offers powerful obfuscation through Shadowsocks and its custom Daita feature. This provider caters excellently to users who want deep, technical control over their stealth settings.
When choosing your service, prioritize providers that actively update their stealth mechanisms to outsmart continuously evolving censorship firewalls.
10. How to enable obfuscation on your VPN
Activating obfuscation does not require great technical skills. All major providers integrate a simple toggle or automatic protocol selection directly within their applications. The only universal prerequisite is ensuring you have selected the correct protocol to support the feature.
10.1. How to enable obfuscated servers on NordVPN, Surfshark & ExpressVPN
How to enable obfuscated servers on NordVPN:
- Open the NordVPN application and navigate to Settings.
- Change your Protocol to OpenVPN (TCP or UDP). The Windows application typically selects this automatically when you toggle the obfuscation feature.
- Return to the main server screen, open the All location list, and click Obfuscated.
We strongly advise turning on the Kill Switch simultaneously to prevent IP leaks if your connection drops.
How to enable obfuscated servers on Surfshark:
- Open the Surfshark application and click on VPN Settings.
- Navigate to the Protocol selection menu.
- Choose OpenVPN (TCP or UDP). Surfshark automatically applies its Camouflage Mode whenever you use OpenVPN, meaning no further steps are necessary.
Please note that while this process works natively on Windows, Linux, Android, and iOS, macOS users will need to configure OpenVPN manually following the provider’s documentation.
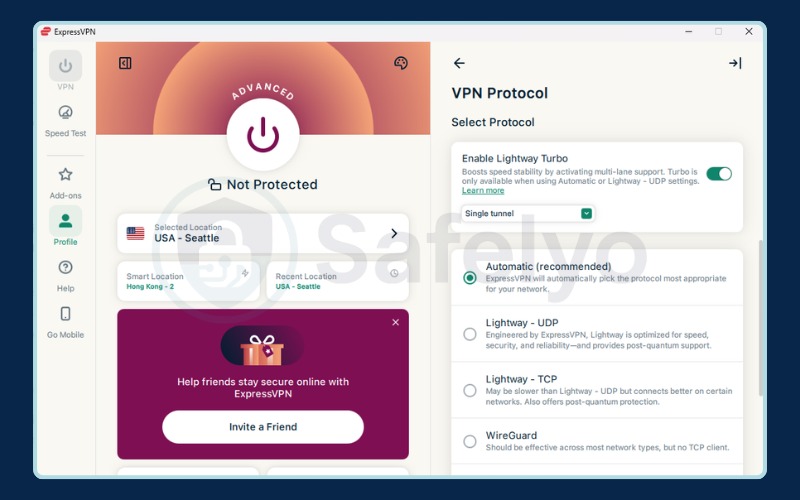
How to enable obfuscated servers on ExpressVPN:
- Open the ExpressVPN application and leave the protocol set to Automatic or select the Lightway protocol.
- Connect to any server. ExpressVPN deploys obfuscation automatically in the background whenever it detects a restrictive network.
- If you face issues, you can manually select OpenVPN in the Profile > VPN Protocol menu, as ExpressVPN also supports obfuscation on specific OpenVPN servers.
10.2. How to enable obfuscation on mobile
On mobile devices, the activation process mirrors the desktop experience, though you should be aware of a few platform-specific nuances.
iPhone (iOS):
- NordVPN: Go to Settings > Protocol > OpenVPN (TCP or UDP), then return to the main screen and tap All locations > Obfuscated.
- Surfshark: Navigate to VPN Settings > Protocol > OpenVPN. The obfuscation applies automatically.
- ExpressVPN: The default Lightway protocol handles obfuscation automatically without any manual toggles.
Due to Apple’s strict Network Extension guidelines, iOS applications sometimes offer fewer manual server selection choices compared to their desktop counterparts.
Android:
- NordVPN: The process is identical to iOS. Set the protocol to OpenVPN in Settings, then select Obfuscated.
- Surfshark: Open VPN Settings, select OpenVPN as your protocol, and connect normally.
- ExpressVPN: Rely on the Lightway protocol for automatic stealth protection.
Android generally offers more flexibility, allowing users to import manual OpenVPN configuration files if the main application is entirely blocked from downloading.
Overall, mobile VPN applications handle stealth connections with excellent stability, even if they feature slightly simplified interfaces.
11. Troubleshooting: Obfuscated servers not working
If your obfuscated servers refuse to connect, it is normal to feel anxious about your privacy. The problem usually stems from one of the following configuration errors or network updates.
| Common Cause | How to Fix the Issue |
| You are using the wrong protocol (like WireGuard or IKEv2). | Open your settings and switch the protocol to OpenVPN (TCP or UDP). |
| The specific server is overloaded or recently blocked. | Disconnect completely and choose an obfuscated server located in a different country. |
| Your application version is outdated. | Update your VPN application to receive the latest stealth mechanism patches. |
| The local firewall recently updated its detection methods. | Contact your provider’s support team for fresh server IPs, or switch to a Shadowsocks proxy if available. |
| A triggered Kill Switch is blocking all traffic. | Temporarily disable the Kill Switch, establish the connection, and immediately turn it back on. |
We must note that not every provider deploys obfuscation on every single server in their network. Always verify that you are connecting to a supported location. If you continually face blocks after trying these fixes, we recommend switching to a provider renowned for heavier stealth capabilities, such as Mullvad with its Shadowsocks and DAITA integration.
12. FAQs about Obfuscated Server
What does an obfuscated server do?
Obfuscated servers disguise your VPN traffic as regular HTTPS web browsing. This prevents internet service providers and firewalls from detecting your VPN usage through Deep Packet Inspection.
Does obfuscated VPN help with Netflix?
Generally, no. Netflix restricts access by maintaining an IP blacklist of known server addresses rather than analyzing the type of traffic via Deep Packet Inspection. Obfuscation cannot bypass an IP blacklist, so you simply need to connect to a standard server equipped with a clean IP address.
Are obfuscated servers safe?
Yes, they are completely safe. Obfuscated servers maintain the exact same military-grade AES-256 encryption as standard servers. The obfuscation process merely alters how the traffic looks to outside observers without compromising the security of the data inside the tunnel.
Is there a free obfuscated VPN?
Finding a reliable free obfuscated VPN is extremely rare because maintaining stealth servers requires significant financial and technical resources. While Windscribe offers a limited free tier that includes some stealth capabilities, we strongly recommend using a premium provider for consistent, secure obfuscation.
Should I always use an obfuscated VPN?
Not necessarily. You should enable obfuscation when you’re in a country with heavy internet censorship, or if your school or workplace network actively blocks standard VPNs. For everyday activities like securing your connection on public Wi-Fi or unblocking streaming sites in a free country, a standard VPN connection is usually faster and perfectly sufficient.
Is a stealth VPN the same as an obfuscated VPN?
Yes, “stealth VPN” is another common term for an obfuscated VPN. They both refer to the same technology used to disguise your VPN traffic and make it undetectable. The goal is to put your VPN connection into “stealth mode” to avoid detection and blocking.
Is an obfuscated VPN slower?
Yes, typically an obfuscated VPN is slightly slower than a standard VPN connection. The extra process of disguising the VPN traffic requires additional processing power, which can lead to a minor reduction in your overall internet speed.
What is the difference between obfuscated and Double VPN?
They solve different problems. Obfuscation disguises your VPN traffic to hide the fact you are using a VPN. Double VPN (or Multi-Hop) routes your traffic through two different VPN servers for an extra layer of encryption and security. Use obfuscation to bypass blocks; use Double VPN when your top priority is maximizing anonymity.
Which VPN protocols support obfuscation?
OpenVPN is the standard protocol that supports the obfuscation feature best. Its structure allows providers to easily integrate data-scrambling methods.
WireGuard does not support obfuscation natively due to its static code design. VPN providers must develop their own proprietary programming tools to hide WireGuard traffic successfully.
Can obfuscation bypass the Great Firewall of China in 2026?
Yes, but the results are not absolutely guaranteed. Today, national firewalls use machine learning algorithms to scan network traffic continuously.
These systems analyze data volume and response times to detect hidden packets. You must use VPN services that continuously upgrade their encryption technology to maintain a stable connection.
Does an obfuscated VPN hide my activity from local network admins?
Yes. The obfuscation technology wraps your data inside a standard SSL/TLS encryption layer.
The network system at your school or company will record this as normal HTTPS web traffic. Because of this, network administrators cannot determine that you are running VPN software on your device.
13. Conclusion
Ultimately, understanding exactly what is obfuscated VPN provides you with an essential layer of protection for navigating restrictive network environments. By wrapping your encrypted data to look like standard web traffic, this feature ensures that network administrators, internet service providers, and strict government firewalls cannot detect or block your secure tunnel.
We always advise applying this tool thoughtfully. You should turn it on when you face aggressive censorship, strict office firewalls, or deliberate ISP throttling. However, you should disable it during normal home browsing to avoid the unnecessary speed drop that comes with the extra processing layer.
If you are eager to take full control of your digital privacy and explore more advanced security setups, we encourage you to check out our comprehensive VPN Guides on Safelyo.